A phishing attack is when a hacker attempts to get their victims to reveal information by providing them with fraudulent links or software. The types of phishing attacks differ based on the particular technique the attackers employ to carry out the phishing. The types of phishing attacks are usually grouped based on criteria such as the frequency of occurrence and the level of the threat.
How the various types of phishing attacks are grouped is listed below:
- Most popular phishing attack: Email phishing
- Most technical phishing attack: Pharming
- Most evasive phishing attack: Spear phishing
- Most expensive phishing attack: Whaling/CEO fraud

The different types of phishing used by attackers are discussed in more detail below:
Table of Contents
1. Email Phishing

Email phishing, sometimes called deception phishing, is one of the most popular types of phishing attacks. This type of attack involves fraudsters posing as reputable brands to send mass emails to users in a bid to steal login details or personal data.
The primary aim of email phishing is to trick users into performing a particular action such as clicking malicious links that lead to compromised websites to steal personal data or install malicious files. For example, a malicious link could lead to a fake login page to steal the victim’s login credentials when they attempt to log in. The installation of malicious files can infect users’ systems with malware.
Email phishing typically works by creating a sense of urgency through the emails sent to scare users into falling victim to the attack. The techniques used in email phishing are:

- Use of shortened links and redirections: To avoid suspicion, phishing attackers use shortened URLs to evade the Secure Email Gateway (SEG). After the email is delivered, attackers use “time bombing” to redirect users to malicious websites and to redirect them back to legitimate websites once the phishing attack succeeds.
- Combining benign and malicious code: Attackers combine benign and malicious code during the creation of fake websites to evade Exchange Online Protection (EOP). This allows the attackers to replicate the JavaScript and CSS code of a reputable company’s login page to steal the credentials of users.
- Use of legitimate links: Attackers include legitimate links in phishing emails to evade email filters. This can be done by including the real contact information of the company that is being impersonated.
- Use of few words in email: Scammers use very few words in phishing emails to avoid detection. Instead of using a lot of text, scammers can attach an image that contains malicious code.
- Tweaking brand logo: Some email filters can detect malicious logos by scanning the HTML attributes of the logo. To avoid being detected, attackers tweak an HTML attribute such as the color of the logo.
Note:
Users can detect phishing emails by looking out for generic salutations and misspellings in texts or links, confirming the contact information in the email, and checking if the email address of the sender contains the wrong domain. To prevent falling victim to email phishing, users should avoid emails that have grammar errors or misspelled words. Users should also avoid clicking on short links and ignore emails with an image and very little text.
A recent example of email phishing happened at Elara Caring, a U.S. healthcare provider, in December 2020. The attacker targeted two employees and gained access to their email accounts, exposing the personal information of more than 100,000 senior patients, including Social Security numbers (SSNs), insurance details, bank information and more.
In September 2020, attackers sent out phishing emails encouraging companies to update partner contracts by downloading malicious documents. To make the campaign appear real, the attackers made the malicious documents appear to be hosted on Dotloop, but clicking the document redirected users to a sham Microsoft login page.
2. HTTPS Phishing

HTTPS phishing involves the use of Hypertext Transfer Protocol Secure (HTTPS) in malicious links used in phishing emails. Most organizations now use HTTPS instead of HTTP because HTTPS is generally considered to be safe and represents legitimacy. Cybercriminals now leverage this to launch phishing attacks.
The primary aim of HTTPS phishing is to steal the personal data of website visitors by making a malicious website look legitimate. One of the major techniques used by attackers is the popular “padlock sign” next to the URL. This prompts users to think the malicious website is legitimate.
HTTPS phishing is mostly part of email phishing attacks since it involves the use of malicious links to redirect users to malicious websites. HTTPS phishing also uses hypertexts to hide the real URL and redirect users to fraudulent websites.
Note:
Users can identify HTTPS phishing by looking out for shortened links and hovering over hyperlinks to see the real URLs. To protect against HTTPS phishing, users should avoid clicking on hypertexts or delete them. Users should also avoid clicking on shortened URLs and only click on the full URL where every part can be seen.
A good example of HTTPS phishing is PayPal scams. Attackers send emails to PayPal users urging them to click on a link to rectify a particular issue with the users’ accounts. Once the link is clicked, the users will be redirected to a fake PayPal login page which attackers then use to collect login credentials and divert funds from the victims’ PayPal accounts.
Another example is the phishing attack discovered by Cofense. Although the campaign started as email phishing, URLs were used to complete the attack. The email that was sent out impersonated a security awareness training provider and warned users not to miss the deadline to complete compulsory training by clicking on the malicious link. Users that complied were redirected to a phishing kit that utilized a sham Outlook on the web (OWA) login page hosted on a Russian domain to steal Microsoft login details.
3. Whaling/CEO Fraud

