Haven Review
Yes.
It is true.
Edward Snowden did create this new app Haven.
Interestingly enough, the app itself has managed to strike up quite a lot of controversy in the past couple of weeks.
A lot of experts have bashed the app.
While some have tried to adopt it.
The first thing users should know about the new Haven app is that Snowden has developed it (with his team of course) with security and privacy in mind.
But there is more to this app than just security privacy.
This Haven review will discuss almost all of the app’s features.
And how can users take advantage of them to add additional security layers to their online anonymity and privacy?
We recommend that all potential Haven users should give this review a thorough read before committing to the app.
Table of Contents
The app is good, no doubt.
But it does come with its limitations.
Mostly we’ll try to discuss how you can use the app for reasons other than anonymity.
Like how to use the new Haven app securely and safely to keep yourself away from hackers and other cybercriminals who want to spy on you.
So first, let’s start off with the question:
Who is Edward Snowden?
And what does he want?
Most online users who follow privacy and security news regularly would recognize Snowden’s name from miles away.
Fortunately, not online users like to follow privacy and security news.
And hence don’t know what is happening in the community.
That means, there are tons of people who don’t know anything about Edward Snowden.
Like who he is.
And why he is famous.
In short, Edward Snowden worked for the NSA and the CIA but only as a government contractor.
One day, after a lot of work, he got fed up with the way the CIA and the NSA used technology.
More specifically, he didn’t agree with the level of access government agencies had into people’s private lives.
What did he do?
He went to his manager with a complaint, NOT.
In other words, Edward Snowden decided to take matters into his own hands.
He stole a bucket load of important and highly classified documents from the organization that he worked for.
That is the NSA.
Then Edward Snowden went about his business and made efforts to expose the activities of the NSA and the CIA to the whole world.
He wanted to tell people how these organizations misuse their authority to keep an eye on people’s lives via the internet.
And how they sent all the information about people to their superiors.
What did the documents show?
The documents clearly showed that the NSA indeed abused its power.
It secretly listened to phone calls of millions of people.
The CIA and NSA also had access to people’s text messages and a lot of other stuff.
Snowden wanted to show that the NSA and the CIA went much deeper as far as invasion of privacy went.
Therefore, the safest method to let the people know about these activities, in Snowden’s mind, was to release all the information he had gathered to the general public.
He stole documents.
And then revealed them to the world.
As a result of that, the United States government declared Edward Snowden a traitor.
Some call him a terrorist.
What did Snowden do next?
He ran away from his homeland and took refuge, eventually, in Russia.
Most people who work in the privacy and security industry consider Snowden as the biggest pro when it comes to security and internet privacy advocacy.
Snowden has givens tens of talks around the world on topics such as internet privacy and security for online users and regular people.
A lot of people still hold Edward Snowden in high regard for what he did.
And that’s why, with his name associated with the new app Haven, the app has generated a lot of buzz in the media.
Security experts are already giving the app good scores based on its privacy and security features.
What Is Haven App?
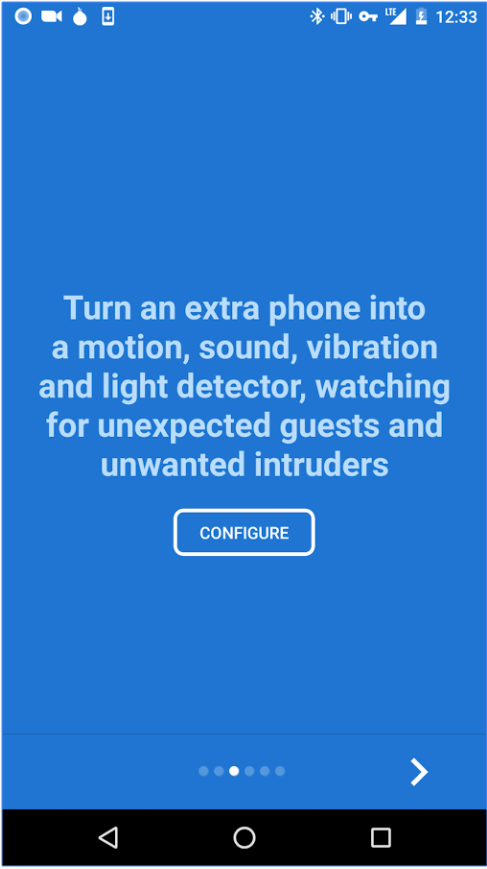
Edward Snowden and his team designed the new Haven app to act as a physical security device.
