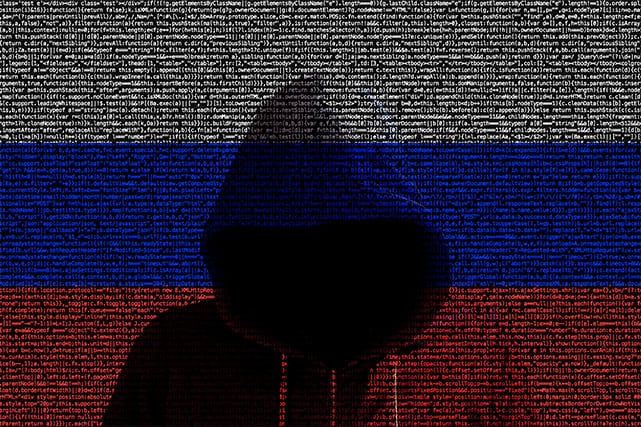
Multiple news reports linked Russian spying agencies to the recent string of cyberattacks targeting the U.S. government. Reportedly, hackers had the resources available to monitor internal messages from the U.S. Department of Commerce and Department of Treasury.
In addition to compromising government systems, the group was able to aim their target at private organizations as well. Experts say this marks a substantially sophisticated cyberattack, and one that could have only been pulled off with help from a nation-state.
The U.S. is not the only target of these attacks, as security agencies across the North Atlantic ocean in the U.K. have also scrambled to get a grip on the scale and impact of the latest attack from Russian hackers on their own networks. In the U.S., though, agencies have deemed these attacks consequential enough to have a White House National Security Council meeting.
According to a report from Reuters, the National Security Council said it asked the Cybersecurity and Infrastructure Security Agency (or CISA) and the Federal Bureau of Investigation (FBI) to coordinate an effective response to the recent compromise.
With that said, readers should note that currently, the U.S. government has not formally named any nation-state as responsible for these cyberattacks.

As mentioned above, media sources citing officials and experts have alleged that Russia is the main perpetrator of these attacks.
For example, the Washington Post has named Cozy Bear or APT 29, a Russian hacking group allegedly linked to Russia’s Foreign Intelligence Service (SVR) and Federal Security Service (FSB), spying agencies believed to be behind the attacks.
There are reasons to believe that Cozy Bear may be the group behind the attacks since just a few months ago in July, Canada along with the U.S. and the U.K. accused Cozy Bear of making attempts to steal vital coronavirus vaccine data from researchers. Going further back, the same group has also been named in the list of hackers responsible for hacking the Democratic National Committee in 2016 and White House systems in 2014.
Chief among the private targets is FireEye, a U.S.-based publicly-traded cybersecurity software and services provider valued at around $3.5 billion. The firm released a statement on Dec. 8 disclosing that nation-state hackers had compromised some of its systems.

On Dec. 13, FireEye separately announced that hackers have infected the systems of individuals and companies utilizing a software program called Orion, developed by U.S.-based software firm SolarWinds. Orion comes with a replacement mechanism which hackers compromised and then utilized to install a backdoor and distribute malware dubbed “SUNBURST” by FireEye researchers.
Using that, Microsoft confirmed in a statement, hackers stole signing certificates that allowed them to impersonate accounts and customers to deceive the target organizations.
FireEye said that according to its evaluation, the compromises were not self-propagating and that each of the attacks required careful and guided planning.
While the full scale of damage is unknown at this point, the CISA issued several alerts and an emergency directive for all U.S. federal agencies to remain vigilant, discontinue using SolarWinds Orion software applications and check their networks for breaches.
It should be mentioned, though, that the Russian Embassy released a statement denying any wrongdoing or involvement on its part and accused American media of making unfounded claims against the country’s government.


Why has President Trump not made a statement about this?
If he is not still governing, perhaps Vice President Pence will give us a heads up on what is being done. This is frightening!