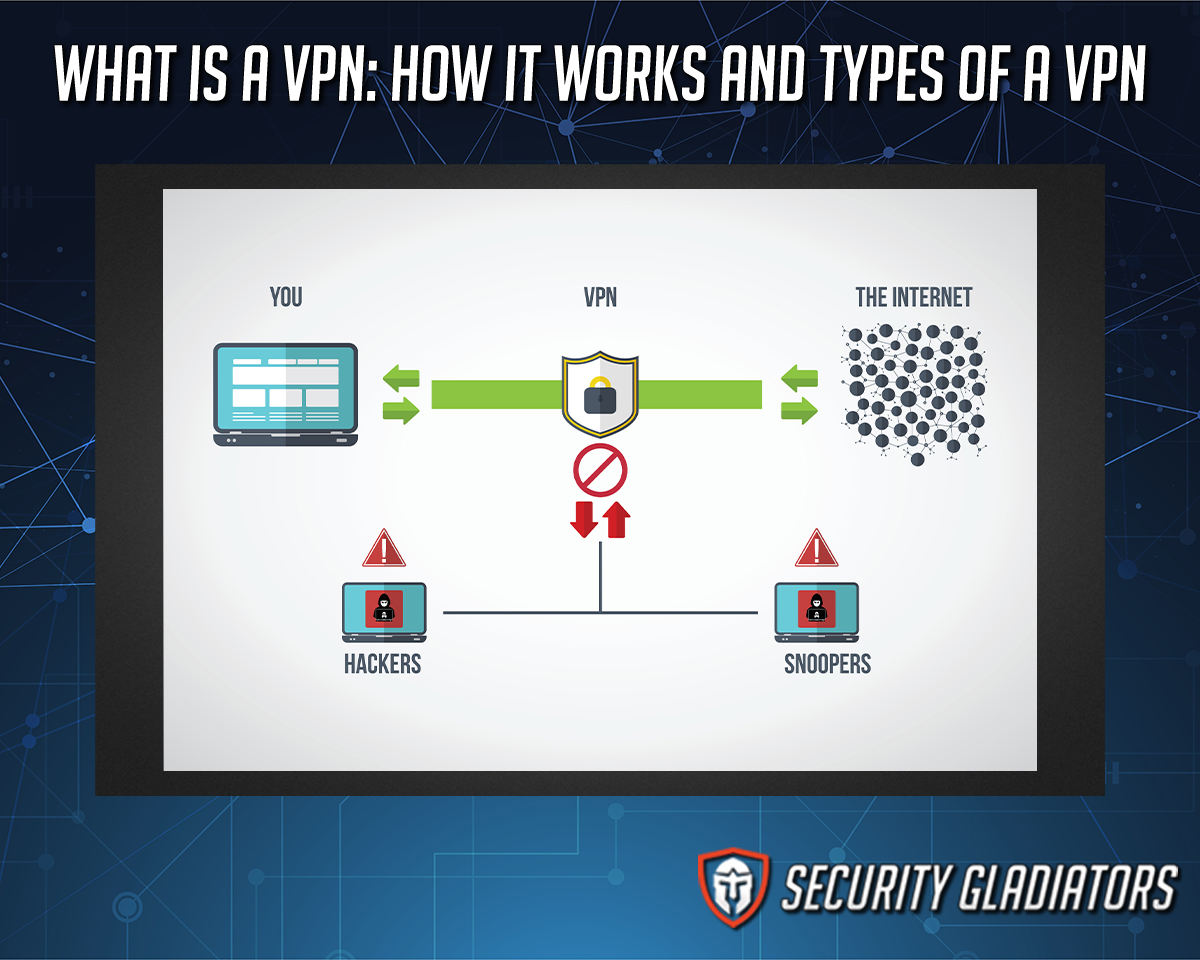
A VPN or Virtual Private Network is an encrypted connection that exists between a device and a network over the internet.
VPN services have become very important in the past couple of decades because of an increased number of government-run surveillance programs and mass data collection by technology companies. To enhance internet security and privacy, people today use VPNs.
The total VPN market is estimated to exceed $107.5 billion within the next 10 years. In 2020 alone VPN usage increased by 27 percent. This surge in popularity has been attributed by some to an increase in remote working. Alternative reasons may include an increase in data mining processes as well as the collection of personal data by technology companies to feed machine learning algorithms.
Gurdeep Singh-Pall developed the PPTP protocol in 1996 while working for Microsoft. It took another three years before the protocol was published but since then, VPNs have evolved to a great extent.
Table of Contents
What are the Benefits of a VPN?
These are the top benefits of using a VPN service:
- Secure public WiFi networks whenever there is a need to connect to one at a location like a cafe or local library
- Stream geo-restricted content from various streaming websites such as Amazon Prime Video and Netflix
- Bypass internet censorship in any country of the world
- Stop internet service providers from activities such as surveillance and tracking
- Avoid price discrimination in some regions. Turning on a VPN service to change location to a place with the lowest prices can result in huge savings
- Secure banking activities that require extra security. A lot of banks still make use of unsecured networks to carry out transactions. The best way to counter that is to use a VPN
- Stop hackers from stealing payment details while shopping online
What is a VPN Used For?
These are the top activities VPNs are used for:
- To stay anonymous on the internet
- To secure internet traffic against hacking attempts that make use of techniques such as MiTM and phishing
- Connecting to an office network that may be located in a different building
- Journalists use VPNs to receive anonymous tips
- Change the IP address to access different content
What is the Best VPN?

