There was never a time when the online world was safe, which is why online users are always striving to make digital lives more private and secure. One of the ways to keep abreast of all the latest trends and advancements in cybersecurity is to watch cybersecurity documentaries.
Cybersecurity is a general term that covers the technologies, controls, processes and application of technologies to secure data, devices, applications, networks and general computer systems against cyberattacks. Since the concept of cybersecurity is crucial to securing online communications, cybersecurity documentaries help online users of all sorts to understand the processes used to keep information and devices safe and private. Cybersecurity documentaries are a way for film producers to bring the obscure and often dry subject of cybersecurity to the masses.

On the other hand, online users should be watching cybersecurity documentaries on a regular basis to keep updated on the latest types of cyberattacks hackers have developed recently and what cybersecurity firms have done to counter such attacks. Cybersecurity documentaries also help users think about and eventually take the steps needed to have a secure and private online existence.
This guide will cover the best cybersecurity documentaries to watch online, as well as the overall themes and concepts presented in the genre. Readers will also learn more about the real-world benefits of watching cybersecurity documentaries and whether such titles offer trustworthy content.The best cybersecurity documentaries to watch are given below.
- The Great Hack (2019)
- Code 2600
- Hackers Wanted
- Hackers in Wonderland (2000)
- The Internet’s Own Boy: The Story of Aaron Swartz (2014)
- We Are Legion: The Story of the Hacktivists (2012)
- WannaCry: The Marcus Hutchins Story (2019)
- Risk (2016)
- Terms and Conditions May Apply (2013)
- Hacking Democracy (2006)
- Citizenfour (2014)
- DEFCON: The Documentary (2013)
- Snowden (2016)
- The Defenders (2018)
- Zero Days (2016)
Table of Contents
1. The Great Hack (2019)
The Great Hack is a cybersecurity documentary that explores the inner workings of Cambridge Analytica, a British company that used personal data acquired through questionable means at best to manipulate social media users ahead of the 2016 presidential elections in the U.S. The documentary was released on June 24, 2019.
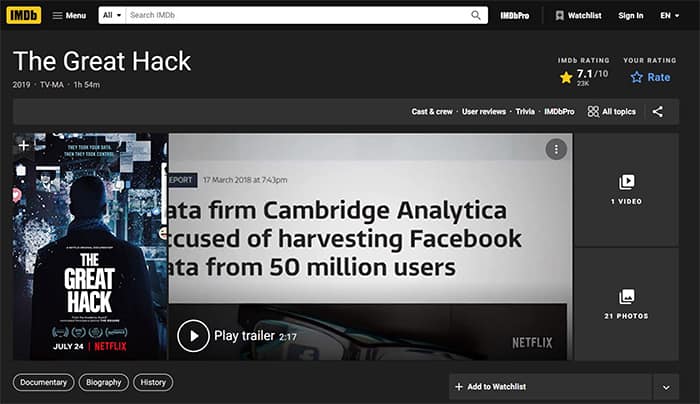
The Great Hack was produced by Karim Amer, along with Judy Kordin, Pedro Kos and Geralyn White Dreyfous. The documentary’s directors are Jehane Noujaim and Karim Amer. The cast includes Christopher Wylie, Roger McNamee, Julian Wheatland, Brittany Kaiser, David Carroll and Carole Cadwalladr.
Theme-wise, The Great Hack touches on the dark side of social media platforms like Facebook and how data companies like Cambridge Analytica can give rise to political and social unrest and affect the lives of people in the real world.
The subject of this cybersecurity documentary is less about pointing fingers at companies like Facebook and Cambridge Analytica and more about how decisions made by such companies can have consequences for users. The documentary essentially follows a person’s journey into finding out what and how social media websites like Facebook collect, process and use personal data.
Note:
This documentary is closely linked to cybersecurity conceptually as the field’s primary aim is to keep data safe and out of the hands of those who are not supposed to have access to the data in the first place.The Great Hack also deals with all the legal problems that can arise if a given user decides to reclaim user data and opt out of micro-targeting programs run by various social media platforms and marketing companies across the internet.
2. Code 2600
The Code 2600 is another cybersecurity documentary that deals with subjects such as the pervasiveness of information technology and the opinions of people who assisted in the rise of the internet, among other communication technologies.
