As the concern for online security and privacy grows, more and more people are looking for ways to keep themselves and their data safe.
Often the focus is on protecting private data like login credentials and personal information, but protecting email content is just as important.
Keeping the content of your emails protected keeps you and the recipients and senders of your emails safe and saves any sensitive information from falling into the wrong hands.
Most modern operating systems have a built-in email client. While this makes it more convenient for you by having all of your emails in one place, it makes it so there’s not a single solution to encrypt emails on every application.

The complexity can be compounded if, for example, you use the built-in email client on one of your devices and then a web-based client on another device.
Luckily, we recognized this issue and have put together solutions for all major email clients, both web-based ones and ones built into your operating system.
Table of Contents
Microsoft Outlook

Here’s how you create one in Outlook if you haven’t made one before:
- Click on File.
- Go to Options.
- Click Trust Center.
- Click Trust Center Settings.
- Click on Email Security.
- Click Get a Digital ID.
- Select the type of certification authority you wish to use to get your digital ID. You’re free to choose any of the services mentioned on the page, but we recommend you go with Comodo.
- Once you’re finished with the previous step, you should get a message in your inbox giving you more information about your digital ID.
If you’ve followed all the steps so far, you should now have a digital ID or certificate. Once you’ve gotten your digital ID, you may proceed to the next set of steps towards encrypting your emails on Outlook:
- Click on Tools.
- Go to Options.
- Click on the Security tab.
- While looking at the field labeled Security Settings Name, you should input a name. You are free to use any name you want.
- At this point, you should make sure that you have selected the option of S/MIME in the box that says Secure Message Format.
- You should also check the box that says Default Security Setting.
- Look under the heading that says Certificates and Algorithms for the Signing Certificate section. Then click on Choose.
- In the Select Certificate box, select your preferred Secure Email Certificate if you find that the window was not selected by default.
- Check the option that says Send these Certificates with Signed Messages.
- Click OK to save all of your settings and then head back to Microsoft Outlook.
If you’ve followed all the steps properly then you should now have a digital signature to insert into all of your email messages. Of course, such signatures will not appear on your messages by default. You’ll have to do a bit more configuring before that happens.
In order to successfully attach your newly created digital signature to your messages you should complete the following steps:
- Click on New Message.
- Click on the option that says Tools.
- Click on Customize.
- Click on the tab that says Commands.
- Go to the list labeled Categories. From there select Standard.
- Turn to the list labeled Commands. Click on the Digitally Sign Message option.
- At this point, you can make things a lot easier for yourself in the future by clicking and dragging your digital signature to your toolbar. This will allow you to add the signature to your message with a single click instead of going through this process every time. You can also drag the Encrypt Message Contents and Attachments option to your toolbar as well.

After you’ve gone through this process, it’s important you understand that encrypting an email message is not the same as digitally signing the message.
To encrypt your message first and then send it to someone using Microsoft Outlook, you need to make sure that the recipient of the message has sent you at least one message in the past that includes the recipient’s digital signature as an attachment.
This is the only way for Microsoft Outlook to know that it can trust the sender of the message.
Conversely, if a user wishes to receive an email message which is encrypted from one of their senders then the user has to send the sender at least one unencrypted email message first that has the digital signature of the user as an attachment.

Clearly, this can become rather convoluted and tedious if you have more than two contacts in your email list, which nearly everyone does. This complexity is an unfortunate side effect of using the S/MIME method.
Users do have the option of digitally signing their email message by clicking the button that says Sign before sending the message. Once both the sender and receiver have each other’s digital certificates and signatures saved in their keychains, they should have no problem exchanging encrypted messages in the future.
If you added the Encrypt button to your toolbar, you only need to press that button before you press send to encrypt your emails on Outlook.
iOS

In order to take advantage of this feature, go to the Advanced Settings menu and then switch the S/MIME option to ON.
While there, you also need to change the Encrypt by Default option to YES. Once you’ve done that, you should be able to compose a new email message with encryption.
More specifically, you should see some lock icons placed right beside the name of the recipient. In order to encrypt the email message, you need to click that lock icon and make sure it’s closed.

The other thing you should note about the iOS platform is that it consults a Global Address List which acts as a type of keyserver for various S/MIME certificates whenever it wants to find the user’s contacts in the user’s exchange environment. If the email app has found a certificate it’ll show you a blue lock icon.
If you’ve followed these steps correctly but still see a red lock icon next to your recipient’s email address, then that could mean a couple of things. In some cases, it could mean that your contact is not in your exchange environment.
In simpler terms, both of you work at different companies and your email accounts are not part of the same network. In other cases, it could mean that both of you have not properly installed the other person’s digital certificate. It doesn’t really matter which case is yours since in both instances you won’t be able to send your contact encrypted messages.
However, there’s a way around this issue. Your recipient must send you at least one message with their digital signature as an attachment.
This will allow you to use the certificates to protect your emails. You should find the option to attach signatures to your messages in the exact same advanced settings menu you accessed earlier when setting up your encryption options.