The best VPN is the one that is best suited to the needs of the user. Therefore, it is essential to know the reason the VPN has been purchased. For example, customers looking to protect the whole household should go with one that offers the most simultaneous connections.
For streaming movies, look for a VPN that offers fast servers, unlimited bandwidth, and lots of servers. Travelers should go with one that offers the most security features and has servers in lots of countries.
Casual online users who only want to surf the internet uninterrupted by geo-restrictions and hyper-targeted content will want to go for a VPN candidate that offers the most locations and servers. Encryption standards and security protocols are less important to such users.

Another way to pick the best VPN is to see its supported platforms. The best VPNs support all major platforms such as iOS, Linux, Android, Mac, and Windows.
Some VPNs allow router installation which can protect each and every device in a given range.
Looking at the VPN apps on offer is another way to pick the best VPN. Good VPNs offer a simple installation process and a clean user interface.
Top-quality VPNs not only work in commonly covered regions such as the US and the UK but also in remote locations such as those in China and Iran.
The best VPNs can be expensive. Price is therefore a huge factor in determining which VPN is the best for a given list of needs. This is where subscription length and payment methods such as cryptocurrency and debit cards come into the equation. The best VPNs offer the most flexibility and choice. A lengthy money-back guarantee is a great way to sign up for the best VPN. The longer it is, the better the overall deal.
This is important:
Privacy conscious users should give a thorough read to the privacy policy document of the VPN they are interested in. The privacy policy document will usually describe in detail the kind of data the VPN service collects and stores.Similarly, the geographic location of the VPN service and where the VPN service operates is also very important for people who care about their privacy. The way to choose the best VPN in this regard is to go with one that isn’t located in the US or the EU and has a zero-logs policy.

Another way to select the best VPN is to look at the level of encryption the VPN service in question offers. Users should not sign up with a VPN service that offers anything below AES 256-bit encryption. Plenty of VPN services use 126-bit encryption which is not as strong as the former. The best VPNs offer the strongest encryption standards and back them up with strong VPN protocols such as OpenVPN and/or WireGuard.
Finally, customer support. Setting up modern VPNs is a simple procedure but sometimes customer support can make things easier. Look for VPNs that offer multiple methods of communication.
What is a VPN Service?

A VPN service is a tool that provides online users with anonymity and privacy. It does this by generating a mini private network from a much larger public internet network. The primary feature of any given VPN service is its ability to mask the user’s internet protocol address, leaving user activities untraceable.
Different VPNs focus on different aspects of online privacy and anonymity. Some focus on ease of use while others focus on security. Some concentrate on price (some VPNs are free while others charge a premium) and a few focus on unblocking geo-restricted content.
For more information on how does a VPN server work refer to this guide.
Is there free VPN Service?
Yes. The VPN market does offer free options for consumers looking to try things out before spending their money, as well as those simply keeping to a budget. Free VPNs do however usually come with restrictions on bandwidth and usage. They also have fewer security tools and server locations.
With this said, there are some VPN services that are free and operate ethically. Such free VPNs have no involvement in deceiving the user by selling data or hiding their logging activities. Finding the best free VPN services in today’s market is a difficult process though.
What is a VPN Kill Switch?