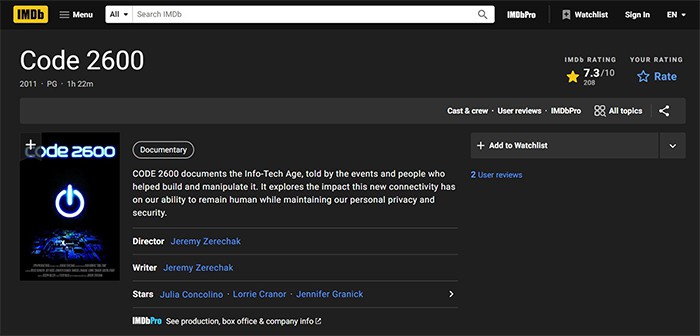
Code 2600 was released in April 2012 in the U.S., with Jeremy Zerechak as the producer and director. Cast members of Code 2600 included Julia Concolino, Lorrie Cranor, Robert Vamosi, Bruce Schneier, Vartan Sarkissian, Jennifer Grannick, Phil Lapsley, Marcus Ranum, Gideon Lenkey, Jeff Moss and Eric Michaud.
Code 2600 tackles themes surrounding the age of information technology and discusses the role of different events and people who were not only involved in the development of the digital landscape but also manipulated various digital communication channels. Code 2600 also covers the impact of all the new digital connectivity tools on humans’ lives—both on the internet and in physical interactions.
The content presented in Code 2600 is closely related to cybersecurity since the topics covered mainly deal with connectivity tools affecting user security and privacy in the digital world. Code 2600 also touches on the ramifications of mass-scale data collection and obsessive usage of various social media networks. In addition to that, Code 2600 examines niche cybersecurity topics such as privacy invasion, identity theft and the evolution of modern cyberattacks.
3. Hackers Wanted
Hackers Wanted is an unrated cybersecurity documentary covering the life events of Adrian Lamo, the famous hacker who broke into computer networks of companies such as Microsoft, Yahoo and The New York Times.
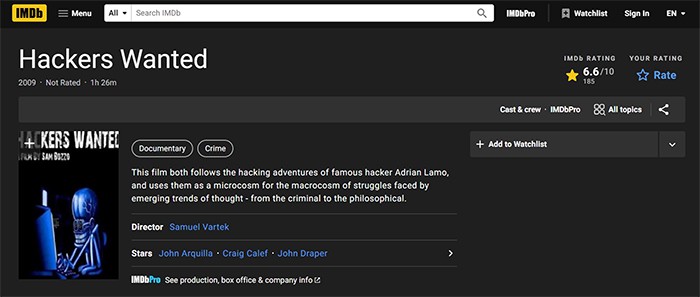
The release date for Hackers Wanted is generally considered to be Jan. 1, 2009, but this cybersecurity documentary was never officially released and instead was leaked to the media.
Dana Brunetti (and according to some sources, Kevin Spacey as well) acted as producers of Hackers Wanted. Sam Bozzo directed Hackers Wanted while the main cast included names such as Steve Wozniak, Kevin Spacey (voice only), Peter Shipley, Kevin Rose, Marcus Ranum, Kevin Lee Poulsen, Tod Pagle, Robert Lyttle, Lep Laporte, Mario Lamo, Adrian Lamo, John Arquilla, John Draper, Craig Calef and Frank Harrel.
The main theme of Hackers Wanted (or Can You Hack It?) focuses on the origins of hacking and how people already working in the field of information technology got into hacking. Hackers Wanted makes Adrian Lamo and other figures in the hacking community the primary subjects of the documentary and then compares hackers with other historical figures. This cybersecurity documentary doesn’t just touch on the criminal side of hacking and hackers but also philosophical ideas that arise because of illegal activities in the digital age.
Note:
Hackers Wanted falls under the cybersecurity documentary genre because the film is about how hackers go about compromising computer systems and the fallouts of cyberattacks.4. Hackers in Wonderland (2000)
Hackers in Wonderland is a British cybersecurity documentary that films interviews given by hackers based in the United Kingdom.
The release date of Hackers in Wonderland is Jan. 1, 2000. Russell Bames acted as the producer and director, and the documentary includes just two personalities, Marc Rogers and Coldfire (a real-life hacker).