Users who want to use the app can utilize it to protect their belongings.
It doesn’t really matter if the object that the user wants to protect is an electronic or not.
Edward Snowden’s new app Haven, provides security and monitoring features by taking advantage of any smartphone device’s camera.
It also makes use of other smartphone features such as the smartphone’s Accelerometer along with its Mic.
The Accelerometer of a given smartphone’s device helps the haven app in calculating and measuring the movement of the given smartphone.
The new Haven app uses the smartphone’s mic to monitor and detect if someone has come near the given device or has moved it.
Such actions will trigger some of Haven’s features.
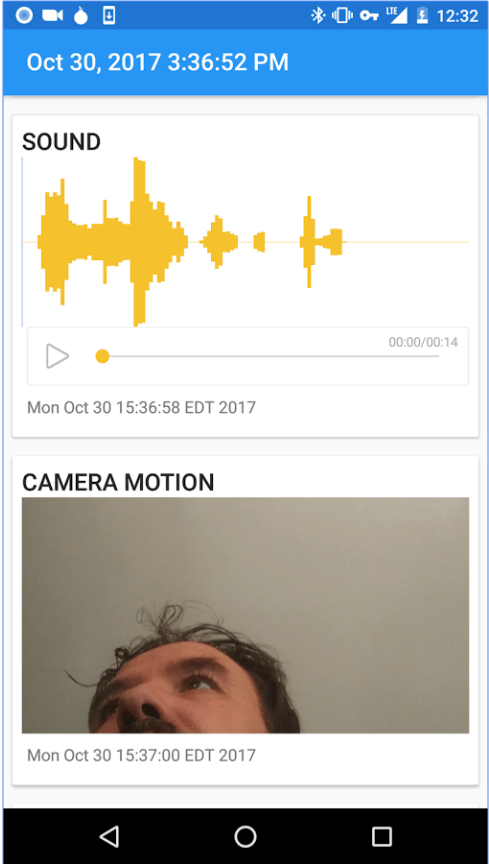
If Haven detects something, it will execute some alert protocols.
Mostly though, actions such as spying will trigger the app to snap a picture of any intruder that tries to move the given device.
Then, the new Haven app will enable the given smartphone device to store that picture on its local storage space.
The new haven app will also send the user, that is you, a text message which will let the user know that the app has detected something fish and has triggered an alert.
As you can probably tell, this can come in really handy for people who like to take with them something precious.
Of course, they must intend to protect it as well.
Such items usually include electronic devices and other articles such as,
- Diary
- Notebook
- Laptop
Some experts in the media say that Edward Snowden definitely designed the app with Investigative journalism and whistleblowing in mind.
With that said, there is no doubt about the fact that just about anyone can use the new Haven app.
Any user who wants to protect something or keep something secret can use the Haven app to achieve his/her objective.
Haven App Features
We have already mentioned the fact that the new Haven app makes use of many smartphone features to accomplish its goals.
It uses the smartphone’s,
- Mic
- Accelerometer
- Camera
These smartphone features help the app to perform its basic functions.
The haven app has several additional features for monitoring and triggering alerts.
It Makes Use Of Motion Sensor
The new Haven app makes use of the given smartphone’s camera to basically detect if someone is moving within the range of the camera shot.
The Movement Sensor
This is where the new Haven app uses the Phones Accelerometer to detect if someone is actually moving the device itself.
Audio Detection And/or Voice Sensor
The new Haven app utilizes the given smartphone’s Mic to detect if an intruder is making some sort of noise near the given smartphone device or speaking.
