Amplification attacks have emerged as a significant and concerning cyber threat in recent years. These attacks exploit vulnerabilities in the Domain Name System (DNS) to overwhelm target networks with an excessive influx of data, causing disruptions and potential damages. Despite their silent nature, amplification attacks pose a severe risk to individuals, organizations, and even critical infrastructure systems.
We will delve into the intricacies of amplification attacks and shed light on how they work. We will explore the role of User Datagram Protocol (UDP) in facilitating these attacks and discuss methods for detecting them. Additionally, we will examine the consequences of such attacks, including their impact on common targets like websites or online services. Furthermore, we will analyze various countermeasures that can be employed to prevent amplification attacks from occurring. By understanding the inner workings of these silent cyber threats and implementing appropriate defenses, individuals and organizations can better protect themselves against potential harm caused by amplification attacks.

Table of Contents
What Is a DNS Amplification Attack?
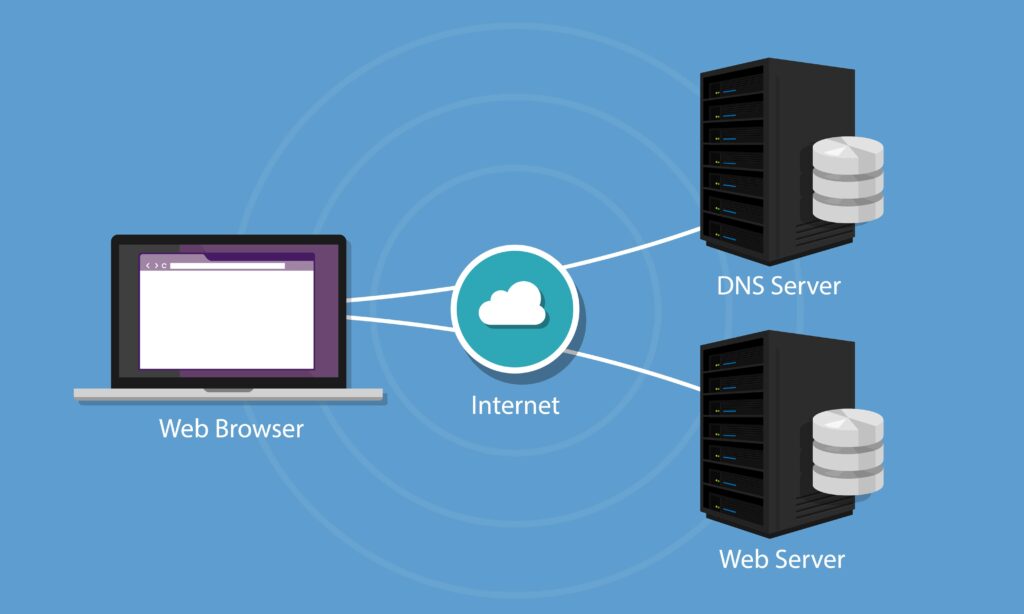
A DNS amplification attack involves exploiting the vulnerability of misconfigured DNS servers by flooding them with a high volume of requests, resulting in a significant amplification of traffic directed towards the target. This type of attack takes advantage of the nature of DNS resolvers, which can provide large responses using small queries. The attacker sends a request to a vulnerable DNS resolver, spoofing the source IP address as that of the target.
The DNS resolver then responds to this request with a much larger response, potentially several times the size of the initial query. By sending multiple requests from different sources simultaneously, an attacker can generate a massive amount of traffic that overwhelms the target’s network infrastructure and causes it to become inaccessible or disrupted. These attacks are commonly used in Distributed Denial-of-Service (DDoS) attacks and rely on misconfigured DNS servers and unsecured IP addresses to achieve their goals.
How Does a DNS Amplification Attack Work?
To understand how these attacks work, consider the following steps:
- Attackers first identify vulnerable DNS servers that can be used as amplifiers.
- These servers are typically misconfigured or lack proper security measures.
- The attacker spoofs their IP address to make it appear as if the requests are coming from the target server.