Whaling or CEO fraud uses open-source intelligence (OSINT) to get the name of a company’s CEO or top-ranking official by checking the company’s website or social media pages. The primary aim of whaling is to carry out wire fraud or W-2 phishing.
The whaling technique used by attackers involves impersonating the CEO or top-ranking official of an organization using a similar email address. The attackers then send an email to the organization authorizing a wire transfer. The attackers follow up with a phone call to confirm the email request which may convince the recipient it is the CEO’s directive. The hoax email can also be used to launch a W-2 phishing attack by requesting the W-2 information of all the organization’s employees to file fake tax returns on behalf of the employees or to leak the information.
Note:
Whaling can be identified if the fraudulent email received was sent to a personal email account and not a work email account. Whaling can also be detected if the request of the email is strange. For example, if the CEO or top-ranking official of an organization had never sent a request through email or never communicated through email, then it would be highly suspicious if an employee receives a supposed email from them.
Most whaling attacks are successful because top officials don’t participate in security awareness training. To counter whaling, organizations should make the training compulsory for everyone, including company executives. Organizations can also defend against whaling by including multi-factor authentication (MFA) in the process of financial authorization so executives won’t be able to authorize money transfers via email alone.
A well-known case of a whaling attack was carried out against Facebook and Google in 2013 and 2015 by Evaldas Rimasauskas. Rimasauskas sent fake invoices posing as a legitimate Taiwanese company and eventually stole a total of $122 million from both companies.
Another case of whaling occurred in November 2020 against the co-founder of Levitas Capital, an Australian hedge fund. The attacker sent an email containing a malicious Zoom link to the co-founder which planted malware on the corporate network of the hedge fund. The hedge fund almost lost $8.7 million, but the attacker still managed to get away with $800,000.
4. Vishing

Vishing, otherwise called voice phishing, is the use of phone calls to scam victims by impersonating a legitimate institution such as a government agency or a bank. The primary aim of vishing is to get victims to divulge important information such as credit card details which cybercriminals then use to steal funds.
The vishing technique used by attackers involves posing as a legitimate organization and creating a sense of urgency during attacks. For instance, an attacker may pose as an employee of an auto insurance company stating that the user’s auto insurance has expired. The attacker can then request the user’s credit card details for “renewal.”
Most vishing attacks use ID spoofing which enables the attacker to appear to be calling from a company or institution’s real phone number with the same area code as the target. During calls, attackers use what is known as “the mumble technique” which involves attackers mumbling answers when asked questions by targets hoping the “answer” would be enough to use to pull off the scam. When targeting company employees, attackers may pose as a member of the company’s tech support team and use confusing technical terms like “data switch upgrade” so the employee is convinced to provide the requested information.

Vishing can be identified if the attackers give a sense of urgency. Vishing can be also detected by checking the phone number of the caller. If the phone number is from a strange location, blocked or private, it’s possibly vishing. Also, if the caller can’t provide useful information to verify the identity of the institution the caller is representing, it is likely a vishing attempt. Vishing can also be identified if the time of the call coincides with an event and requests for personal details. For example, if a user gets a call from the IRS during tax season, then it is possibly a vishing attempt.
Users can defend against vishing by knowing the security rules of the organizations with which their company is in business. For example, most institutions clearly state clients will never be called to ask for personal details. Therefore, if that happens, users will know it is vishing and will not provide personal details. If an institution has called to request information in the past, clients should reach out to the institution via legitimate means to confirm the initial call. Companies can protect employees from vishing by organizing security awareness seminars.
In September 2020, some patients of the Spectrum Health System were victims of vishing. The attackers posed as employees and either used flattery or threats to coerce patients into providing personal data such as member ID numbers, funds or access to personal devices.
Vishing attacks were carried out against residents of Montgomery County, Virginia in which attackers called to say the SSNs of the residents were suspended and access to bank accounts would be restricted unless SSNs were provided.
5. Smishing