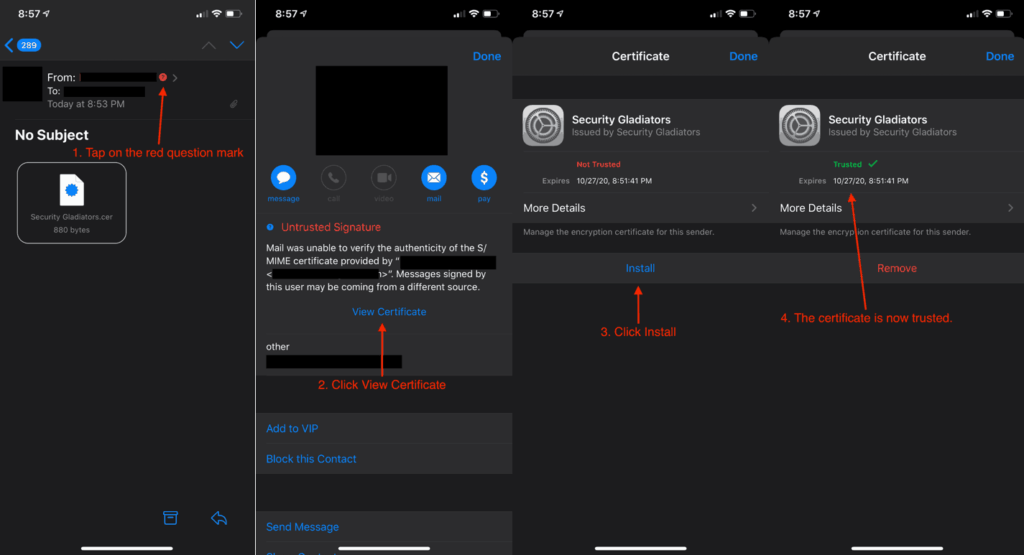
Once your recipient has sent you the email with their digital signature as an attachment, you’ll need to complete the following steps:
- Click the address of the sender.
- You should see a red question mark on your screen indicating that the app doesn’t trust the signature. You’ll need to tap the option that says View Certificate.
- Tap the option that says Install. When you do that you should see the install button changing its color to red. It will also say Remove. You need to click the option that appears in the top right corner of your screen which says Done.
- Notice the lock icon changing its color to blue when you are about to compose a message to your recipient. You should tap the lock icon and when you do, the email app will automatically encrypt your email message.
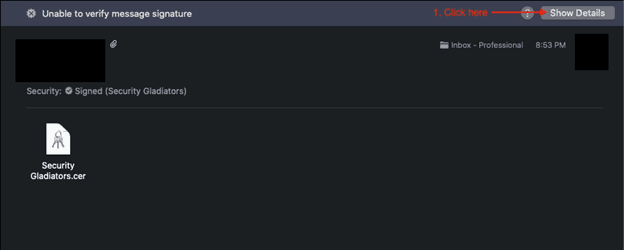
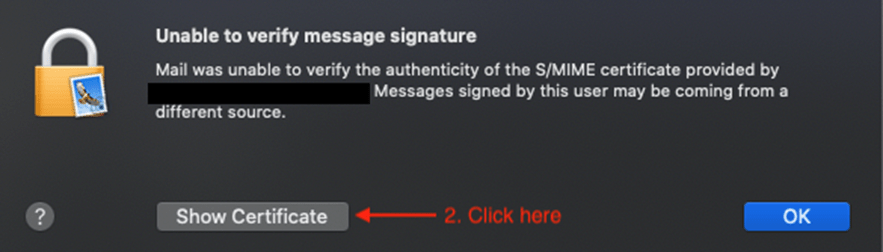
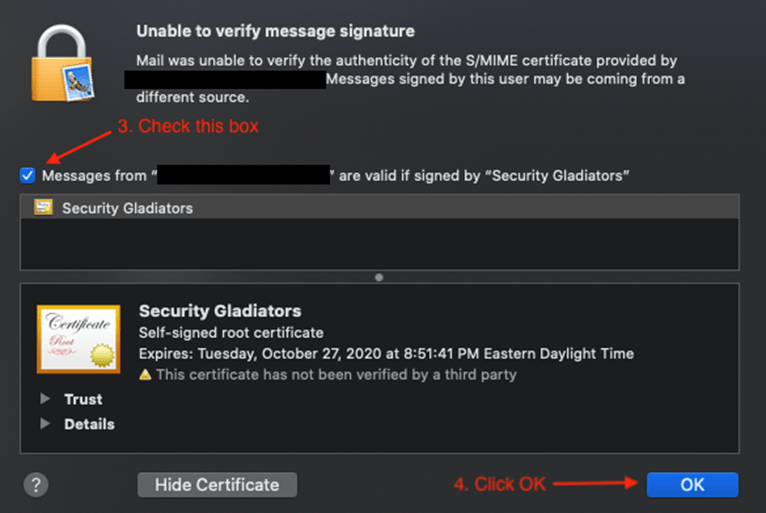
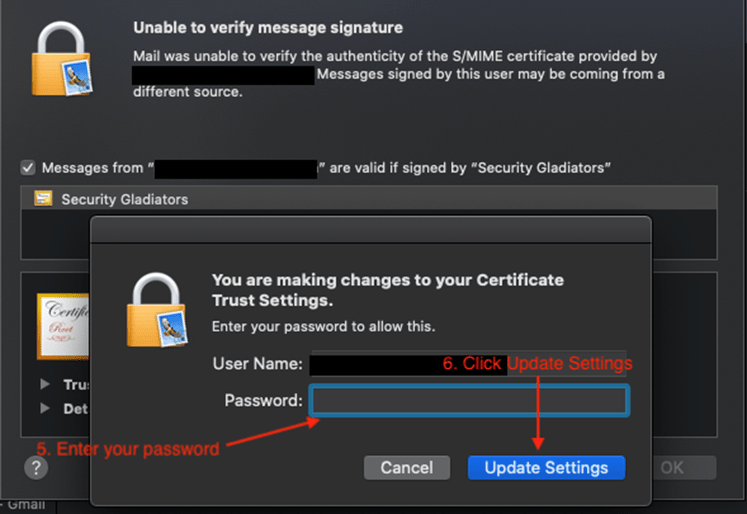
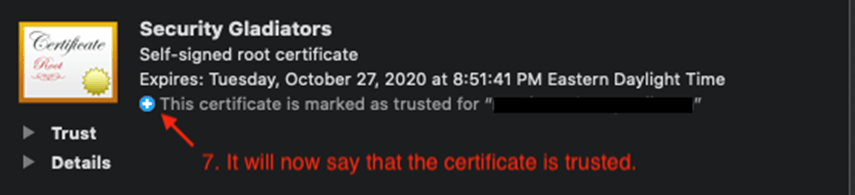
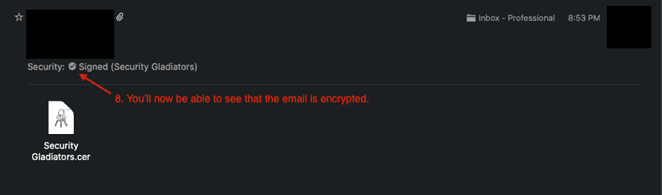
macOS
That being said, the process is very similar since Apple has been working to make switching between the two operating systems as seamless as possible.