This cybersecurity documentary’s primary subject is hacking and how hackers can be grouped into three main categories: white hat, gray hat and black hat hackers. Hackers in Wonderland also explores how not all cases of hacking involve cyberattacks and malware infections. The documentary takes a detailed look at the lives of various hackers and the objectives of hacking.
The Hackers in Wonderland documentary is closely related to cybersecurity since the movie discusses famous hackers who got into legal trouble for various hacking jobs. Absorbing the film’s content can help cybersecurity professionals have a deeper understanding of how hackers compromise secured systems and how to mitigate different hacking techniques.
5. The Internet’s Own Boy: The Story of Aaron Swartz (2014)
The Internet’s Own Boy: The Story of Aaron Swartz is a cybersecurity documentary that details the story of Aaron Swartz, who was considered a programming prodigy.
The release date for The Internet’s Own Boy is June 27, 2014, and Brian Knappenberger is credited as the producer, director and writer. This cybersecurity documentary has appearances from Ron Wyden, Ben Wikier, Trevor Timm, Susan Swartz, Robert Swartz, Noah Swartz, Ben Swartz, Aaron Swartz, Matt Stoller, Taren Stinebrickner-Kauffman, Bryan Stevenson, Christopher Sogholan, David Sirota, Stephen Shultze, Alec Resnick, David Segal, Elliot Peters, Quinn Norton, Tim O’Reilly, Zoe Lofgren, Carl Malamud, Lawrence Lessig, Brewster Kahle, Orin Kerr, Stephen Heymann, Peter Eckersley, Cory Doctorow, Cindy Cohn, Tim Berners-Lee and Gabriella Coleman.
The Internet’s Own Boy’s main theme is about Swartz’s life and contributions in developing the basics of internet protocol RSS and some of his groundbreaking work in areas like politics and social justice. Swartz’s work towards ensuring information access across the internet eventually led to a legal battle lasting more than two years. Sadly, the final stages of the legal proceedings saw Swartz die by suicide at age 26.
Note:
This documentary relates to ideas found in cybersecurity in the sense that technology should enable people to establish justice and uphold the privacy of the end-user, which is in stark contrast to the status-quo position in tech hubs like Silicon Valley.6. We Are Legion: The Story of the Hacktivists (2012)
We Are Legion: The Story of the Hacktivists is a cybersecurity documentary that presents the beliefs and operational structure of the hacktivist collective known as Anonymous.

The release date of We Are Legion: The Story of the Hacktivists is Oct. 30, 2012, and Brian Knappenberger is the producer, director and credited writer of the documentary. Cast members of We Are Legion include names such as Anon2World, Deth Veggie, Grandmaster Ratte, Commander X, Chris Wysopal, Mike Vitale, Vendetta, Richard Thieme, Ryan Singel, Quinn Norton, Brain Mettenbrink, Steven Levy, Jericho, Tim Hwang, Gregg Housh, Homocarnula, Mercedes Haefer, Peter Fein, Josh Covelli, Joshua Corman, Gabriella Coleman, Stanley Cohen, Adrian Chen, Barrett Brown, Aaron Barr, Julian Assange and Anonyops.
We Are Legion primarily tackles themes related to hackers rising up against perceived injustices of the digital world, such as online censorship and copyright abuse. The main subjects of the film are noteworthy hackers, who discuss how different life events affected the way the community as a whole operates.
The We Are Legion documentary is relevant to cybersecurity because the movie sheds light on self-proclaimed hacktivists who launch cyberattacks against organizations and governments worldwide, particularly in the U.S. and the Middle East. On the other hand, the same hacktivists try to guard personal privacy on the internet, which is a major component of topics that make up cybersecurity.
7. WannaCry: The Marcus Hutchins Story (2019)
The WannaCry: The Marcus Hutchins Story is a cybersecurity mini-documentary as the movie formed an episode of the TV series Hacker: Hunter.
Officially, the WannaCry: The Marcus Hutchins Story aired on Oct. 23, 2019, as episode two of season one. The director and producer is Hugo Berkeley, with Normal Life Pictures acting as the production company of the entire series. The film’s main cast includes David Menkin and Tarah Wheeler.