SMS phishing, alternatively called smishing, is very similar to vishing but uses texts instead of phone calls to perpetrate fraud. Smishing is also similar to email phishing as attackers send texts posing as trusted organizations. The texts usually contain malicious links to redeem fake coupon codes or lottery tickets. The primary aim of smishing is to steal the credentials of targets or install malware on the targets’ devices.
Techniques used by attackers to carry out smishing include embedding malicious links in texts to install nefarious applications, deploy ransomware or provide access to the attackers. The malicious links could also redirect targets to compromised websites to collect the personal data of the targets. Attackers also send out texts posing to be the tech support of a trusted company, instructing targets to contact customer service through a particular phone number. The attackers then pretend to be customer service representatives to trick targets into providing personal information.
Note:
Targets can identify smishing by checking the area code of the text and comparing it with their contact list. If the area code appears strange, then it is possibly a smishing attempt. Targets can also detect smishing if the companies they are in business with usually send emails to notify of a promo and not texts.
Targets can defend against smishing by contacting the company in question to verify the authenticity of the texts received. Targets should also neglect texts from unknown or strange phone numbers.
In September 2020, a smishing campaign was carried out by attackers disguised as the United States Postal Service (USPS). The attackers sent out texts urging recipients to view new details of an incoming USPS delivery by clicking the link in the texts. The malicious links redirected targets to several malicious websites to steal Google account details.
Apple users were targets of a smishing campaign that used a fake Apple chatbot to send text messages. Recipients were notified that they won a chance to test the new iPhone 12 and were instructed to pay a delivery fee. The malicious links in the texts led to a fake web page that was used to steal credit card details.
6. Angler Phishing

Angler phishing is the use of social media platforms like Twitter, Facebook and Instagram to carry out scams. The main aim of angler phishing is to obtain sensitive information by tricking targets into clicking malicious links.
Angler phishing is mostly carried out by creating fake social media accounts to make it easier to steal private data by posing as someone the target knows or impersonating the customer service of a known brand. Angler phishing mostly uses the notifications and direct messaging features on social media apps to reach out to targets.
Note:
Angler phishing can be detected if users receive notifications that they were added to strange posts. Users can also identify this type of phishing by looking for clues the account may be spoofed like weird usernames and profile photos. Angler phishing can be identified if a direct message from an unknown or known user contains suspicious links.
To protect from angler phishing, users should immediately block any requests or notifications to join strange groups. Users should also not click links from strange accounts and block such accounts immediately. In the case of customer support, users should make sure to use a brand’s legitimate social media account by checking the profile details such as the number of followers, verification badge and if the account follows or is followed by familiar people.
In August 2019, scammers sent direct messages to some Instagram users, notifying the users of an image copyright violation and demanded the users fill out a form to prevent suspension of their accounts. Another case of angler phishing happened to an Instagram user who received a message from a fake North Face account claiming copyright infringement. This user was asked to follow a link to a fake Instagram website that could have been used to steal the user’s data.
7. Pharming

