Security testing tools are software programs used by security experts to scan systems for vulnerabilities, identify and remove potential threats, and manage security processes. The primary purpose of security testing tools is to perform penetration testing, which involves finding system vulnerabilities or security threats in a simulated attack.
The results of a penetration test are used to upgrade the system’s security. Security testing tools are used in several industries, including gaming, software, social media platforms, streaming platforms, e-commerce sites and other markets.
Though this article covers 15 programs in total, a top selection list of the best security penetration tools is given below.
- Most Economic Testing Tool: Xray
- Most Used Testing Tool: Metasploit
- Best Testing Tool: Powershell-Suite
- Best Open-Source Testing Tool: BeEF
There are different types of security testing tools in use today. In 2018, 76% of companies were victims of data breaches through attacks on applications, resulting in the widespread use of application security testing tools. In 2021, a report from security firm Barracuda Networks found that one-third of businesses had been breached twice in the past year due to poor application security—further confirming the necessity of penetration testing.
The best security penetration tools in the market are detailed below.
Table of Contents
1. Powershell-Suite
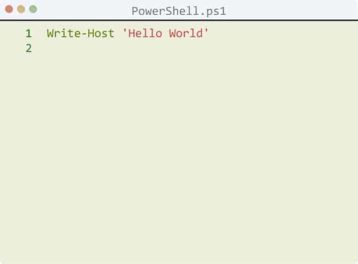
Powershell-Suite is used to scan and detect vulnerabilities of systems on a network. Powershell-suite is also used to access data on Dynamic Link Libraries (DLLs), handles, processes and other aspects of Windows devices.
Powershell-Suite consists of a scripting language, configuration management and command-in-line shell. The scripting language includes an extensible formatting system, a type system and built-in support for standard data formats like JSON, XML and CSV. The configuration management has features that enable users to make declarative configurations and custom scripts, apply configuration settings, and use push or pull models to install configuration. The shell component has a pipeline for chaining commands, an in-console help system and other features.
The advantages of Powershell-Suite include allowing users to explore several attack possibilities, helping to establish effective login methods and integrating with WinRM to eliminate the use of Remote Desktop Protocol (RDP), which can expose users to serious attacks.
However, there are a few notable disadvantages. Attackers can manipulate the operating system due to its simple interface, or invade the network without using external files or use the tool to hide an attack.
Note:
Powershell-Suite is supported on macOS, Linux and Windows. The pipeline for chaining commands and in-console help system are some of the features unique to this tool. Overall, the program can perform tests such as post-exploitation, infrastructure scanning and collation of information, and communication structure attacks.
To use Powershell-Suite, users must first launch the tool in Windows 10 by typing “Powershell” in the search bar and then right-clicking on the result to reveal a drop-down menu. Users can then select “Run as administrator” to launch Powershell. To test security with Powershell-Suite, simply set up the launcher and payload, and run the test.
The program costs $489.02 for one user license with a one-year subscription and $606.62 for one user license with a one-year subscription and yearly premium support. There are three free versions of Powershell-Suite: Powershell Plus, PowerGui and Powershell ISE.
2. Netsparker

Netsparker is used to detect vulnerabilities such as cross-site scripting (XSS) and SQL injection in web APIs, web services and web applications. Netsparker offers a Chrome-based crawling engine, false-positive detection, proof-based scanning technology, compliance testing, automatic scans, more than 49 integrations, REST API, technical reports and other features.
The advantages of using Netsparker include accurate detection of security threats using proof-based scanning technology, up to 1,000 web application scans, automatic scanning and team access for easy collaboration and report-sharing. However, the disadvantages are the program’s high costs, configuration difficulties, long scanning times, and limited scans for website URLs.
Scanning website URLs is one of the primary uses of Netsparker, which can be done using the following steps.
- Open the software application and locate the “Home” tab.
- Click “New” to display a new service scan dialog.
- Enter the website URL in the “Web Service URL” or “Target Website” options.
- Configure authentication, scan policy and Netsparker standard scan fields.
- Select “Start scan” from the crawl.
- View results after the scan is completed.

Netsparker is supported on Windows, Linux, macOS and web browsers.
Pricing can be obtained by requesting a quote on Netsparker’s website. There is no free version.
Netsparker can be used to test security by simply selecting the type of security check users would like to perform in a web application security scan.
3. Xray
Xray is used to detect open ports on a network by using DNS requests, API keys and wordlists. Xray’s features include deep recursive scanning, impact analysis, native integration, detailed reports, native BDD support, static application security testing (SAST) capabilities and use of a vulnerability database (VulnDB).