A VPN Kill Switch disconnects users from the internet the moment a VPN connection drops. The major benefit of a VPN Kill Switch feature is that it stops information and IP leakage if a VPN stops working suddenly for some reason.
Pre 2010, a VPN Kill Switch feature came only as a luxury feature but recently has become a necessity because of the increased sensitivity of the work that journalists, activists, P2P users, whistleblowers, and torrent users do regularly.
Does VPN Work on Phones and Mobile Devices?
Yes. VPNs do work on mobile devices and various phones. Plenty of VPNs come with dedicated apps for Android and iOS platforms. In addition to those, some VPNs also support FireStick and Blackberry devices. Usually, the official website of a given VPN makes it clear which platforms they support.
What is the Difference Between IOS and Android VPN Services?
These are the major differences between Android VPN and iOS VPN services.
- The main difference is that the best iOS VPN services don’t work on Android devices and the best Android VPN services don’t work on iOS devices
- iOS VPNs usually support fewer protocols because of iOS restrictions. Android VPNs are much more fleshed out because of the permissions the Android operating system grants to any app by default.
- iOS VPNs are generally more secure because of the closed nature of the iOS itself. Android VPNs, again because of the nature of the Android operating system, have a harder time containing information from being leaked.
What are the Disadvantages of VPN?
These are the major negative points of VPN services:
- Since a VPN has to encrypt and reroute internet traffic, it decreases connection speed.
- Some streaming services like Netflix and Amazon ban people who use VPNs so there is always a risk of permanently losing access to these services.
- A few countries, like China and Iran, have banned unapproved VPN services. Depending on the location VPN usage may or may not be legal.
- Consumers have no other option but to trust VPNs on features such as encryption and zero-logs policy. In the end, a VPN may or may not provide protection.
- Some VPNs sell user data which defeats the purpose of using a VPN. The potential logging and reselling of user data is a major disadvantage of using a VPN.
- VPN connections can drop at any time which can lead to data leaks in the absence of a Kill Switch feature.
- VPN services can give a false sense of security if the user does not take appropriate precautions in addition to using a VPN. Clicking on a malicious link will lead to problems whether or not there is a VPN in place.
Does VPN Connection Make Internet Slower?

Generally, VPN connections do reduce internet speeds. VPNs decrease download and upload speeds since the service has to encrypt and re-route data which, compared to a vanilla connection with no security, makes VPN connections slower. Connecting to remote servers and encrypting internet data is how VPNs function. Without these processes, they wouldn’t work. Premium VPNs can, however, diminish the effect a VPN has on internet speed with the help of VPN servers.
How Does a VPN Modify Internet Connection?
The steps that explain how a VPN modifies an internet connection are listed below.
Here are the steps that are completed every time a VPN modifies an internet connection (the previous discussion on how does an internet connection work when there is a VPN involved shows the user’s connection changes significantly).
- A VPN connects the user through the user’s preferred VPN server to the internet.
- The user’s data travels through an encrypted VPN tunnel towards the VPN server.
- The VPN server then sends the data to its final destination. This changes the IP address of the user.
Because of this, the data the user’s computer transmits comes out through the VPN server and straight to its final destination rather than from the user’s computer itself.
An easier way to think about VPNs is that they act as intermediaries and connect the user to the larger public internet after hiding the IP address of the user. - Then the user receives the response from the website/app/service accessed.
Note:
VPNs modify internet connection in other ways as well. For example, most VPNs encrypt user data. This means even if a hacker intercepts the VPN tunnel and gains access to the data, the encrypted data would be of little use. Reading encrypted data is close to impossible.How Many Minutes Does it take to Connect a VPN?

In order to connect to a VPN service, a user can take anywhere from 5-15 seconds assuming the VPN app is already installed on the system. The quality, accessibility and responsiveness of VPN can affect the necessary time for connecting the VPN. The server the user connects to and how far it is from the user’s original location is another factor that may increase or decrease connection time. A VPN service can activate more servers to help users to connect faster from different locations on earth.
Finally, the protocol a user connects with also has a bearing on connection time.
How to Find a VPN IP Address?
Here are the steps for finding the IP address of the VPN server connected to:
- Go to here to check the current IP address
- Connect to a VPN server.
- Go to the afore-mentioned sites again and check the new IP address.
- That is the IP address of the server.
Note: VPNs can leak the real IP address of the user in 4 different ways, you should learn more about what is an IP leak so you can test the VPN you are thinking of using.
An advanced method is to go to https://ping.pe.
- Input the IP address that is shown right beneath the input field on the top of the page into the text field on the top of the page after having connected to a VPN server.
- Then click on Go.
- The site will ping the provided IP address from various locations around the globe.
- The lower ping time from different locations will indicate the VPN server being closer to that location.
What is the Onion Over for VPN?