WannaCry: The Marcus Hutchins Story tackles themes such as cybercrimes and the stories of people behind those cybercrimes. Following that, the main subject is about the famous WannaCry ransomware attack and how a British computer security researcher, Marcus Hutchins, managed to stop the ransomware’s spread. The episode lasts about 31 minutes.
The WannaCry: The Marcus Hutchins Story documentary has particular relevance to cybersecurity as the entire episode is about how the WannaCry cryptoworm started, spread and was stopped by Hutchins, who initially started work on the ransomware from a vacation hotel room. All of these events can teach cybersecurity professionals about how new cyberattacks evolve and how security experts can respond quickly.
8. Risk (2016)
Risk is another feature-length cybersecurity documentary that covers the story of Julian Assange, the editor-in-chief of WikiLeaks, and how the maker of the documentary sees Assange’s life events.
The film was released on May 12, 2017, with Laura Poitras as the director. Producers of Risk include names such as Brenda Coughlin, in addition to Poitras. Risk’s cast members include Assange, Slavoj Zizek, Johannes Wahlstrom, Donald Trump, Katerina Suvorova, Edward Snowden, Vaughan Smith, Jeff Sessions, Adam Schiff, Barack Obama, Fidel Narvaez, Mathia Nalappan, Helmut Martin-Jung, Chelsea Manning, Gavin MacFadyen, Helena Kennedy, Kristinn Hrafnsson, Amy Goodman, Lady Gaga, Tamer Gadalla, Laura Ellsberg, Daniel Ellsberg, Roger Dingledine, Anderson Cooper, James Comey, Amal Clooney, Hillary Clinton, Louis Bladel, Christine Assange, Ana Alban, Laura Poitras, Erinn Clark, Jennifer Robinson, Renata Avila, Joseph Farrell, Jacob Appelbaum and Sarah Harrison.
The main subject of the Risk documentary is Julian Assange, founder and head of the famed whistleblowing outlet WikiLeaks. Risk takes a look at the conditions under which Assange has had to live as a result of forming an organization that leaks sensitive data and how being confined to a single building has threatened the existence of Assange’s organization.
Risk is relevant to cybersecurity as WikiLeaks releases information that is supposed to be protected. The only way for WikiLeaks to leak sensitive information is to have a source that obtains the information by bypassing cybersecurity measures in a given organization. Hence, cybersecurity professionals can watch Risk to have a better idea about how organizations like WikiLeaks work.
9. Terms and Conditions May Apply (2013)
Terms and Conditions May Apply is a cybersecurity documentary that presents viewers with the true cost of all the free online services that are popular today.
Terms and Conditions May Apply’s official release date is July 12, 2013, with Cullen Hoback as the producer and director of the documentary. In addition to Hoback, John Ramos and Nitin Khanna also worked as producers on the project.
The main cast of Terms and Conditions May Apply include Jon Stewart, Eddie Izzard, Greg Grunberg, Stephen Colbert, Jennifer Valentino Devries, Russell Tice, Edward Snowden, Jay Rockefeller, TImi Robertson, Mark Pryor, Barack Obama, Rupert Murdoch, Robert Mueller, Declan McCaullagh, Thomas Lenard, Vito Lapinta, Mark Klein, John Kerry, Hank Johnson, Bill Hemmer, Hugh Grant, William Glanz, AL Franken, Daniel Ellsberg, Thomas Drake, Sally Dowler, Milly Dowler, Bob Dowler, Alan Davidson, George W. Bush, Joe Barton, James Barmford, Julian Assange, Keith Alexander, Peter Aldridge, Mark Zuckerberg, Jamie Court, Ondi TImoner, Raymond Kurzweil, Frank Heidt, Chris Anderson, Peter Schaar, Orson Scott Card, Chris Knight, Amy Cutler, Joe Lipari, Leigh Bryan, Douglas Rushkoff, Christopher Shin, Jerome Schwartz, Brain Kennish, Max Schrems, Margaret Atwood, Barrett Brown, Ellen Corbett, Ryan Calo, Michael Schearer, Christopher Soghoian, Rainey Reitman, Sherry Turkle, Moby, Danah Boyd, Debra Aho Williamson, Eli Pariser, Siva Vaidhyanathan, Eric Schmidt, Zeynep Tufekci, Harvey Anderson, John Palfrey and Brian Lawler.