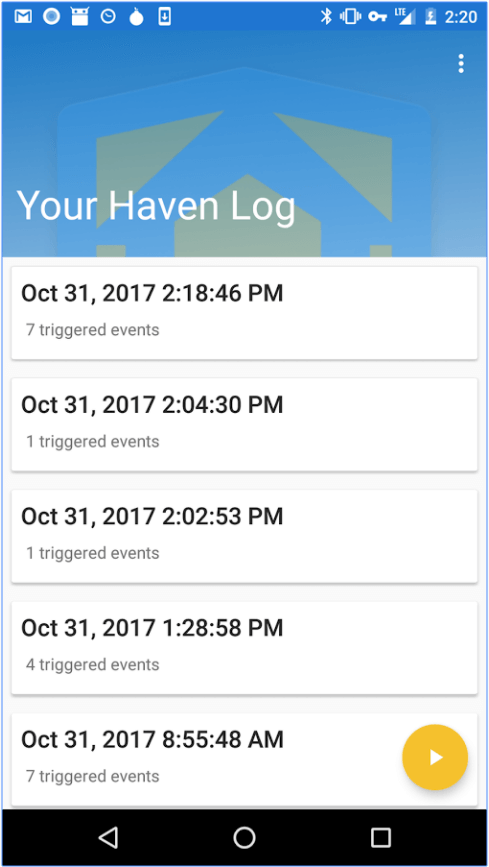
The Device Logs
We have mentioned three alert actions so far.
If the new Haven app detects any of the three that we have discussed above, it uses the smartphone’s camera.
And then it takes the picture (automatically) of the detected disturbance.
As indicated earlier, the app then moves ahead to save the picture to the smartphone device’s local storage folder.
Camera Settings
The Haven app comes with a Camera setting which allows the user to control and modify if they want the Haven app to use the device’s back camera or front camera or, in some cases, no camera at all.
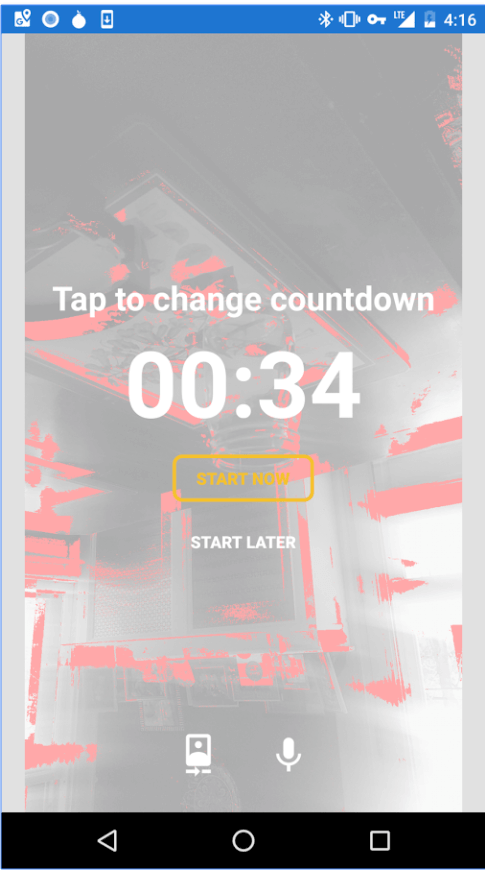
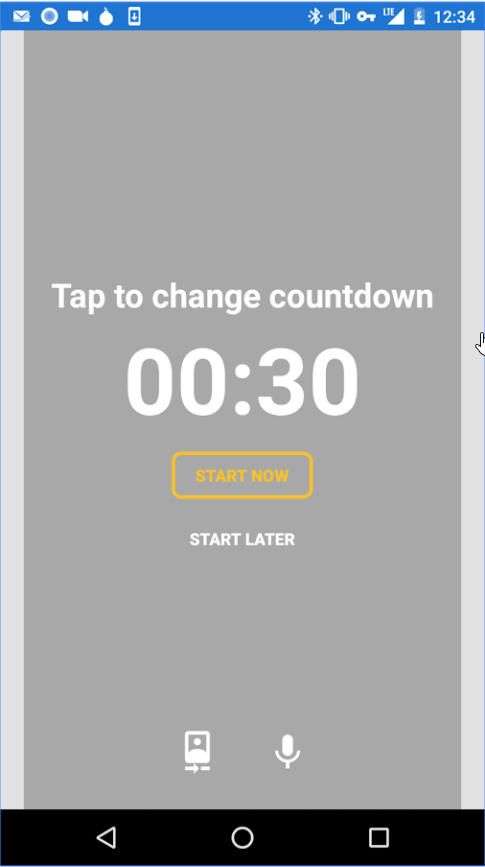
The Configuration
This is where the new Haven app enables users to configure the app’s sound sensitivity.