- The attacker sends a large number of DNS queries to multiple vulnerable servers, using the spoofed IP address of the target server.
- The DNS servers, believing the requests are legitimate, respond by sending much larger responses back to the target server.
By exploiting this vulnerability in DNS systems, attackers can generate a significant amount of traffic directed towards their intended target without directly initiating it themselves. This method allows them to amplify their attack and potentially overload the targeted server’s resources, leading to service disruptions or even complete downtime.
The Role of UDP in DNS Amplification Attacks
UDP (User Datagram Protocol ) is a crucial protocol in DNS amplification attacks, enabling attackers to exploit vulnerabilities and unleash overwhelming traffic on targeted servers. In a DNS amplification DDoS attack, the attacker sends a large number of spoofed UDP packets to vulnerable DNS servers, utilizing the reflection attack technique.
By exploiting the inherent design of the UDP protocol, which does not require a handshake or verification process between sender and receiver, attackers can easily send falsified source IP addresses to DNS servers. These servers respond by sending larger responses to the forged IP address, resulting in an amplification effect where small DNS requests generate significantly larger responses.
This amplification allows attackers to achieve high traffic volumes with minimal effort, as they only need to send a small number of initial requests. Consequently, these attacks overwhelm the target server’s resources, disrupting its normal functioning and potentially causing service outages for legitimate users.

What Are the Signs of Amplification Attacks
Amplification attacks can be challenging to detect because they often involve exploiting legitimate services and protocols to generate a large volume of traffic.
However, there are several signs and patterns that may indicate the presence of an amplification attack:
Significant Traffic Spike
A sudden and significant increase in network traffic is a common sign of an amplification attack. If you notice a rapid surge in incoming or outgoing traffic, it could be an indicator of an attack.
UDP Traffic Dominance
Amplification attacks typically use the User Datagram Protocol (UDP) because it’s connectionless and easy to forge source addresses. If you observe a high volume of UDP traffic, especially to services like DNS, NTP, SNMP, or SSDP, it may be a sign of an amplification attack.
Unusual UDP Port Activity
Look for unusual patterns of UDP traffic on uncommon or unexpected ports. Many amplification attacks target services running on well-known ports, such as DNS on port 53 or NTP on port 123.
High Packet-To-Byte Ratio
In an amplification attack, the response packets are usually much larger than the request packets. If you see a high packet-to-byte ratio, with small requests triggering large responses, it may indicate an amplification attack.
Abnormal Query Patterns
For attacks that target specific services like DNS or NTP, analyze the query patterns. Look for repetitive or unusual query patterns that may indicate malicious intent.
Consequences of Amplification Attacks
Below are some of the consequences of amplification attacks:
Service Disruption
Service disruption can have a significant impact on the availability and accessibility of online platforms, potentially causing inconvenience, frustration, and financial losses for businesses and users alike. Amplification attacks exploit vulnerabilities in the Domain Name System (DNS) infrastructure by sending small requests that result in large responses being sent to the targeted victim’s IP address. This flood of traffic overwhelms the victim’s network resources, leading to service disruptions and making it difficult for legitimate users to access the platform.
The consequences of service disruption caused by amplification attacks can be severe, including reputational damage for businesses, loss of customer trust, and potential financial repercussions due to downtime or decreased productivity.
Network Congestion
Another significant impact of these attacks is network congestion. In particular, a type of amplification attack known as DNS amplification can lead to severe network congestion. During a DNS amplification attack, an attacker spoofs the victim’s IP address and sends small queries to multiple open DNS resolvers with forged headers, resulting in large responses being sent to the victim’s IP address. As a result, the victim’s network becomes overwhelmed with excessive traffic directed towards it.
This influx of traffic leads to network congestion, causing delays and inefficiencies in data transmission across various systems connected to the affected network. Network congestion not only disrupts legitimate services but also provides an ideal environment for attackers to further exploit vulnerabilities and launch additional attacks.