The advantages of using Xray include security scanning before and after binaries are created and restrictions on downloads not complying with security policies or licenses. The disadvantages of using Xray include the lack of a post-deployment stage and the inability to detect hidden content in codes. Further, users need to use IDE with Xray’s user interface to manage security.
After installing Xray, users can perform a data scan by following these steps:
- Go to “Admin.” Locate and select “Configuration” and then “Artifactory.”
- Click on “Configure Indexed Repositories” and include the repositories that need to be scanned.
- Tap “Index Existing” to scan files in repositories.
- View the results.
Xray is supported on Windows, macOS and Linux.
Xray offers cloud (SaaS) and self-hosted plans, and there’s a free version of the cloud platform. The cloud plan consists of a Pro Team plan and an Enterprise plan, costing $98/month and $699/month, respectively. Under self-hosted plans, there are the yearly Pro, Pro X and Enterprise X plans, which cost $3,200/server, $19,900/server and $41,500/server, respectively. There is also the Enterprise+ plan, but clients have to request a quote to get the price.
4. SimplyEmail

SimplyEmail is used to collect information available on email addresses on the web. Users can make use of the Canario service in SimplyEmail to find data leaked to the internet, such as email addresses, hostnames and passwords. The name generation feature allows users to filter search results to some accuracy. SimplyEmail then verifies emails by checking MX records, sorting, checking for 250 codes if the server is suitable, and then displaying results with verified email addresses.
Some of the features available on SimplyEmail include a multiprocessing queue for modules, theHarvester modules, a result queue and built-in parsers.
The pros of using SimplyEmail are that theHarvester is easy to integrate, writing modules is simplified, the program offers raw results, and major settings can be changed quickly. The cons of using SimplyEmail include occasional freezing and issues with the pastebin functionality.
SimplyEmail is supported on Kali Rolling, Ubuntu, Docker, macOS and Debian.
5. Wireshark

Wireshark is a network protocol and packet analyzer used to find details about network protocols, decryption and packet information. The information gathered is viewed using a GUI or TTY-mode Tshark utility.
Some of the features available on Wireshark include VoIP analysis, live capture and offline analysis, decryption support for protocols, the ability to read or write several capture file formats, display filters, deep inspection of many protocols, a three-pane packet browser and more options.
The benefits of using Wireshark are that the software is compatible with multiple platforms, provides full details about packets on a network and supports command line input (CLI). Most of all, this program is available for free.
The downsides to using Wireshark are that the local capture of packets might not reflect actual network traffic, users may encounter issues with sending the information gathered from the network, sometimes it’s unclear whether some IP addresses captured in a packet are real, and notifications don’t distinguish when there’s a network intrusion.

Wireshark is available for free as open-source software under the GNU General Public Licence version 2. After downloading the software from Wireshark’s website and then installing and launching the program, users can run a capture by clicking the capture button, which will start to record all the incoming and outgoing data of users’ Ethernet interface. The resulting data displayed on the screen is called network protocol data. Stop capture from the capture menu and analyze data gathered.
Wireshark is available on Windows, Solaris, Linux, FreeBSD, OS X and NetBSD.
6. Metasploit

Metasploit is used to identify and exploit vulnerabilities, control security analysis, gather results and report, and upgrade security awareness. The available features on Metasploit are command-line tools, test automation, vulnerability scans, manual tests, reporting and analytics, API and integrations, reconnaissance and problem tracking.
Metasploit can be used on networks, applications and servers, and offers several merits, including gathering testing data for over 1,500 exploits, network segmentation tests with meta modules, manual brute-forcing and an easy-to-use GUI interface and command line.
As for the cons of Metasploit, the software is not easy to learn, has limited GUI-based utilities, is difficult to install if a system has antivirus and can crash a system if not used properly. Further, the live technical support service may yield slow responses.