Onion over for VPN is a phrase that describes a scenario where an internet connection has the protection of both Tor and a VPN. Sometimes, services refer to it as Tor over VPN. Onion Over VPN is important for people working in sensitive areas such as journalism, political activism, and others where mistakes can be criminal offenses. Onion over VPN adds an extra layer of security on an internet connection that can further hide internet traffic and machine IP addresses. The major benefit of using Onion over VPN is the inability of a given ISP to see if a given user is using a VPN. Onion over VPN also means even the VPN provider doesn’t get to know which websites the user is visiting. Moreover, Onion over VPN provides access to .onion websites on the dark web.
What is VPN Configuration?

VPN configuration is when the user successfully installs a VPN app on a computer and hence protects the available network. VPN configuration is necessary since without proper configuration the network would not receive the benefits of a VPN service. Modern VPNs only require permissions in the form of VPN configuration as the installation process takes care of everything else. There is no need to spend too much time learning how to configure VPN for other devices. The main benefit of proper VPN configuration is a working VPN connection that hides internet traffic and changes IP address and keeps it that way as long as the user wants.
What is Double VPN?
A double VPN connection means the user’s traffic passes through two VPN servers instead of one. Double VPN connections have become important for people who want more security and an extra layer of anonymity on top of their standard VPN protection. Having a double VPN is also useful for organizations and individuals who regularly transfer important files from one network to another and/or carry out sensitive tasks such as banking and checking health records.
The main benefit of a double VPN connection is that it provides twice the encryption and twice the change of IP addresses relative to a standard VPN. This means it is twice as hard for governments, ISPs, and hackers to track down the VPN user in any way, shape, or form.
What is the VPN Access?

A remote VPN access is a virtual private network that allows online users to securely use and access data and apps remotely. The data is held in a data center or office HQ that is located in a different location to the location of the user. Via VPN Access the data is encrypted while it is sent and received between X and Y. Remote VPN access only happens because of the creation of a virtual tunnel. The tunnel connects the remote user and the website/network/app the user is trying to access. This tunnel is both private and encrypted.VPN access has become very important for users who have to access their organization’s network from public locations. It is also important for data such as patents and formulas that a company may use to gain an edge over the competition. Such data needs protection from potential interception or tamper attempts. VPN access provides that protection.
What are the VPN Types?
VPNs come in different shapes and sizes. Here are the main types of VPNs (VPN types can also mean different protocols of VPN):
- Client-based VPN
- This virtual private network is created between a remote network and a single online user. Most of the time, the user has to use an app to create the network after authenticating the process with a username and password. Generally, the VPN client creates a tunnel, encrypts it, and allows the user to have access to the remote network.
- The main reason why such types of VPNs exist is to make it easy for single users to access private resources from remote locations with nothing but their mobile devices and/or laptops. Another reason is to provide the connection with some form of security.
- Network-based VPN
- These virtual private networks come into existence when two different networks get connected to each other via an untrusted network. The easiest way to understand this type of VPN is to think of different offices that belong to the same company but need to access each other’s networks via IPSec tunnels (for example).

- Network-based VPNs have 3 subtypes.
- The first is IPSec Tunnels. This network-based VPN works similarly to the client-based IPSec tunnel. The difference is that client-based IPSec tunnels target single devices and their traffic patterns while network-based IPSec tunnels are configured to carry an entire networks’ worth of device traffic and thus enable communication between them. This is the main reason why this type of VPN is used is to connect devices from different vendors and networks via the same tunnel.
- The second network-based VPN is DMVPN (Dynamic Multi Point VPN). It takes the concept behind IPSec point-to-point tunnels and expands it to a huge cloud of connected networks. In simpler terms, any network has the ability to communicate with any other network via DMVPN cloud.
- Multinational corporations who want to reduce latency rates between different networks belonging to remote sites have to use DMVPN to connect between networks.
- The final type of network-based VPN is MPLS-based L3VPN.
- The MPLS enables organizations to virtualize their networks. An equipment known as the PE router transfers traffic from a company’s circuit to a VRF or virtual route forwarding in a WAN circuit. The CRF is unique to the company involved. Then the PE forwards it to a provider core or PC router making use of MPLS to tag the traffic.
- Companies use this type of VPN in order to keep their customers technically separated but physically linked in a shared network.
What is the P2P VPN?