In order to send encrypted emails, you must first find a way to have your recipient’s digital signature stored on your Mac after they send you an email with the signature as an attachment.
What happens here is that once you start composing an email message and input the email address of the recipient, the email app should show a checkmark icon.
Its appearance will indicate that the message you are about to send will have your digital signature on it. Now, right next to that signature icon, you should also see a lock icon.
The lock icon functions a bit different on macOS than it does on iOS. The lock icon on the iOS platform allows the user to choose which of the recipients will receive an encrypted email message and which will not.
On the macOS platform, the lock icon works on an all-or-nothing basis. Therefore, to send an encrypted message you have to have digital certificates for each of your recipients. Otherwise, you won’t be able to send any encrypted emails from your Mac.
On that note, we should also mention that you’re required to sign your email message only after you’re done writing the content of the messages. If the message gets altered after you’ve signed the email the recipient will see an untrusted certificate.
Android

As far as the Android platform is concerned, users have three options to choose from as to how they want to encrypt their emails.
The first option is the CipherMail application which allows users to receive and send S/MIME mail that’s encrypted within the default Gmail application.
The CipherMail application also supports a number of third-party email apps like K-9.
The CipherMail app follows the same digital certificate rules discussed in the previous sections of this guide. If you haven’t read these sections, the digital certificate rules essentially require you to exchange digital signatures with your email recipients in order to confirm that the emails are being received by the right person. Once this is done, you can use the encryption tools in your email client.
The second option is to use the PGP/MIME method. This method requires the user to have both the keychain and the email app to store digital certificates. While it does require a lengthier setup, the advantage of using this method is that you don’t have to receive a message from your contact containing their digital signature in order to be able to send them an encrypted email.
Of course, you’ll still need the digital signature, but you won’t have to go through the process of exchanging emails for the sole purpose of giving each other your digital signatures.
The third option is the OpenKeyChain option which is a free and simple keychain tool that you can use to safely store your contacts’ digital certificates.
OpenKeyChain reportedly works reasonably well with other mail apps like K-9 Mail, meaning that you should have no problem using it with your current email client. However, you should check their full list of compatible apps to be sure.
So, how do you use OpenKeyChain? You use it to create your own private and public keys.
To do that you have to input your password, name and email address. Once you do that, it’ll automatically generate private and public keys for you.

If you already have these keys from email encryption you’ve done in the past, you’ll need to import them. Fortunately, OpenKeyChain provides functionality for that.
OpenKeyChain also allows users to utilize an already generated key with various other apps and devices by exporting it.
Apart from that, OpenKeyChain can assist users who want to search for public keys belonging to other people online so they’re able to send the owner of those public keys an encrypted email message. The app automatically stores public keys that the user has added to their keychain.
Note:
If you want to use the OpenKeyChain app with your chosen email app, you’ll first have to open the settings menu of the email app and then select the OpenKeyChain app as the default provider of OpenPGP.The actual process will vary from app to app but should be fairly simple.
It shouldn’t go beyond digging through the app’s settings menu in order to find the proper options.
With that said, you should keep in mind that there are many email applications that still don’t support encryption, one of which is Gmail.
Web-Based Email Clients
Services like Gmail are considered web-based email clients. For such services, it’s usually recommended to use the MIME/PGP encryption solution.
This is recommended because MIME/PGP solutions are far easier to incorporate than the S/MIME solution used in some of the methods discussed above.