Pharming is a type of phishing that involves the hijack of a Domain Name Server (DNS), which is the server used to convert URLs from natural language to IP addresses. When users enter a web address, the hijacked DNS redirects users to a malicious IP address that may be identical to the real one. The primary aim of pharming is to obtain the private information of victims.
Pharming is mostly carried out by hijacking a DNS server to redirect website visitors to malicious websites. Cybercriminals can also carry out pharming by sending emails with malicious codes to tweak the host files on users’ computers. This will cause any link entered on such computers to be redirected to malicious websites to steal information.
Note:
Pharming can be identified by carefully checking a website to look for any form of inconsistency such as different fonts, background colors or misspellings. Also, if a URL contains HTTP and not HTTPS it means the connection is not encrypted and could lead to a malicious website.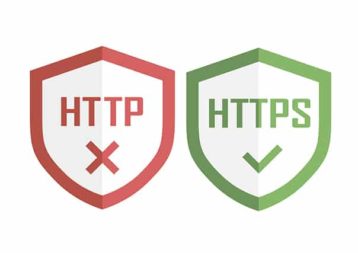
To protect against pharming, users should ensure URLs have no typos and contain HTTPS and not HTTP. Users should change their default Wi-Fi password to a stronger one to avoid DNS poisoning. Installing antivirus software is another way to defend against pharming. Organizations should regularly carry out security upgrade recommendations from a reputable internet service provider (ISP).
In 2013, 300,000 small businesses and home office routers were victims of a pharming campaign that used man-in-the-middle (MitM) to hijack the DNS settings of the victims and redirected users to malicious sites. In 2019, an attacker created a fake Venezuelan humanitarian campaign website with the same IP address as the legitimate site. The personal details of volunteers entered on the real website were filtered to the fake one, resulting in thousands of users having their data stolen.
8. Pop-up Phishing

Pop-up phishing is the use of pop-up ads to inject malicious code into the user’s system. Pop-up phishing aims to install malware or carry out credit card fraud.
Pop-up phishing works through the installation of malicious code on website pop-ups or notifications. Visitors to a compromised website will get pop-up messages saying a website wants to send notifications. If the user clicks “Allow” then malware will be installed on the user’s computer. Pop-up phishing can also work by showing users a notification of a fake security issue, instructing the users to call a particular phone number for tech support.
Note:
Pop-up phishing can be recognized when pop-up messages ask users to allow a website to send notifications or show a strange security warning. A user’s web browser automatically switching to full-screen mode is also an indicator of pop-up phishing.
Users can defend against pop-up phishing by blocking fraudulent pop-up messages. Users can also reach out to the company in question to confirm the authenticity of the pop-up notification.
A good example of a pop-up phishing attack involved attackers showing a website pop-up message to a MacBook user, informing the user of an issue with the MacBook and providing a phone number to call. The attacker posed as an Apple support representative and asked the user to allow a remote connection to diagnose the user’s MacBook. The attacker then told the user their AppleCare had expired and that they needed to renew it for $499. The user was then directed to a fake site to pay using credit card details.
9. Clone Phishing
Clone phishing is a type of phishing attack in which scammers create a malicious duplicate of a recent email a user receives and then re-send it from a source that appears reputable. Clone phishing aims to collect useful private credentials from victims.
Scammers perpetuate this type of phishing by first researching the platforms that organizations use to exchange messages and then create fake messages that appear to come from those platforms. For instance, many institutions use DocuSign to exchange digital contracts. Scammers will then create malicious emails for this platform. The links or attachments of the original email will be substituted with malicious links or files. The scammers will now re-send the malicious email, stating that an issue with the links or attachments in the original email is the reason for re-sending.
Note:
Clone phishing can be spotted by hovering the cursor over the links from both emails to check for discrepancies. Clone phishing can also be spotted through grammar errors and misspellings or if the name of the sender is incorrect. Recipients can also detect clone phishing if the email requests information the service provider has never asked for before.Users can avoid becoming victims of clone phishing by installing anti-phishing software that detects and removes malicious emails. Installing firewalls to run background checks and remove malicious links is another way to fight clone phishing. Recipients can also call the sender of the first email to confirm the authenticity of the second email.

A typical example of clone phishing involves receiving two identical emails with the second email containing malicious links or files. Clicking on links in the second email will lead users to a fake website that appears to have the correct URL.
Clone phishing is common since this type of phishing attack utilizes emails, which are the primary tool used in phishing attacks. Clone phishing will likely remain common as email continues to be a popular method of communication.
10. Evil Twin