Metasploit starts a penetration test by scanning for and identifying vulnerabilities. Metasploit integrates with Windows patch enumeration, Nmap, Nessus and SNMP scanning to identify vulnerabilities. After detecting a vulnerability, users check Metasploit’s database for the exploit that will grant access to that vulnerability. Users then pair the exploit with a payload such as Meterpreter to gain access. After exploitation, Metasploit offers useful tools like packet sniffing, keyloggers, pass the hash, pivoting and privilege escalation tools.
Metasploit is available on Windows, Linux and macOS.
Metasploit offers two products: Metasploit Framework, which is free and open-source, and Metasploit Pro, which costs $15,000 annually with a 14-day free trial.
7. BeEF

BeEF or Browser Exploitation Framework is designed for web browsers to defend against web attacks. BeEF uses GitHub to detect vulnerabilities beyond the user system and network area.
Some of the features of BeEF are keystroke logging, plugin identification, intranet service exploitation, browser proxying, extension and restful API, QR code hooking, Metasploit integration and PhoneGap modules.
BeEF, a free penetration tool, offers many benefits, including connections with more than one browser and the ability for users to start directed command modules. The program also allows pen-testers to use user-side attack vectors to ensure the security of the client’s web browsing network. However, BeEF is difficult to use for beginners.

To use BeEF in a local network, a localhost is used. BeEF uses a hook, which is a JavaScript file that “hooks” (i.e., exploits) the target browser while serving as a command-and-control between the browser and attacker. Immediately after BeEF hooks a browser, users can then inject more payloads and commence post-exploitation. To locate a local IP address, users should open a new terminal and enter “$ sudo ifconfig”. To target a web browser, users need to identify a webpage the target visits often and attach a BeEF hook to the webpage. Users then inject a JavaScript payload by injecting the JavaScript hook into the webpage header. Once the target visits the website, the browser becomes hooked. The IP address and operating system of the hooked browser are displayed on the BeEF GUI.
Note:
BeEF is supported on macOS 10.5.0A or higher and Linux, but not on the Windows platform.At its core, BeEF is a free and open-source penetration testing software. QR code hooking is a feature unique to this program.
BeEF was designed mainly for penetration testing, but aside from that, the program can run RSpec and functional tests.
8. Zed Attack Proxy (ZAP)

Zed Attack Proxy (ZAP) is used to perform security testing on mobile applications by sending malicious files or requests through a message to test if the mobile app is vulnerable to the malicious content.
ZAP offers many features such as a Jenkins plug, WebSocket testing, brute force attack support, a passive scanner, a scan policy, proxy servers, API, web crawling, directory searching, an automated scanner, fuzzer and AJAX spidering.
The advantages of using ZAP are that the program is open-source and free, perfect for beginners and offers cross-platform compatibility. However, one disadvantage is that active scanning and spidering against a live website is not safe and may lead to data loss.

To start penetration testing with ZAP, start up the program and click on “Quick start.” Enter the URL of the web application that needs penetration testing in the URL text box and click on “Attack.” The risks of the web app are displayed on the “Alert” tab. Users can run active scans to identify other vulnerabilities by launching known attacks against targets. To carry out an active scan, the relevant websites should be selected in the “Tree view” in the “Sites” tab. Users can then right-click on the selected sites to trigger “Active scan.”
ZAP is an open-source and free penetration testing tool that’s supported on Windows, macOS and Linux.
9. Hashcat

Hashcat is a password recovery software tool that’s used in penetration testing to identify easy-to-hack or compromised system data. Some of the features available on Hashcat are a built-in benchmarking system, multi-platform compatibility, an integrated thermal watchdog and support for distributed cracking networks, automatic performance tuning, session and restore, password candidate brain functionality, and many more.
The advantages of using Hashcat include a fast password cracking process, an in-kernel rule engine, advanced password recovery, free and open-source, cracks several hashes at once, easy to install and easy API integration. However, the disadvantage is that cybercriminals can use Hashcat for illegal transactions.
Hashcat works by first guessing passwords using brute force attacks, a lookup table, a dictionary or rainbow table. The readable passwords are translated into different hashes with several hash keys, such as MD5 and SHA. The hashes are then compared to the actual hashes being cracked to find a match.
Note:
Hashcat is free, open-source and available on Linux, macOS and Windows. The password candidate brain functionality and integrated thermal watchdog are unique features of this penetration testing software program.10. John the Ripper
John the Ripper is a fast password cracking tool used to reveal weak passwords on a system.
Users of John the Ripper benefit from features such as support and auto-detection of different password hash types such as DES-based, FreeBSD MD5-based, “bigcrypt,” OpenBSD Blowfish-based and BSDI extended DES-based. John the Ripper also supports DES-based Windows LM, Kerberos/AFS and DES-based tripcodes.
The pros of using John the Ripper include fast results, cross-platform support and customizable features. However, the cons are that the program can be hard for new users to operate, and there may be compulsory logins to the user account to install software and recover passwords.
John the Ripper can either use dictionary attacks or brute force attacks to crack passwords. Using a dictionary attack, the tool collects string samples from a particular text file, a wordlist, already-cracked passwords or a dictionary. The samples are then encrypted similarly to the key, method and algorithm of the original password. Dictionary words could be varied randomly using the single attack mode of the tool, and several hash variations are compared.