Note:
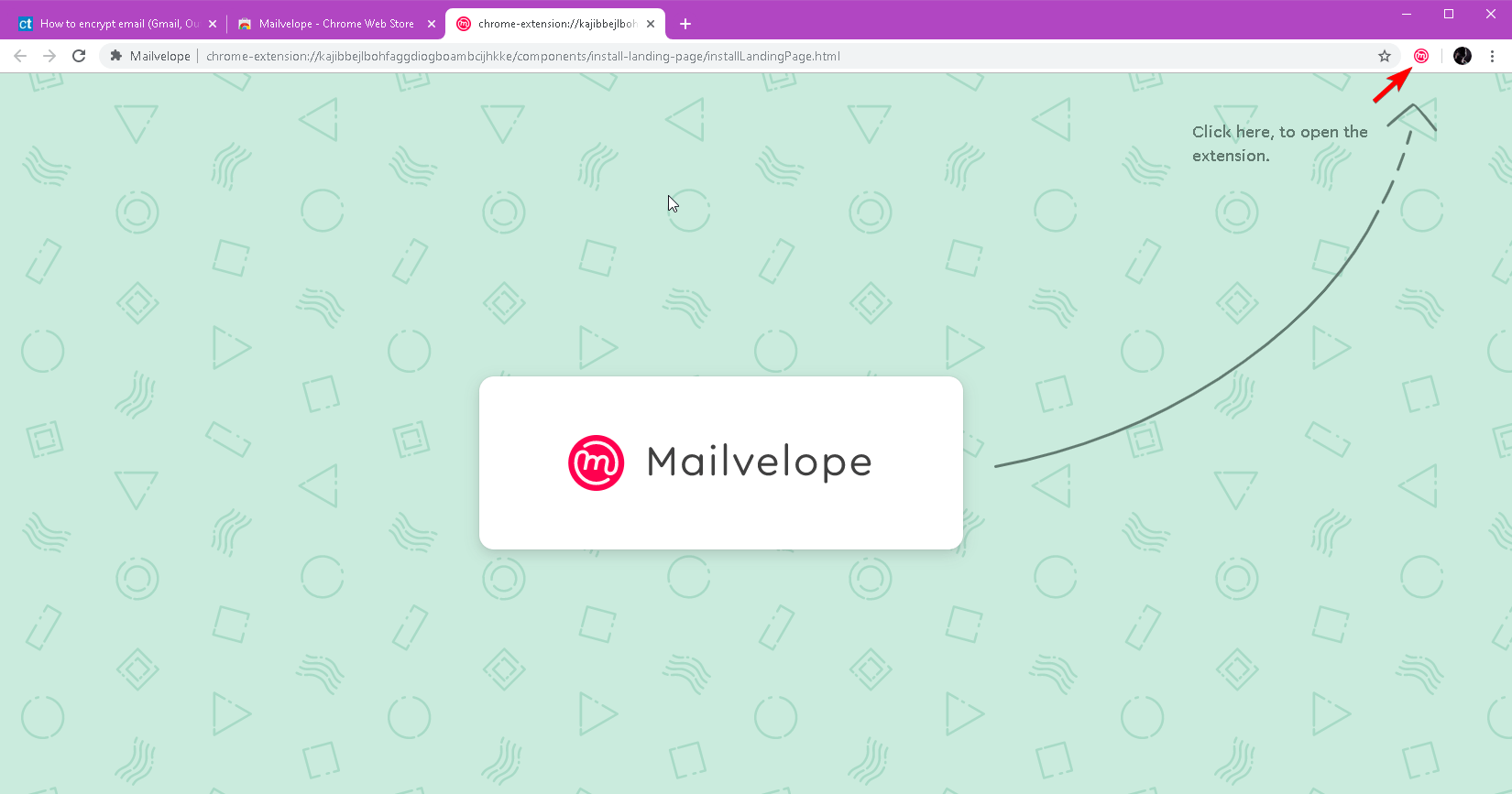
As far as this tutorial is concerned, we will mainly make use of the Mailvelope Chrome extension to enhance Gmail.You should keep in mind that most web browser extensions tend to work similarly to Mailvelope and follow essentially the same fundamental principles.
If you’d rather not use Mailvelope some good alternatives are GNU Privacy Guard, GPGTools and EnigMail.
To get started you need to install the browser extension of the service you’d like to use and then open the options menu.
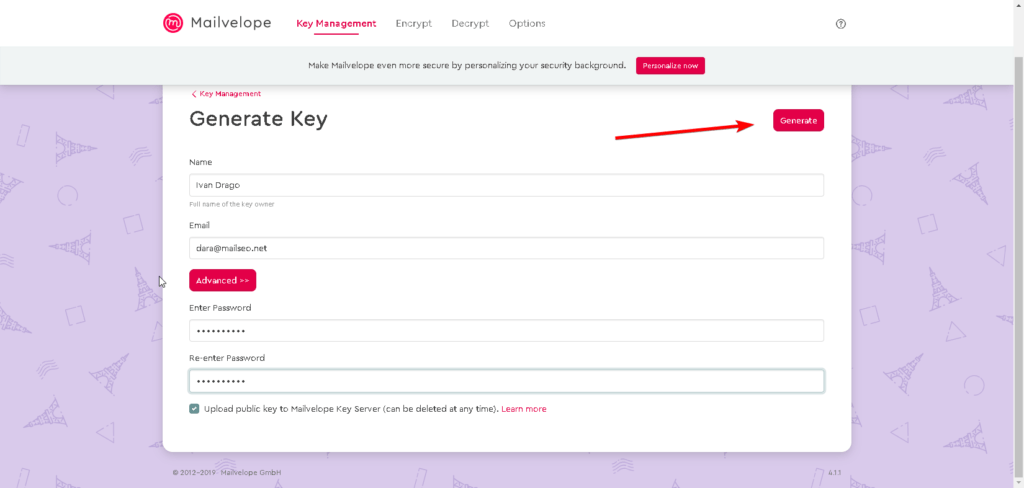
The best place to start is the section where you can generate your own key.
Enter your full name along with a password and your email address. After that click on Generate.
The majority of email encryption browser extensions have a built-in key generator and a key ring. For users who already have access to a key, just import it using copy and paste.
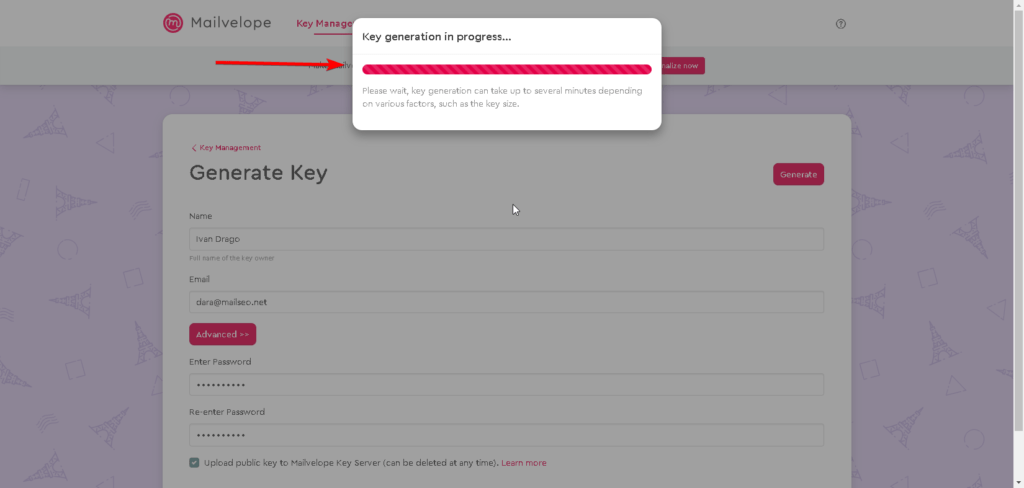
If you’ve followed along so far you should now have an encryption key.