Evil twin phishing is the use of a fake Wi-Fi network that appears to be legitimate to steal credentials from users by eavesdropping. Evil twin phishing is mainly used for stealing the credentials of users.
Evil twin phishing works by using a fake wireless access point to spy on internet traffic. The attackers then collect the login credentials of users that connect to the fake Wi-Fi network. If users visit other websites while connected to the attacker’s network, the details entered on such websites, especially unsecured websites will also be collected by the attackers.
Note:
Users can spot evil twin phishing if the Wi-Fi network activates an “unsecured” notice. Any unfamiliar network that requires login credentials should be considered a possible evil twin attack.
Users can avoid falling victim to evil twin attacks by adhering to warnings when trying to connect to a Wi-Fi network. Users can also avoid being victimized by disabling the auto-connect feature to avoid automatically connecting to fraudulent networks. Users can also make use of a secure VPN to encrypt their data. If possible, users should avoid connecting to public Wi-Fi networks.
In September 2020, evil twin phishing was used by hackers to steal unique credentials and infiltrate the Wi-Fi networks of the U.S. Department of the Interior. Another example of an evil twin attack is the use of captive portals to steal the login credentials of users on public Wi-Fi networks that use web login pages.
11. Spear Phishing

Spear phishing is the use of malicious emails by cybercriminals to target employees of an organization by pretending to be another employee from the same organization. The aim of spear phishing is for targets to click on malicious links so the attackers can steal personal data.
Cybercriminals start a spear phishing campaign by using OSINT such as the corporate website or social media accounts of an organization to gather information about the employees of that organization. The attackers then impersonate employees using their real names, job titles, phone numbers or work emails to target other employees within the organization. To make the malicious email more convincing, the attackers make sure to use the email address format used internally by employees to exchange emails. Spear phishing attackers hide malicious content on cloud services like Google Drive and Dropbox to evade email filters since many organizations’ IT departments are less likely to blacklist those platforms.
Note:
Spear phishing can be identified if the name of the sender or the email address contain misspellings, or if the format of the email is different from the standard format used in the organization. Spear phishing can also be detected if emails contain links to cloud services such as Dropbox or Google Drive or to password-protected documents.
Organizations can defend against spear phishing by training employees to identify, avoid and report suspicious emails. Organizations should also install and update security software to scan all internal and external emails to identify, stop and remove spear phishing threats.
In September 2020, two spear phishing campaigns were launched by Chinese group TA413. The first attack targeted some non-profit organizations and European government institutions using a malicious WHO document. The second was against Tibetan dissidents using a PowerPoint presentation.
12. Watering Hole Phishing

Watering hole phishing is a complex strategy used by attackers to infect an organization with malware by tracking and infecting one or several websites the employees of an organization visit. The aim of watering hole phishing is to steal important data.
Watering hole phishing starts with attackers observing the websites visited by the staff of an organization. The attackers then find vulnerabilities in those websites to install malware that redirects users to malicious sites or creates similar, but fake websites. Once the malware is installed, the attacker will have access to all the data entered on those websites.
Note:
Watering hole phishing can be detected using web gateways or anti-malware software. There are also cybersecurity tools used to identify websites used for watering hole phishing.
Organizations can defend against watering hole phishing by installing trusted anti-malware software to stop malware and rootkit installation or website redirections. All third-party websites should be properly scrutinized before allowing employee access. Advanced threat protection such as behavioral analysis should be put in place to detect watering hole threats early.
From late 2018 to early 2019, LuckyMouse, a cyber-espionage group, launched watering hole attacks throughout China. In 2019, Asian charities and religious groups were victims of a watering hole attack. The attack was launched by telling victims to update Adobe Flash.
What Are the Unique Questions for Phishing Attacks?
Some frequently asked questions about phishing attacks are listed below.

- What is phishing?
- How can I avoid phishing attacks?
- How can I identify a phishing attack?
- What are the main features of phishing?
- What are the types of phishing attacks?
- What should I do if I’m attacked?
- What is the best software to use against phishing?
- How does a phishing attack work?
- Why is phishing hard to spot?
- How does phishing work?
Security Gladiators has several resources to answer many of these questions.
How to Detect Phishing Attacks
Phishing can be detected using anti-phishing software. However, no software can provide 100% accuracy which makes knowing other methods to detect phishing attacks necessary.Phishing can be detected by scrutinizing emails, text messages, calls, domains, URLs and sender addresses. Some phishing sites are identifiable by the use of “HTTP” instead of “HTTPS” in their URL.

