A replay attack is a type of man-in-the-middle attack in which a hacker intercepts and retransmits data in an attempt to gain access to that data. Replay attacks are exceedingly common because after intercepting a transmission from a network, a hacker doesn’t need specialized expertise to decrypt the information.
Replay attacks are not limited to credit card transactions alone but can take many various forms. Fraudsters can imitate real users and accomplish any fraudulent act with an effective replay attack. However, replay attacks have a detrimental impact on businesses because these attacks cause breaches in data security, which leads to increased frustration from existing clients.

Aside from the apparent dangers replay attack can impose, there are limits to what hackers can achieve through the assaults alone. Because attackers can’t change the provided data without accessing the network, the attack’s effectiveness is restricted to repeating the previous activity.
Table of Contents
What Is the Definition of Replay Attack?

A replay attack is a security breach in which data is stored without permission and then transferred to fool the receiver into performing false identity verifications, duplicate transactions and other actions.
The 1983 film “War Games” demonstrated how naive and weak cryptography systems might be fooled. To gain access to a system, a cracker, for example, can record and playback the voice of an authorized individual. If the hacker employs digitized information, this replay attack can be boosted.
Even more powerful DNA-based computer security systems can be deceived, as shown in the 1997 film “Gattaca.” The film depicts a futuristic scenario of a genetically flawed man who desires to fly in space, so he adopts the appearance of an athlete who is genetically capable of pursuing his dream. The idea behind this movie introduced the concept of replay before it became a technical term.
What Is the History of Replay Attacks?

A replay attack is a kind of man-in-the-middle attack, a concept that dates back to the late 18 century. For example, Guglielmo Marconi (living from 1874 to 1937) was a Nobel Laureate whose career included early work in the radio transmission field and what became known as Marconi’s Law. Professor Fleming, Marconi’s mentor, showed how a message could be transferred wirelessly from one end to the other. Maskelyne, an inventor and magician, functioned as the middleman in the process, transmitting a new, updated message using his receiver. Professor Fleming was probably not amused that a substantial exhibition of wireless technology resulted in an unwanted signal from a “man in the middle,” which he likely received as a complete surprise.
Since the 1980s and 1990s, when man-in-the-middle attacks became widespread, many new complex processes have been developed to mitigate the attack’s effects.
How Are Replay Attacks Generated?

Replay attacks are generated when an attacker eavesdrops on communication between two systems or parties. To break into the system, the attacker utilizes a technique that involves resending a transmission. The hacker only needs to grab and decode the communication sent over the network. He doesn’t even have to read or comprehend the message to resend it as is.
An example of replay attack generation is when there is fraudulent eavesdropping in financial transactions. For instance, “Dean” has a financial transaction with “Tom.” To inform Tom about the transaction, Dean sends an encrypted message to him. Tom receives the funds after Dean transfers them. Unfortunately, an attacker intercepted Dean’s initial notification message, which was resent to Tom. Tom thinks the notification is still from Dean, and the funds are transferred again. This time, however, the funds are sent to the attacker.
How to Prevent Replay Attacks?

Prevention of replay attacks can be achieved with a one-time password and other sophisticated measures. When a one-time password is used for a short period, it expires. During the authentication process, a one-time code can help create credibility between the two parties interacting with each other. The efficacy of this on-time code is that before a successful log-in, the code checks to confirm both parties use the exact match.
Timestamping all messages is another measure to prevent replay attacks. This measure involves using solid digital signatures to prevent hackers from resending information multiple times, thus minimizing the possibility for an intruder to intercept and resend the data.
Note:
A data backup plan is also a preventive measure to this interception. Data backup aids in the restoring local files in the event of a system breach and prevents data leaks caused by violations that can encode and corrupt local database records.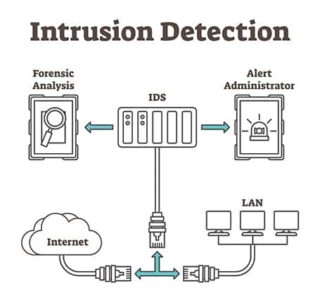
The use of intrusion detection systems (IDS) is of high importance in preventing replay attacks. When a security breach strikes, IDS tools immediately detect and notify of the attack. It responds to the replay attack as soon as possible and quickly controls the damage through network security. Some advanced intrusion prevention systems, such as SIEM, also proactively activate network breach response procedures in a network breach.
Because wireless connections are one of the main avenues of replay attack, having a secure wireless network is an evident approach to prevent replay attacks. Modifying the AODV (Ad Hoc On-Demand Distance Vector) protocol is one technique to enhance wireless connections.
Another proven prevention measure is the use of session ID, in which the transmitter and recipient make a unique arbitrary session key that only one transaction can use.
How Are Replay Attacks Used?