Users can also modify other settings such as the app’s delay time and movement sensitivity.
What’s the delay time?
The delay time is the period of time the app will wait before it starts to work.
It works similar to a solid home security system if that makes any sense.
Secure Texting Alerts And Texting Alerts
Another one of the new Haven app’s features which enable users to specify if they want to have the option of receiving text alerts via various options such as Signal (encrypted messaging service) or the device’s default (and not so secure) messaging service.
Utilizing TOR For Remote Access
Edward Snowden’s Haven app makes use of the TOR network to assists users to anonymously gain access to their Haven device (a smartphone) from any place they want to with the use of a TOR connection.
The Haven app utilizes Orbot (an app) on the user’s smartphone device to open up a Hidden Service.
This gives the Haven app a .onion web address.
The user can then go to the .onion address via the TOR network from any place of his/her choosing.
Full Haven Review
Users who want concerned about things such as Anonymity, Security and Privacy should give Haven app a try.
In the beginning, though, Haven will scare you with its main features.
But it doesn’t do anything new.
Chances are that your government already has the technology to do everything this app does to your smartphone.
You just don’t know it yet.
The new Haven app should show users how software applications can leverage three, fairly simple, features.
These features come with any and all modern smart devices.
Users should expect to spend quite a bit of time to dig slightly deeper into the new Haven app.
Once you have the hang of all its features then you will find it easier to understand that Edward Snowden and his team have really designed the Haven app to give the user a lot of control as far as the user’s privacy is concerned.
The new Haven app allows users to turn off their Haven-laden camera.
As indicated earlier, it also allows users to choose if they want encrypted messaging service.
And users can also modify settings to gain access to their Haven-installed device via the TOR network.
Aren’t these the things one normally looks for when talking about the security and internet privacy community?
The Haven app has all the features which should help it to distinguish itself from all average security apps out there on the market today.
And when you put Edward Snowden’s name into the mix, you have a great app that comes from a reasonably reputed source.
And no.
There is very little chance that Edward Snowden is actually working as an undercover agent for the NSA and the CIA.
Edward Snowden’s Haven app has a lot of credibility even though it is relatively new.
Moreover, the Haven app is totally open source.
And we all know what an open source Project means right?
Yes.
Anyone with a computer machine and an internet connection can view Haven’s code and read it as well.
Edward Snowden and his team have put in a lot of work to make sure that people have an easier time trusting their app.
But as always, you should always take appropriate safety precautions.
When it comes to apps like Haven, safety is perhaps the most important topic of conversation.
How safe is Haven?
Well, no one really knows that.
Hackers will find out soon enough by the looks of it.
With that said, there are certain measures that all users can take to ensure that they are safe and sound when they are using the new Haven app.
Good Safety Measures
What’s the biggest concern with using the new Haven app?
As we just mentioned, it’s the concern of a hacker compromising the app.
What if a hacker exploits the app and then records the user without the user knowing anything about the hack?
Of course, this is a very unlikely scenario.
Why?
Because of the way Haven’s developers have designed the app.
The app basically doesn’t save logs on any other place than the user’s own device.
Regardless, it is still a possibility that a hacker may compromise the app.
If you are in a position that you need to keep yourself and your family safe while you are using the Haven app, then there are many precautions you can take right now for your benefit.
Let’s discuss some of those.
The first thing you can do is to install the Haven app on a smartphone that you don’t really want.
Or don’t use.
Or you can simply buy a new cheap phone for this very purpose.
Buying a new smartphone just for the Haven app is probably the best idea.
Why?
Because any new smartphone is less likely to have any kind of virus on it.
This is very important to understand.