The main subject of Terms and Conditions May Apply is privacy and the role of online services in the erosion of digital privacy on the internet. This cybersecurity documentary also exposes the legal covers that corporations and governments worldwide utilize to collect data on citizens every day.
The Terms and Conditions May Apply documentary is closely related to cybersecurity concepts such as data security and privacy. The primary portion of the documentary tackles cybersecurity issues like the use and sale of sensitive data by the world’s most successful technology companies, such as Facebook and Google.
10. Hacking Democracy (2006)
Hacking Democracy is an online cybersecurity documentary that sheds light on the corporations involved in voting machines and the counting of votes.
The release date of Hacking Democracy is Nov. 2, 2006, with Simon Ardizzone and Russell Michaels serving as directors. People credited as producers of Hacking Democracy include Robert Carrilo Cohen, Russell Michaels and Simon Ardizzone. Executive producers include Sian Edwards Beal, Alice Henty, John Hoffman, Earl Katz, Sheila Nevins, Sarah Teale and Piers Vellacott.
The main cast of hacking Democracy includes names such as Andy Stephenson, Ion Sancho, Mark Radke, Harri Hursti, Deanie Lowe, Bev Harris and James Naughton.
The primary subject of this cybersecurity documentary is investigative journalist Bev Harris and a small group of citizen activists. Hacking Democracy chronicles the group’s journey in trying to uncover the procedure behind counting votes in the U.S. The group also sets out to prove that stealing votes is not beyond the realm of possibility given the presence of skilled hackers and profit-seeking corporations in control of voting machines.
Hacking Democracy is all about cybersecurity since the movie discusses how hackers and corporations can disable security mechanisms to keep voting data safe and secure from manipulation. The documentary also follows Harri Hursti, a hacker who showed how to perform an untraceable hack on the voting system in Leon County, Florida, using a single memory card. Such events are potentially useful for cybersecurity professionals looking for easily digestible material.
11. Citizenfour (2014)
Citizenfour is a historical and biographical cybersecurity documentary that details a reporter’s meetings with famed National Security Agency whistleblower Edward Snowden.
The release date for Citizenfour is Nov. 28, 2014, with Laura Poitras credited as the director and producer of the documentary. In addition to Poitras, Dirk Wilutzky and Mathilde Bonnefoy are also credited as producers. Citizenfour’s cast members include Snowden, Poitras, Piers Morgan, Jesselyn Radack, Barack Obama, James Clapper, Keith Alexander, Lindsay Mills, Rainer Staudhammer, Marcel Rosenbach, Lada Levison, David Miranda, Carsten Gericke, Gonzalo Boye, William Bourdon, Ben Wizner, Wolfgang Kaleck, Marcel Bosonnet, Julian Assange, Nick Hopkins, Paul Johnson, Julian Borger, Roberto Kaz, Jose Casado, Robert Tibbo, Jonathan Man, Michael Day Hawkins, H. Thomas Byron, Harry Pregerson, Kevin Bankston, M. Margaret McKeown, Jeremy Scahill, Ewen MacAskill, Jaco Appelbaum, William Binney and Glenn Greenwald.
Citizenfour touches on themes such as mass surveillance, corruption in government, government surveillance, the U.S. National Security Agency (NSA), information leaks, investigative journalism, invasion of privacy, whistleblowing, government cover-ups and terrorism.
The main subject of Citizenfour is Snowden’s story about how working as an intelligence consultant for the NSA, Snowden sent encrypted email messages to trustworthy journalists and activists providing evidence of illegal activities.
Note:
Citizenfour, as a documentary, contains cybersecurity-related components such as the mechanisms Snowden used to extract the NSA’s sensitive data, the functions and technical aspects of surveillance programs, and the overall state of national security in the U.S. and globally.12. DEFCON: The Documentary (2013)
The DEFCON: The Documentary is a cybersecurity documentary that takes a look at DEFCON, the biggest hacking conference in the world, for a period of four days.
DEFCON: The Documentary was released in the U.S. on Aug. 1, 2013. Jason Scott Sadofsky worked as the documentary’s director, while Rachel Lovinger, Jeff Moss and Russ Rogers are credited as producers and executive producers.