John the Ripper is available on macOS, Unix, 11 Unix-like OS, Windows, DOS, BeOS and OpenVMS. John the Ripper 1.8.0 Pro for Linux, Linux with upgrades, and Linux with upgrades and support cost $39.95, $89.95, and $185, respectively. And John the Ripper 1.7.3.1 Pro for macOS, macOS with upgrades, and macOS with upgrades and support cost $39.95, $89.95 and $185, respectively.
John the Ripper has a free and open-source version called John the Ripper Jumbo. The program stands out from competitors by offering several password crackers in an all-in-one product.
11. Aircrack

Aircrack is used for detecting weaknesses within a wireless connection by observing data packets, attacking through packet injections, testing wireless network capacity and cracking passwords.
Some of the merits of using Aircrack include the ability to capture and export data packets, support for multiple drivers and cards, testing for WiFi devices and driver capacity, fake access point creation, high tracking speed, and support for WEP dictionary attacks and replay attacks. One drawback, though, is that Aircrack cannot be used to monitor or perform penetration tests on non-wireless networks.
Aircrack can be used to crack WiFi WPA/WPA2 passwords using the following steps:
- To start, launch the terminal in Kali Linux and then use “iwconfig” to decide the name of the wireless adapter. Some wireless cards may show error messages; in that case, use the “airmon-ng” command to remove the error.
- After that, use the “airmon-ng” command to activate monitor mode in the WiFi card (wlan1). For the interface in the terminal, use wlan1mon.
- Input the command “airodump-ng wlan1mon” to show all the access points within the computer perimeter, including users connected to that access point. This command captures the network packets and gathers data from wireless packets. Make sure not to close this terminal.
- Add more parameters to the “airodump-ng” command. Insert the last command: “airodump-ng -c channel –bssid [bssid of WiFi] –w [path to writing the data of packets] wlan1mon [interface]”
- Input the command “aireplay-ng –death 10 –a [router bssid] interface” to de-authenticate the users on the WiFi network.
- Finally, use the command “aircrack-ng –b [bssid of router] –w[path to word list] [path to capture packets]” to crack the WiFi with the captured packets.
Note:
Aircrack is free, open-source and available on Windows, Solaris, macOS, FreeBSD, OpenBSD, eComStation 2 and Linux.All of the features available are unique to this wireless penetration testing tool.
12. Wfuzz

Wfuzz is used for launching brute force attacks on web applications to reveal vulnerabilities such as SQL injections and XXE injections. Wfuzz offers features like cookies fuzzing, capacity for multiple injection points, output to HTML, authentication support, brute force HTTP methods, multiple encoders per payload, SOCK and proxy support, payload combinations with iterators, HEAD scan, and many others.
Some of the pros of using Wfuzz are versatility, customization through the modular framework, and the ability to perform manual and semi-automatic tests. Some of the cons of using Wfuzz are slow speed, high RAM requirements and high CPU usage.
Wfuzz detects vulnerabilities by brute-forcing, which can be done by using this command: “wfuzz.py -c -z file -f commons.txt –hc404 –html website URL”. This command will brute-force the website entered to find malicious files, scripts and directories.
Wfuzz is free, open-source and supported on Linux, Windows and macOS.
13. W3af

W3af (short for Web Application Attack and Audit Framework) is used for scanning and exploiting vulnerabilities of web applications such as XSS and SQL injection. Some of the features available on W3af include a command line interface, plugin extensions, GUI, DNS spoofing, cookie handling, DNS cache, fuzzing engine, user-agent faking and manual request generation.
The advantages of W3af include identification of over 200 weaknesses and threats in web applications, ease of use for beginners and options to configure as a man-in-the-middle proxy. However, one disadvantage of this testing tool is the presence of false negatives.
To use W3af, users should download the latest version of the application and define the information required and the order of plugins to be called for this information. Users should then type in “help” to see all available commands, “Plugin” to see a list of plugins, or “help <PluginName>” to see the command for a particular plugin.
Note:
W3af is open-source, available for free and supported on Windows, macOS, Linux, FreeBSD and OpenBSD.To test security, W3af will locate all web links, forms and queries. The tool then sends unique requests to each input, performs an analysis on the output, and presents the information as results.
User-agent faking is one feature that’s unique to this tool. W3af performs web application analysis and application security testing.
14. SQLMap