You should know that the encryption key doesn’t do you any good if no one can use it to send you an encrypted email message.
To make your key public so it can be found by those looking to send you an email, you’ll need to find a keyserver.
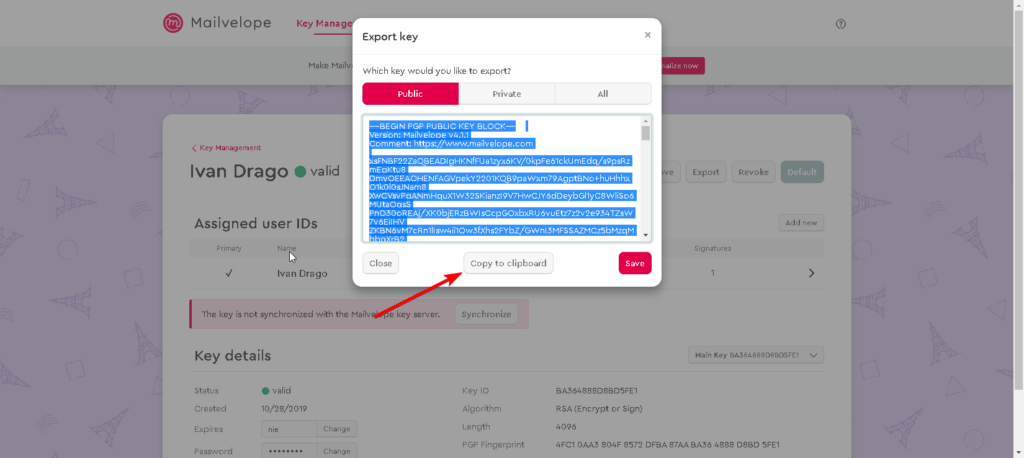
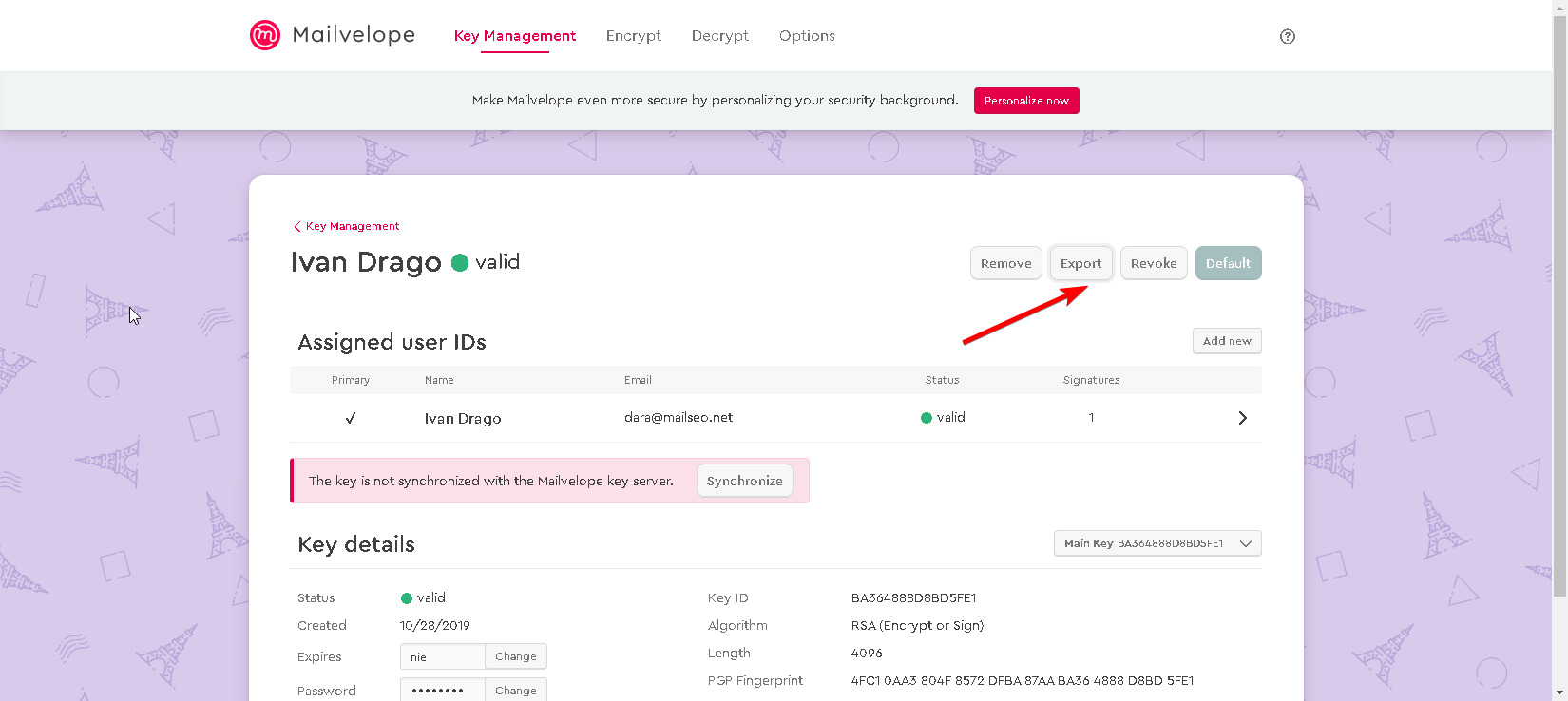
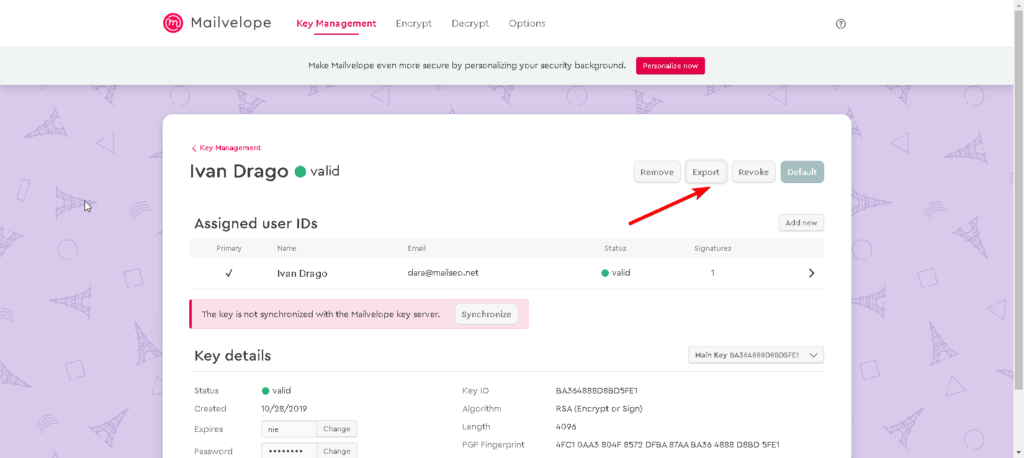
To upload your key to this keyserver, you need to go to the settings menu of Mailvelope and then navigate to the Display Keys option.
Click on the key you just generated and copy it.
You can also use the Export option while you’re here to see your public key in plain text.