And that’s why we want to stress the point that buying a new phone is the best option because you can’t use all of Haven’s features on a single phone that you also use as your primary smartphone.
Moreover, consider the fact that if you use Haven on your primary smartphone then you have basically installed an app that has the capability to spy on the whole of your smartphone device.
And that too at all times.
The second thing you can do is to first turn off your Haven smartphone.
And then remove its batteries.
Why?
Well, if you aren’t really using your Haven smartphone then why leave it exposed to potential cyber attacks.
By turning off your Haven smartphone when you are not using it you decrease the chances of a hacker getting hold of your phone or the Haven app when you are not around.
So protect yourself and your family by thwarting hackers that want to spy on you.
The third tip is to avoid using your Haven smartphone device for any other reason that the Haven app.
This is perhaps the most important security measure.
Hackers are clever people.
But they aren’t as clever as movies would have you believe.
They can’t just sit there, type some code within minutes and then hack your smartphone device with a virus.
In other words, the user has to actually provide them an opportunity or a weakness to exploit.
And hurt the user with a virus.
Most of the time, a hacker would want the user to actually go to a malicious website.
Some might even want you to download some content.
These are some of the most common ways hackers use on regular internet users.
So if you don’t use your Haven smartphone for anything else than the Haven app then you remove the possibility of a hacker attacking you with the above-mentioned methods.
Don’t use your Haven phone for anything else and you basically ensure that hackers can’t get to you easily.
In fact, we think that if you want to eliminate the possibility of a hacker ever getting close to your phone then follow this very advise.
If you follow it strictly enough, a hacker may never get the opportunity to attack you with a Virus by infecting your haven smartphone with it.
The fourth tip is to forget about using Haven’s remote access feature.
Why?
Don’t get us wrong.
The remote access feature is fairly safe.
Moreover, you can use the Haven app to set up a password for the remote access feature as well.
But if you want to make sure that you are as close to a fool-proof safety plan as possible and you don’t have a need for such a feature, then don’t make use of it.
Enabling the remote access feature only opens more doors for hackers to hack your Haven device.
Shut all the easy doors for them.
And soon enough they will move on to a target that is much easier to hack.
The fifth tip is to use strong passwords.
So that basically means that you can’t use names as password.
You can’t use places of work as your password either.
And forget about your dog’s name as your password.
What is a strong password anyway?
In short, a strong password is a password that does not have any kind of names in it.
Haven app has one feature which it protects with a password.
That feature is the remote access feature.
And hence you should make sure you use the password protection to secure your remote access feature.
What’s the best method to do that?
Well, use a strong password.
Simple.
And easy.
Ideally, you should make sure that your password length goes beyond 12 characters.
All the characters should be random.
Use letters.
And numbers.
And symbols.
Use some capitalization techniques as well.
You can do all of that.
Or you make use of the many random password generators.
Then store that strong password someplace that is safe.
Otherwise, no one is going to come to help you if you forget your strong password.
Conclusion
That’s it basically.
Follow our advice that you should have no safety problems while you are testing out the Haven app.
Haven app has everything to become a great app.
We have no doubt that in the long run, it will help many users.
But all apps are a potential security risk to the user.
Since Edward Snowden is involved with the Haven app you can trust the people who work behind the scenes here.
Trust Haven and give it a try.
Do follow our safety guide though.
Just because Edward Snowden has made something doesn’t mean no force on earth can use it for evil.
The only person who can basically guarantee that the Haven app won’t hurt you, is you.


Very well-written thorough review.
I’m curious if you have been able to successfully use the remote access via Tor browser feature. I know you state it’s better to ignore the feature, but I would absolutely use it if I could just get it to work. I’ve gotten as far as having orbot installed on the phone and giving it it’s own .onion address, but when attempting to access that address via another device with a TOR browser, it never connects. Any tips?
We haven’t come across such a problem yet but we will look for solutions. Although, if you are only interested in receiving encrypted notifications on your mobile phone from the Haven device then perhaps using Signal. Haven does have options where it allows users to configure it in such a way that it sends encrypted notifications, video and audio files to the user’s device via Signal.
Thanks for the feedback.