SQLMap provides an automated way to detect and exploit strictly SQL injection weaknesses and takes control of database servers. SQLMap’s features include support for multiple database types, enumeration of necessary data like password hashes and users, DB fingerprinting, a detection engine and compatibility with multiple injection techniques.
The pros of using SQLMap are that the program offers a quality detection engine with fast and reliable results, automatic detection of SQL vulnerabilities, thorough vulnerability scanning, and customization of commands to unique outcomes. The cons of SQLMap include the lack of a GUI, generation of false positives, and manual confirmation of vulnerability.
To use SQLMAP, users first select a vulnerable website and identify any possible injection point. Users then retrieve data on SQL vulnerabilities, exploit the vulnerabilities and generate the report.
Note:
SQLMap is free, open-source and supported on Windows, Linux and macOS. This tool is also supported on database systems such as MySQL, SQLite, Sybase, Altibase Oracle, and Microsoft SQL Server.DB fingerprinting is a feature that’s unique to this penetration testing tool.
15. Hydra

Hydra is a penetration tool that makes use of different brute force strategies to test the ease of gaining unauthorized access to a system through password cracking. Some of the features of Hydra include password guessing, dictionary-based attacks, username guessing, brute force on multiple hosts, support for parallelized connections, and compatibility with multiple security protocols.
The advantages of using Hydra are flexibility, speed of login cracking, and the ability to perform HTTP post form attacks. The disadvantage of Hydra is that the tool takes time to crack passwords due to password and username combination trials.
To use Hydra for security testing, users should establish a secure network and then set up a test network and test server. Users should then configure the network services and ACL, set up the network with strong passwords, implement SSL, cryptography and IDS. After that’s done, Hydra should be put up against the network and used to attempt to crack the login credentials. The success or failure of this attack provides information on the vulnerability status of the network.
What You Need to Know About Penetration Testing

Penetration testing is the use of security tools by cybersecurity experts to simulate an attack in order to identify and exploit system vulnerabilities. The primary purpose of penetration testing is to identify security loopholes or weaknesses in a computer network to prevent future exploitation by hackers and then upgrade the system security accordingly. Penetration testing also helps discover any compliance gaps with security regulations and policies.
The types of penetration testing include network penetration testing, physical testing, web or application testing, social engineering testing and cloud penetration testing. Penetration testing offers many benefits, such as ensuring adequate security protection, identifying and preventing security threats, managing security risks according to severity, confirming compliance with security certifications, and protecting the data of clients and employees.
This is important:
Penetration testing can be done through external testing, internal testing, blind testing, double blind testing or targeted testing. External testing involves targeting the visible part of a data network and trying to extract information therein. On the other hand, internal testing involves simulating a malicious attack behind an application’s firewall. Double-blind testing launches an attack without any prior security information. Targeted testing is where both the tester and security personnel are aware of the attack simulation for the sake of learning, while blind testing involves the launch of an attack with only the application name and no other information available to the tester.What Are the Benefits of Using a Security Penetration Testing Tool?
The benefits of penetration testing are given below:

- Provides valuable insights on security systems: Penetration testing provides room for an in-depth analysis of systems and recommendations for software and hardware security improvements.
- Educates the security team and other employees: With penetration testing, the security team and other staff will be armed with information on safety measures and how to improve software security.
- Helps identify and protect against system vulnerabilities: Penetration testing helps to identify vulnerabilities and provides insight into different hacking methods and the best ways to prevent attacks.
- Gives information about security defense capabilities and lapses: Penetration testing helps to determine the strength and speed of a security team’s competence to respond to future attacks.
- Ensures business continuity, loyalty and trust with clientele: A good cybersecurity system ensures personal data is protected, thereby proving trustworthiness to both new and established clients.
- Provides compliance with security regulations: Penetration testing points out loopholes in security policies that could lead to fines if discovered by authorities.
What Are the Types of Penetration Tests?
Some of the types of penetration test are detailed below.