A P2P VPN is a virtual private network service that is able to anonymize the user’s internet traffic via torrenting. P2P VPNs are different from normal VPNs in that they allow users to download torrents and other types of files either via a torrent client or any other P2P file transferring application without alerting government agencies or internet service providers. The obvious benefit of using a P2P VPN is the ability to download torrents anonymously. P2P VPNs have grown in popularity in the last couple of years because of an increased need for torrenters to stay anonymous. More and more governments and copyright holder groups are taking strict action against torrenters and hence they have started to look for ways to protect themselves. Generally, P2P VPNs cost anywhere from $3 to $14 per month.
What is Layer 2 Tunnel Procol VPN?

The Layer 2 Tunneling Protocol (L2TP) is one of the most popular computer networking protocols. Internet service providers use this protocol to enable VPN operations. It is unique in that it merges two protocols: one from a company called Cisco and the other from Microsoft (PPTP). The main benefit of using L2P is that it saves dial-up costs and other overheads for users who want to connect to their office site remotely.
What is SSTP VPN?
SSTP VPN protocols work similarly to PPTP as they secure and transfer PPP traffic. However, SSTP VPNs utilize an SSL/TLS channel which the PPTP doesn’t. Hence, SSTP VPN protocols offer more security than PPTP. They are also unique because they offer secure key negotiation, encryption, and traffic integrity checking. SSTP is not the most popular VPN protocol because it works best for Windows users only. While it is possible to use on Android and Linux devices, it is difficult to set up properly. Services that offer the SSTP protocol usually cost between $3 to $10 depending on the length of the subscription period.
What is IKEV2 VPN?

IKEv2 stands for Internet Key Exchange version 2. It secures internet traffic by establishing and handling the Security Association or SA attribute within another authentication suite. That suite is usually IPSec. IKEv2 is a very secure protocol and can incorporate ciphers like Camellia, 3DES, and AES among others. The MOBIKE feature ensures no data leaks even when the user switches networks. It is also renowned for being fast.IKEv2’s popularity has been on the rise since it works very well on iOS devices and can restore dropped VPN connections without any input from the user. Services that offer the IKEv2 protocol usually cost between $4 to $11 depending on subscription period length.
Are All VPN Services Secure?
No. Not all VPNs are secure. However, signing up for a reputable VPN service will usually guarantee security and anonymity. With that said, free VPNs are usually not safe and may actually compromise data integrity and anonymity.
How to Understand Whether a VPN Secure or not?

To understand whether a VPN is secure or not, check the current IP address without VPN and then with the VPN installed. This can be done with help from tools like BrowserLeaks. There are many other ways to check if a VPN is secure. Any VPN that claims to be secure has to offer IP leak protection. The best way to find out is to read reviews. Secure VPNs do not log information. Check if the VPN in question is a zero-logs VPN as that is the only way to ensure privacy and anonymity on the internet. Read the privacy policy document of the VPN in question to see if it logs any data. Another way to know if the VPN is secure is to check for the Kill Switch feature. A Kill Switch will cut off internet access on a VPN connection drop. Without it, a VPN cannot claim to be secure.
Does All VPN Services Block Internet Sites Tracking?

No. Free VPNs claim they do but in reality, they often don’t. Even paid services sometimes fail to block internet site tracking. For complete security is it essential to sign up for a premium VPN that has a clean record of blocking site tracking. Companies and other entities usually track users via malware, IP address, cookies, fingerprinting, DNS leak, and doxxing. A VPN takes care of most of these but an anti-virus program should also be used for complete protection. Avoiding clicking on suspicious links and unknown emails will always improve security further.
Does VPN Service Prioritize the Internet Security over Speed?

Most VPN services prioritize internet security over internet speed. Of course, the final connection speed will depend on the internet connection of the user. But even the fastest VPNs can reduce download speeds by 10 to 20 percent. Premium VPNs minimize speed loss while maximizing security and privacy.
They also use enhanced security features and better logging policies which ensure more security but may decrease speed. Users should sign up for the best VPNs with better server infrastructure and service quality to avoid sacrificing speed for security.
Does VPN Service Care About Internet Privacy?

Generally, yes. VPN services care about internet privacy. But not if the VPN in question is a free VPN. Free VPNs are commonly involved in questionable practices that do not provide any evidence that they care for privacy.
Premium VPNs have “no-logging” policies which demonstrate that they prioritize privacy. They also have strict VPN protocols and secure servers to ensure internet privacy. Premium VPNs support privacy advocacy groups all over the world to make the general population more aware of their privacy rights in cyberspace. Individuals who want to ensure their own privacy should avoid free VPNs altogether and instead use top-of-the-line VPNs after reading user reviews on various forums and review sites.