Hackers use replay attacks to achieve their malicious acts, which could range from fraud to financial theft to other nefarious activities. For example, attackers can use replay attacks to attack the network, gather otherwise restricted data or execute a repeat transaction.
Another purpose of a replay attack could be impersonation or deceit. For example, a valid routine transaction to transfer funds from Tom’s account to Dean’s account could be replicated by an attacker in an attempt to send more money than Dean authorized.
What Are the Common Techniques in Replay Attacks?
The conventional techniques in replay attacks are listed below.
- Kerberos prevention technique: During protocol exchanges between the user and the server, Kerberos implements a time authenticator. It also checks the ticket’s lifetime and, most importantly, the user’s timestamp. The message will be rejected if the authenticator’s timestamp isn’t within five minutes of the server’s time. This is because the maximum duration that may be accepted between users and servers is five minutes. However, the timing can be changed.
- One-time passwords (OTP): A code that can only be used once for a transaction. With the user’s OTP program, the authentication server operates on similar credentials in OTP-based security features. The use of OTP is based on the idea that each OTP is valid for 10 minutes or one successful activation, depending on which comes first.
- Sequencing: Authentic messages are numbered, and the recipient will refuse to accept packages not in the correct order. As a result, internal delay or duplication attacks are prevented.
- Random session key: The session key enables both parties to have secured and closed-end transactions using time-bound and process-bound code.
What Is a Biometric Replay Attack?

A biometric replay attack occurs when a hacker steals a victim’s biometric data, mainly in template form, while the data is being transmitted across a network. The hacker then uses the stolen data to imitate the target and obtain unapproved access.
Biometric replay assaults are dangerous since the victims cannot change their biometrics or the templates linked with their biometrics easily. Two-factor biometric authentication systems can be used to protect against biometric replay attacks.
This is important:
The only comprehensive, robust authentication software is SAASPASS, which helps handle all digital and physical access demands securely and conveniently with the help of mobile phones and other compatible devices.Because biometric replay attacks are not recoverable, these threats are dangerous and can be exploited forever, affecting the victim’s reputation. Biometric playback might potentially result in job loss or humiliation in front of friends and relatives. Once the stolen information is exposed online, the victims will be subject to various cyberattacks, even if the replay platform wipes the information.
What Are the Examples of Replay Attacks?
Some of the examples of replay attacks are cited below.
Crime Replay

Hackers post personal information about their targets on the internet and instigate others to hurt the victim.
Neal Horsley, an anti-abortion activist, compiled the contact details of abortion providers and publicized them on the Nuremberg Files website in the late 1990s and early 2000s. That list was branded a “hit list” by him. So far, eight doctors from the Nuremberg list have been killed. The website praised the victims of such assassinations and urged pro-life activists to keep killing doctors on the hit list.
Revenge Replay
Hackers post their targets’ publicly recognizable information on the internet to embarrass them.
Curt Schilling, a former Major League Baseball pitcher, took vengeance on those who made sexually abusive comments about his daughter on Twitter in March 2015. Schilling tracked down the real people behind the troll Twitter accounts and revealed their valid names online. One bully was fired from his job, and another was suspended from his community college due to the incident. Other targets whose identities were not revealed apologized on social media over fears about the attacks. Schilling employed replay attacks for online vengeful criminal punishment.
Faulty Replay

A faulty replay can occur when hackers are not attentive enough in searching or selecting victims, thereby exposing the information of another individual. The consequences of this defective replay attack are identical to others, including harassment, loss of life, loss of employment and a tarnished reputation.
Sunil Tripathi, an innocent student, was mistakenly labeled as a suspect in the Boston Marathon bombing by vigilantes on Reddit in 2013. According to his family’s social media page, Tripathi mysteriously disappeared, and his corpse was discovered in the sea near a park in Rhode Island. His death was considered a suicide, and people attributed the event to public humiliation caused by the faulty replay.
VIP Replay
In a VIP replay, a hacker discloses a celebrity’s sensitive information, such as credit card details, social security number, email address or phone number.
Swatting Replay