You can then copy it for future use in a readable format.
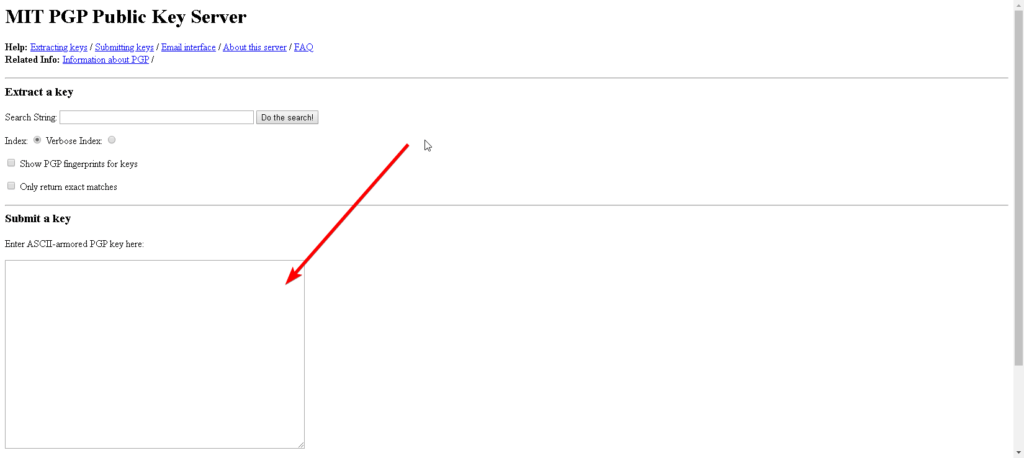
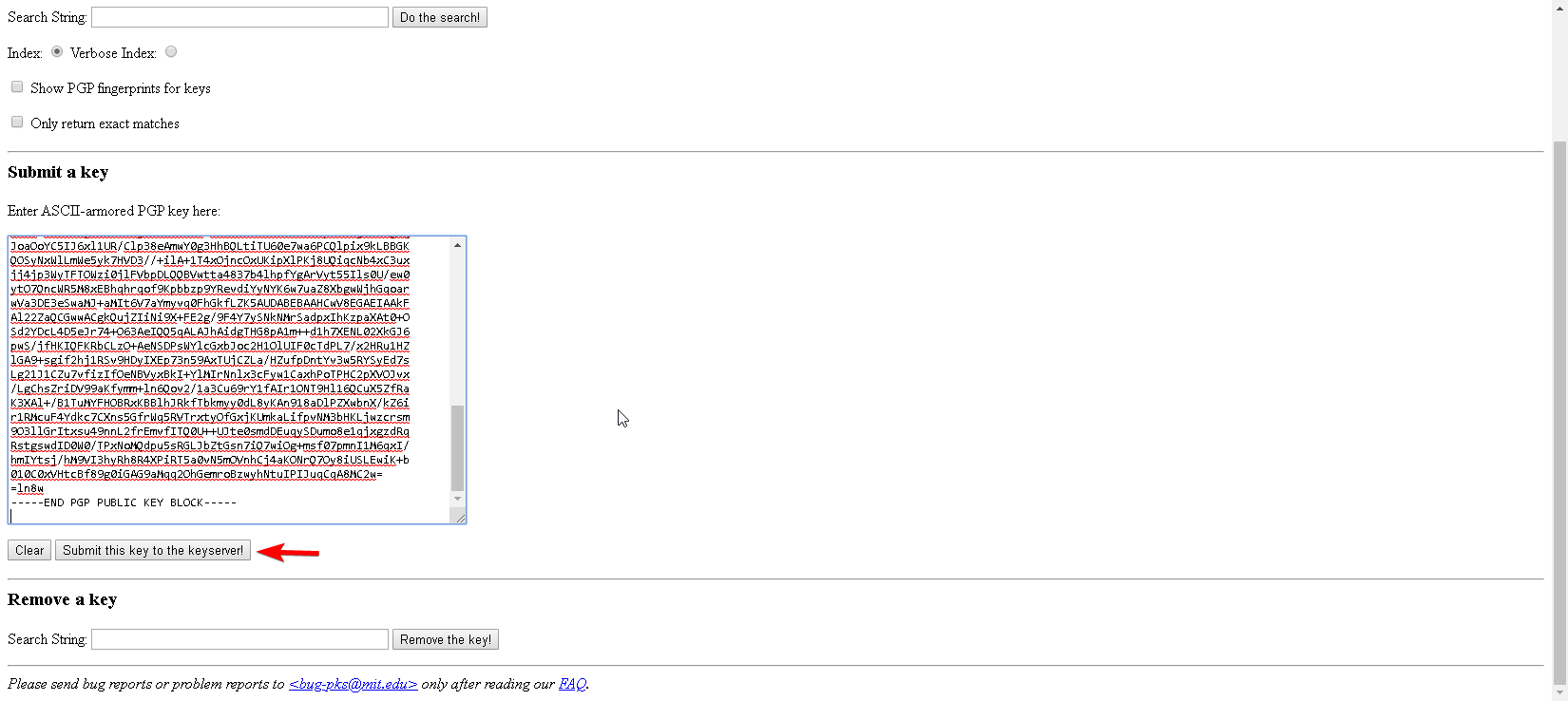
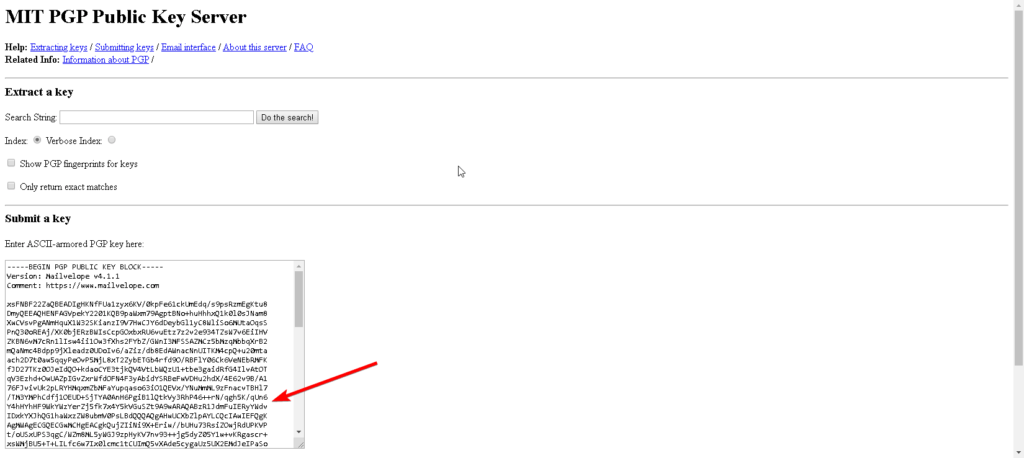
Once you’ve copied your key, go to the MIT keyserver page and paste it into the Submit a key field.
After pasting your key there you need to press the Submit button.
When that’s done, you need to make your way back to the MIT keyserver homepage.
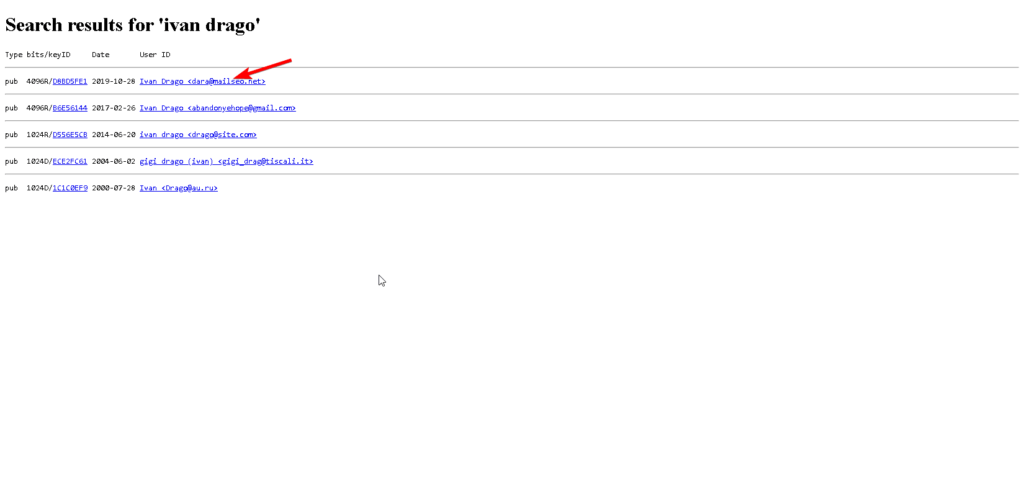
From there, search for the exact name that you entered.
If you’ve done everything right and the upload has completed, you should see your public key.
In addition to your key itself, you’ll also see a key ID both on the MIT listing page and the Mailvelope settings. Note it down. It can come in handy if your name matches someone else’s.
You can use the search function on the MIT keyserver to search for other people’s public keys. If you click the key ID of a person, you should see their key in plain text.
Just copy the key and then paste it into the section labeled Import in Mailvelope. That should add the key to your own keyring and you’ll be able to send encrypted emails to the key’s owner.