The lack of a unique company domain in the sender’s address helps detect phishing attacks. Emails that do not contain “@companyname.com” but rather “@gmail.com” are red flags that can aid the detection of a phishing attempt.
Phishing can be identified through requests for sensitive information, grammar errors, misspellings and the inclusion of non-requested attachments. As these attacks are common, it is important to check all of these things to protect against phishing attacks.
What Are the Best Anti-Phishing Software?
Some of the best anti-phishing software are detailed below:
Avanan Cloud Email Security

Avanan stops phishing attacks from reaching email inboxes by 99.2%, and the ones detected in emails are blocked fully 100% making Avanan the best anti-phishing software. Avanan Cloud Email Security protects cloud email from phishing attacks on platforms including G Suite/Google Workspace, Office 365 and Slack.
Avanan Cloud Email Security uses an advanced machine learning algorithm that thoroughly scans emails for over 300 signs of phishing. The software utilizes an API-based integration to examine email history between two parties to determine the level of existing trust, which makes it easier to identify malicious content or impersonation.
Companies with fewer than 500 employees are charged $4/month per user for Avanan Cloud Email Security.
Area 1 Horizon Anti-Phishing Service

The Area 1 Horizon Anti-Phishing Service is a cloud-based service that prevents phishing attacks on websites, emails and networks. This service protects users from malware, ransomware, business email compromise (BEC) and other phishing attack techniques, making it one of the best.
Area 1 Horizon has a single platform that uses APIs for operations as well as analytics and recommendations features. Area 1 Security combines small pattern analytics and high-speed web crawling to identify launch points of phishing attacks before they are activated. Using this feature along with a deep contextual analysis of the user’s email, web or network allows the software to block targeted phishing before the attacks can wreak havoc. Area 1 Anti-Phishing service can process millions of emails and web clicks monthly and successfully blocks 99.997% of incoming malicious emails. Phishing attacks are identified and stopped an average of 24 days prior.
Area 1 clients are charged based on the number of users with access to the software on a 12-month or 36-month basis. Prices range from $25,000 to $225,000 for 12-month plans while 36-month plans span $67,500 to $607,500.
GreatHorn

GreatHorn is an email security platform that uses API to protect Google Workspace and Microsoft 365 platforms from phishing attacks.
GreatHorn uses cloud-native API to successfully stop phishing attacks automatically in real-time. The automation of this anti-phishing software removes the occurrence of human-reported phishing omissions or mistakes. GreatHorn is the next-level email security tool for cloud-based emails like Office 365 and Google Workspace (formerly G Suite). This security platform offers messaging security for companies and apps like Slack.
Users of GreatHorn attest to a 90% reduction in response time to phishing attacks and a success rate of 96%.
Pricing is custom and must be requested from GreatHorn’s website.
What Are the Criteria of a Phishing Attack?
The primary goal of a phishing attack is to get the targets to take action that gives the attackers access to the targets’ personal data. This phishing definition captures every pointer to the activities of phishing attackers. The main features of a phishing attack are the use of malicious links, the request for sensitive or personal information, a sense of urgency, grammar errors or misspellings, spoofed websites and fake domains or URLs.

Several experts and thought leaders in software security have emphasized how phishing works and how it can be avoided. For example, the Federal Trade Commission, in one of the publications released on software security said, “When internet fraudsters impersonate a business to trick you into giving out your personal information, it’s called phishing. Don’t reply to email, text, or pop-up messages that ask for your personal or financial information. Don’t click on links within them either – even if the message seems to be from an organization you trust. It isn’t. Legitimate businesses don’t ask you to send sensitive information through insecure channels.”
What Is the Most Popular Type of Phishing Attack?
The most popular type of phishing attack is email phishing which accounts for 96% of all phishing attacks worldwide. As of 2020, 75% of companies worldwide experienced phishing attacks and 65% of those attacks were through email phishing. From 2016 to 2020, email phishing grew by over 61%.
Which Phishing Attack Is Most Dangerous?
Spear phishing is more dangerous than other types of phishing. In 2020, 35% of all phishing attacks on organizations were through spear phishing. Spear phishing also accounted for 65% of the total number of targeted phishing attempts.
What Is the Difference Between Phishing and Vishing?
The major difference between phishing and vishing is that phishing is used by attackers far more than vishing. Phishing attacks more people and yields faster results than vishing. Phishing uses target and system vulnerabilities to launch successful attacks while vishing relies on the vulnerability of the target alone.