- Network Penetration Testing: This type of test is divided into internal and external penetration testing and involves the use of public data (such as web data and cloud services) and private data available to only insiders to access information or hack a system. For instance, in network penetration testing, a pen-tester may pretend to be staff or security personnel to gain information to hack a network system.
- Web or Application Testing: This type of testing explores vulnerabilities in websites and applications, from the design to the back-end code. The aim is to ensure the security of applications is up-to-date and free of vulnerabilities.
- Social Engineering Testing: This type of testing is used to gauge staff’s vulnerability to malicious attacks. This test uses methods such as phishing or vishing to gain trust and trick employees into providing confidential information that might be useful for hackers.
- Physical Penetration Testing: This involves physically testing security weaknesses either through hardware devices or intrusion by personnel. For example, a USB cable that contains malicious content could be inserted into hardware to measure how easily such threats could unfold.
Is There an Open Source Penetration Testing Tool?

Yes, there are open-source penetration testing tools such as W3af, Wfuzz, Aircrack, Hashcat, ZAP, BeEF, Wireshark and SimplyEmail.
Premium tools like Netsparker are different from open-source tools. For example, W3af is the most extensive tool for identifying vulnerabilities in web applications but does not provide access to application testing. Netsparker as a premium tool, on the other hand, performs the same function as W3af but provides application testing as well. And while Netsparker contains more monitoring tools than W3af, the latter is easier to use and gain insights on vulnerabilities. Both tools are very effective and give quality results.
Can Penetration Testing Tools Be Used with Android?
Yes, penetration testing tools can be used with Android devices, but not all. Some of the best Android hacking tools for penetration testers are OWASP Zap, SQLmap, zANTI and Kali Nethunter. The best Android penetration tool is zANTI, which provides high-intensity information about possible malicious attacks, permits replication of real-world attacks, and can be used to identify threats from any connected device or network with only one button.
Can Penetration Testing Tools Be Used with iOS?
Yes, penetration testing tools can be used with iOS. There are a few iOS hacking tools for penetration testers such as Radare, MobSF, Burp Suite, iSPY and Cyprict. The best penetration testing tool for iOS is MobSF because this ethical hacking tool provides both static and dynamic analysis of connected applications on iOS and also serves as one of the best automated vulnerability scanners.
Is Using Penetration Testing Tools Easy?

Penetration testing tools are not easy to use in advanced levels, especially for non-experts in security software. However, Netsparker is quite easy to use compared to others.
Netsparker is a penetration testing tool used to detect vulnerabilities such as cross-site scripting (XSS) and SQL injection in web APIs, web services and web applications. Netsparker is easy to use because the tool allows automation of the entire process for web auditing and makes scan configuration simple, even for beginners.
Which Programming Languages Are Better to Code Penetration Testing Tools?
There are several programming languages to learn cybersecurity and provide education on advanced-level hacking. Some of the best programming languages used for writing penetration testing tools are listed below.
- Python: SimplyEmail, W3af, Wfuzz and SQLMap
- Java: Xray, ZAP and Hydra
- JavaScript: Netsparker
- C: Hashcat, John the Ripper, Aircrack and Aircrack
- Ruby: Metasploit
Where Does the Term ‘Penetration Testing’ Come From?

Penetration testing is also referred to as pen-testing. The term was coined in the 1960s by the U.S. government after being warned of a threat to a security system. To check that out, the government formed a group of experts called Tiger teams to attempt to break into the computer network, which led to the use of penetration testing.
The first use of the word “penetration” with regards to computer security was in 1967 at a Joint Computer Conference, where security experts listed possible threats to computer networks, including “penetration.” From that point, publications were released about penetration and teams were formed to “test” the penetration of different computer networks, eventually establishing the term “penetration testing.”
Note:
However, not all tools identify themselves as penetration testing tools. There are several other cybersecurity terms similar to penetration testing, such as ethical hacking. Tools like Metasploit, Wireshark and John the Ripper are identified as ethical hacking tools rather than penetration tools.Which Penetration Testing Tool Is More Preferred by Penetration Testers?
The most preferred tools by penetration testers are Hashcat, Metasploit and Wireshark.

Wireshark is best preferred for network analysis because the tool contains many features and provides an extensive range of useful information. Wireshark is also easy to use and suitable for both professionals and amateurs in pen-testing.
Hashcat is largely preferred for speed and versatility and works across multiple algorithms like LM Hash, NT hash, MD-5 and various operating systems, including Windows, OS and Linux.
Metasploit is the first choice for most pen-testers involved in testing multiple applications because the tool is easy to use.
Irrespective of preference, however, the penetration tester job description is what determines the penetration tool to be used.