The term “swatting” refers to a different type of replay. When someone falsely accuses someone of a crime, police (or a SWAT squad, ergo “swatting”) are dispatched to the victim’s residence to harass them. Doxxing, on the other hand, can often be fatal for the victim.
Tyler Barriss was involved in a confrontation with two other gamers, Casey Viner and Shane Gaskill, in an online video game in December 2017. According to NBC News, Viner challenged Barriss to swat Gaskill, and Gaskill accepted the challenge by disclosing his last address, which was now occupied by the family of an unrelated man named Andrew Finch. A group of tactical police officers was deployed to Finch’s house, and one ended up fatally shooting him.
What Are the Statistics about Replay Attacks?
Some statistics about replay attacks are mentioned below.
- Replay attacks are a type of man-in-the-middle threat, which accounts for 35% of exploitation activity in IBM’s X-Force Threat Intelligence Index.
- About 95% of HTTPS servers could be subjected to a man-in-the-middle attack, per Netcraft data.
- Only one-tenth of companies have HTTP Strict Transport Security in place to prevent threats like replay attacks, according to W3Techs.
Is Replay Attack Illegal?

Replay attacks are illegal since they gather users’ private and sensitive information without the victims’ knowledge or agreement. Replay attacks are a type of hacking that is disapproved of in almost all countries.
There is, however, ethical hacking, which is a countermeasure to attackers’ illegal hacking. Ethical hacking is typically used by the owners of websites and applications to ensure the services withstand any external attack.
What Are the Laws Regarding Replay Attacks?
A replay attack is unacceptable in most countries, and different security policies are being implemented to mitigate replay attacks.
The following steps are employed under the U.K. GDPR (General Data Protection Regulation):

- Personal data must be processed safely using relevant technological and functional safeguards.
- Any password arrangement used must be acceptable for the processing’s unique contexts.
- Examine whether any alternatives to passwords are available.
- Every password mechanism must guard against security breaches and replay assaults “brute force.”
- To safeguard against frequent attacks, choose an appropriate hashing technique to store your passwords.
- For safety, use two-factor authentication.
How to Protect Yourself from a Replay Attack

Here are some of the ways to protect yourself from a replay attack.
- Use one-time passwords
- Use time-specific session keys
- Limit failed login attempts
- Use digital signatures
- Reject duplicate messages
- Use secure wireless networks
Does HTTPS Secure the Server from a Replay Attack?

Yes, if the server is set up for this, HTTPS can protect a given server from replay attacks. The usage of message authentication codes (MAC) in HTTP can efficiently accomplish this.
Using the best HTTPS certificates for any online transaction guarantees protection and secured data exchange without any replay attack. HTTPS also ensures data is encrypted over the internet. Because only the server and the user know the decryption keys, HTTPS makes sure that only the server and the user can share and access data.
What to Do If You Become a Victim of a Replay Attack?
These are helpful tips to consider if you become a victim of a replay attack.

- Speak with someone you can trust.
- Keep a log of any incidents that occur.
- Change your passwords for all of your online activities.
- Any illegal or compromised credit should be closed.
- Make a report to your local police department.
- Consider what additional types of personal information could be in danger.
- If you suspect you’re being tracked, think about changing your email address and internet service provider. On your PC and mobile devices, use data encryption software.
Is a Replay Attack Man-in-the-Middle Attack (MitM)?

Yes, the replay reaction is a form of man-in-the-middle (MitM) attack. A man-in-the-middle attack is a broad term that refers to any assault in which a hacker intercepts traffic between two servers. Anyone reading transmissions of the network could be the “man in the middle” who is eavesdropping.
Hackers can also use a man-in-the-middle attack to damage data, snoop on people and disrupt networks. With this method, hackers may listen in on any conversation and steal any data sent across a compromised channel.
Is a Replay Attack a Passive Attack?

In a passive network assault, a system is observed and occasionally checked for potential vulnerabilities and loopholes. However, a passive attack aims to gather information about the device being hacked; no direct action is taken against the target. Wireshark, a traffic analysis tool, is a good example of this.
Cyberattacks can be either active or passive. For example, an attacker tries to change the content of messages in an active attack. In a passive attack in network security, an attacker monitors and copies the target’s communications and could use that information to commit fraud. Also, in an active attack, the victim is notified, whereas, in a passive attack, the victim is not informed.
A replay attack is passive since no active data alteration occurs in transmission, and it is online, meaning the attacker captures data during the verification process.