Bandwidth Costs
Bandwidth costs can escalate significantly as a result of network congestion caused by amplification attacks, leading to a strain on resources and hindering efficient data transmission. Amplification attacks, work by exploiting vulnerabilities in the DNS system to generate a large volume of attack traffic. This flood of malicious traffic overwhelms the target network, resulting in congestion and an increased demand for bandwidth. The excessive amount of attack traffic consumes valuable network resources and forces organizations to invest in additional bandwidth capacity to handle the influx. Consequently, this incurs substantial financial costs for businesses and can impede their ability to transmit legitimate data efficiently.
Resource Exhaustion
Resource exhaustion occurs when the overwhelming volume of attack traffic associated with amplification DDoS attacks depletes valuable network resources, hindering efficient data transmission and imposing significant financial burdens on businesses. In an amplification attack, the attacker exploits vulnerable DNS servers or DNS resolvers to reflect and amplify a small amount of malicious traffic into a much larger volume directed towards the target. This results in a flood of incoming requests overwhelming the target’s network infrastructure, consuming all available bandwidth and processing power. As a consequence, legitimate users are unable to access the targeted services, leading to potential revenue loss and damaging the reputation of businesses.
Collateral Damage
Collateral damage, an unintended consequence of the amplification of DDoS attacks, can have far-reaching implications for businesses and their stakeholders. These attacks utilize vulnerable internet services to overwhelm a target network with massive amounts of traffic. As a result, collateral damage occurs as innocent bystanders suffer the consequences.
The impact of collateral damage can be significant, leading to prolonged service outages and disruptions for businesses, crippling their online operations. Internet service providers (ISPs) are particularly affected by these attacks, as they may face increased costs in terms of bandwidth consumption and infrastructure upgrades to cope with the massive influx of malicious traffic. Additionally, ISPs may experience reputational damage due to their inability to protect customer networks from these attacks.
Furthermore, collateral damage extends beyond just ISPs; it can also affect other organizations sharing the same infrastructure or hosting platform with the intended target. This includes cloud service providers who may find themselves inadvertently involved in amplification attacks and facing potential legal liabilities as a result.
What Are the Techniques Used in Amplification Attack

Here are some common techniques used in amplification attacks:
Spoofed IP Addresses
Attackers typically forge the source IP addresses of their requests to make it appear as though the requests are coming from the target’s IP address. This misdirection makes it difficult for the target to filter out malicious traffic.
UDP-Based Amplification
UDP (User Datagram Protocol) is connectionless and doesn’t require a three-way handshake like TCP. Attackers often exploit services that use UDP, such as DNS (Domain Name System) and NTP (Network Time Protocol), to send small requests that generate much larger responses. The attacker’s request is small, but the server’s response is significantly larger, amplifying the traffic directed at the target.
DNS Amplification
DNS servers can be used in amplification attacks because they respond with relatively large packets to small queries. Attackers send DNS requests to open resolvers with the victim’s IP address as the source, causing the open resolvers to send large DNS responses to the target.
NTP Amplification
Similar to DNS amplification, NTP servers can be exploited by sending small requests with the victim’s IP as the source. NTP servers respond with much larger packets, increasing the attack’s volume.
SSDP Amplification
SSDP (Simple Service Discovery Protocol) is used in network devices like routers. Attackers send small SSDP requests with the victim’s IP as the source to SSDP-enabled devices, which respond with larger packets.
Common Targets of Amplification Attack
Amplification attacks can target a variety of online services and entities. The common targets of amplification attacks include:
Websites
E-commerce sites, news portals, and other online services are often targeted to disrupt their availability. The goal is to overwhelm their servers and make them inaccessible to users.
Online Gaming Servers
Multiplayer online games and their servers are attractive targets for amplification attacks. Gamers often depend on low-latency connections, and an attack can disrupt gameplay and affect user experience.
Streaming Services
Video and audio streaming platforms may become targets, impacting the delivery of content to users.
Internet Service Providers (ISPs)
Attackers may target ISPs to disrupt internet services for an entire region or a specific customer base.
Content Delivery Networks (CDNs)
CDNs are responsible for distributing web content to users efficiently. An attack on a CDN can have widespread implications, affecting multiple websites and online services that rely on the CDN for content delivery.