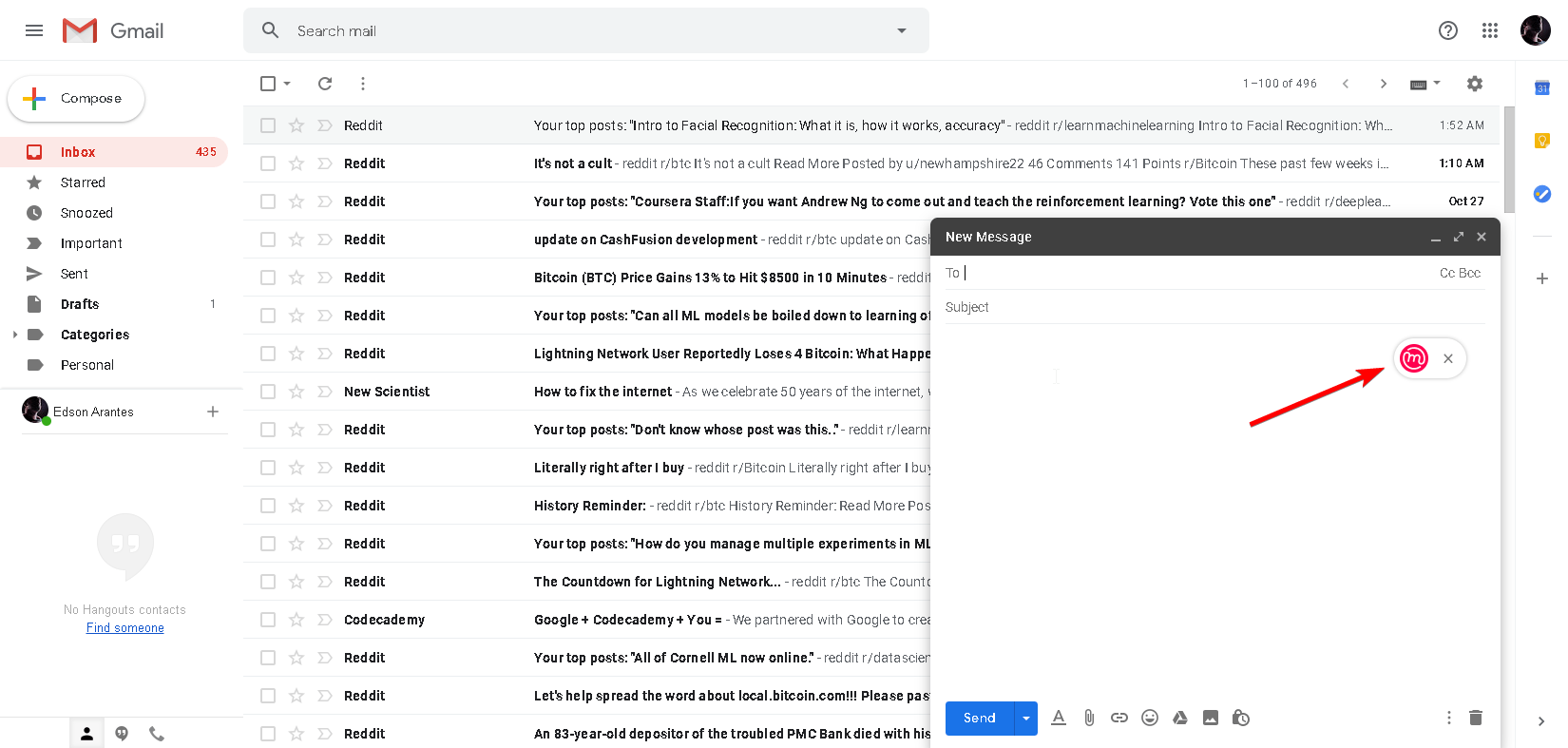
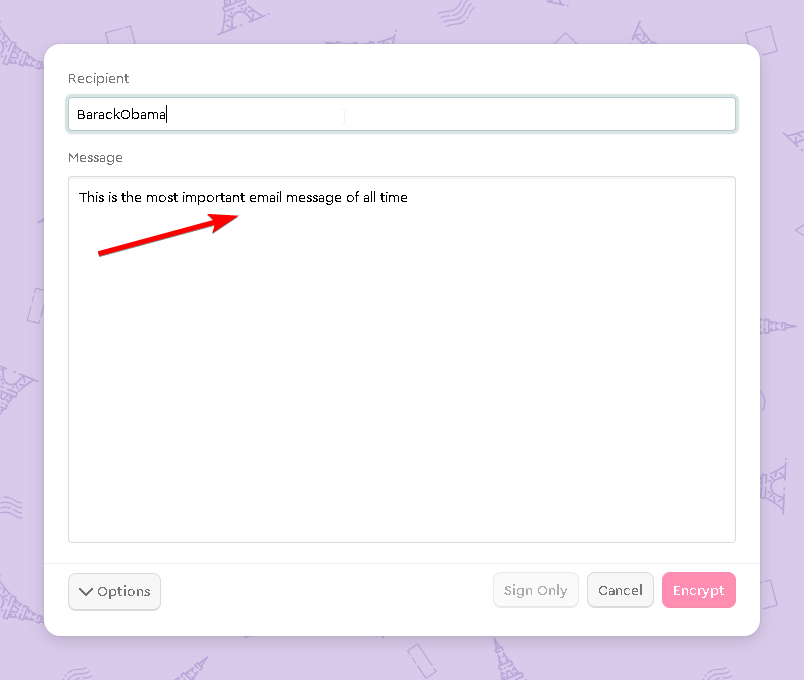
Mailvelope comes in handy here as it’s able to add a button to your Gmail email composer which opens a new window.
You can use the window to type your message that you want to encrypt.
Then when you’re finished, just click the button that says Encrypt and select your recipient.
Then you can transfer the entire encrypted message to your Gmail interface.
Do take note that the recipient of the message will have the need for some PGP decryptor app or a web browser extension installed on their end.
Upon receiving an encrypted email, your browser extension will automatically recognize the message. It will then offer to decrypt the message for you. If you’re using Mailvelope, you’ll just need to click the icon that appears over the encrypted text and entered your password to decrypt it.