What Are DNS Amplification Countermeasures
To counteract DNS amplification attacks, several countermeasures can be employed:
Restrict Open DNS Resolvers
One of the most effective measures is to restrict open DNS resolvers. Network administrators should ensure that their DNS servers only respond to requests from trusted sources, such as their own network or authorized clients. Open resolvers should be secured or closed to external requests.
Rate Limiting
Implement rate limiting on DNS resolvers to restrict the number of queries they can accept from a single IP address over a set period of time. This can help mitigate the impact of amplification attacks.
BGP Blackholing
Internet Service Providers (ISPs) and network operators can use BGP (Border Gateway Protocol) blackholing to redirect traffic destined for the target of a DDoS attack to a null route, effectively dropping the malicious traffic.
Anycast DNS Servers
Using anycast to distribute DNS servers across multiple geographically dispersed locations can help distribute the load and absorb some of the attack traffic. Anycast directs user requests to the nearest DNS server, which can improve response times and provide some level of redundancy.

Monitoring and Alerting
Implement monitoring and alerting systems to detect unusual DNS traffic patterns or a sudden increase in queries. This can help administrators respond quickly to an attack.
Firewalls and Intrusion Detection Systems
Employ firewalls and intrusion detection systems (IDS) to filter malicious DNS traffic and block known attack patterns.
Content Delivery Networks (CDNs)
Utilizing a CDN for DNS services can help distribute the load and protect against DDoS attacks by absorbing traffic and ensuring high availability.
DNSSEC (DNS Security Extensions)
Implement DNSSEC to add a layer of security to DNS by digitally signing DNS data. This can help prevent DNS cache poisoning and other DNS-related attacks.
Traffic Scrubbing Services
Some organizations subscribe to DDoS mitigation and traffic scrubbing services that filter and clean incoming traffic before it reaches their network, protecting against various types of attacks, including DNS amplification attacks.
How To Respond to Amplification Attack
Here are the tips that can help you respond to an amplification attack:
- Identify the attack source.
- Block or mitigate the attack traffic.
- Monitor network and traffic patterns.
- Use intrusion detection systems (IDS) and intrusion prevention systems (IPS).
- Engage with your Internet Service Provider (ISP).
- Implement source IP filtering.
- Review and adjust firewall rules.
- Opt for a DDoS mitigation service.
- Consider rate limiting or throttling.
- Improve overall network security.

Frequently Asked Questions
What Is the Purpose of an Amplification Attack?
The primary purpose of an amplification attack is to overwhelm a target’s network or system with a flood of data, causing it to become unavailable or slow down. These attacks are often used to disrupt online services or websites.
What Is the Difference Between Reflection and Amplification Attacks?
Reflection attacks use a third-party server to reflect the attack traffic toward the target, whereas amplification attacks use amplifiers to generate excessive response traffic. Amplification attacks are a subset of reflection attacks.
What Are Some Commonly Targeted Protocols in Amplification Attacks?
DNS (Domain Name System), NTP (Network Time Protocol), SNMP (Simple Network Management Protocol), and SSDP (Simple Service Discovery Protocol) are frequently targeted for amplification attacks due to their ability to amplify traffic.
Are There Legal Consequences for Launching Amplification Attacks?
Yes, launching amplification attacks is illegal in many jurisdictions and can lead to criminal charges. Laws against cyberattacks vary by country, but there are international agreements to combat cybercrime.
What Is a DNS Response?
A DNS response, also known as a DNS reply, is a critical part of the Domain Name System (DNS). The DNS is a hierarchical system that translates user-friendly domain names (like www.example.com) into IP addresses (like 192.0.2.1) that computers and network devices use to locate and connect to each other on the internet.
Conclusion
Amplification attacks are a serious concern in the realm of cybersecurity. Understanding how they work and implementing effective countermeasures is vital for protecting networks and systems from potential harm. Organizations must remain proactive in detecting and responding to these threats while also working collaboratively with ISPs and security professionals to ensure a safer digital environment for all users.