The cast of the DEFCON: The Documentary includes Carlos De Leon, Neil R. Wyler, Tim Vidas, Deth Veggie, Jonathan Vanover, Peter Teoh, Scotland Symons, Stealth, Mike Spicer, Mark Smith, Siviak, Winn Schwartau, Guido Sanchez, Ryan Russell, Russ Rogers, Marc Rogers, Roamer, Philip Polstra, Percent, Peeve, Michale Pauley, Noid, Jeff Moss, Eddie Mize, Luke McOmie, Brain Martin, Nikita Kronenberg, Dan Kaminsky, Uncle Ira, Brad Haines, Gtrf, Grandmaster Ratte, Joe Grand, Wayde Gilliam, Connor Gilliam, Fredyd Frick, Grey Frequency, Zac Franken, Nicholas Frangia, Flea, Ryan Finnie, Dr. Faustus, Chris Darbro, Ryan Clarke, Brain Baskin and Dead Addict.
The main subject is the DEFCON event, as the documentary crew essentially records the full event. DEFCON has a strict no-video policy, but the crew was allowed to film the event for four days. The whole documentary is thus about the people at DEFCON, featuring interviews with many individuals involved with the conference, the different sub-events that take place at DEFCON and the history of DEFCON.
DEFCON: The Documentary is perhaps the most relevant documentary for any professional working in the cybersecurity field. That’s because the whole event (and the documentary) is about disseminating the latest developments in the field of security and privacy. Cybersecurity professionals usually have to attend a DEFCON or two to network and learn more about the trends in the industry. A documentary detailing the event and the philosophy behind the conference can help any cybersecurity professional gain some vital information before attending one in person.
13. Snowden (2016)
Snowden is less of a documentary and more of a biographical criminal drama movie. The movie was released in the U.S. on Sept. 16, 2016. Snowden was produced by Fernand Sullchin, Philip Schulz-Deyle, Eric Kopeloff and Moritz Borman, and Oliver Stone directed the film.
Cast members of Snowden (2016) include Edward Snowden, Alan Rusbridger, Ashani Perera, Mathangi Ray, Ben Chaplin, Stanley I. Walker Jr., Eric Kofi Abrefa, Logan Marshall-Green, Stephanie Simbeck, Lakeith Stanfield, Scott Eastwood, Christy Meyer, Patrick Joseph Byrnes, Olga Koda, Bhasker Patel, Valentina Kuitko, Anatoly Kucherena, Suzanne Gilbert, Erol Sander, Ben Schnetzer, Timothy Olyphant, Demetri Goritsas, Nicholas Rowe, Joely Richardson, Tom Wilkinson, Shailene Woodley, Michael Benz, Nicolas Cage, Ken Thomas, Rhys Ifans, Parker Sawyers, Christian Contreras, Rachel Handshaw, Robert Firth, Jaymes Butler, Joseph Gordon Levitt, Zachary Quinto and Melissa Leo.
Just like any good cybersecurity-related film, Snowden (2016) deals with themes such as mass surveillance, digital journalism, whistleblowing, cryptography, WikiLeaks, the NSA and ideas surrounding the Orwellian state.
The main subject of Snowden (2016) is the NSA contractor Edward Snowden and how the agency’s malpractices led him to steal classified information and then leak the reports to trusted journalists from around the world.
The Snowden documentary has many connections with the issues facing the cybersecurity industry today—mainly, how organizations can keep data safe from potential whistleblowers. From the point of view of whistleblowers, this cybersecurity documentary is relevant as knowing how to extract data from company servers and then disseminate information contained in the data reliably and anonymously to credible contacts is something any cybersecurity professional would be interested in.
14. The Defenders (2018)
The Defenders is a lesser-known cybersecurity documentary that takes a behind-the-scenes look at various cybersecurity professionals working in the field for critical institutions. This cybersecurity documentary also covers various famous cyberattacks over the past several years.
The Defenders was released on May 7, 2018. This documentary/film was produced by Cybereason and directed by Luke Poling and Matthew Slutsky.
As far as the main subject of this cybersecurity documentary goes, The Defenders focuses on cybersecurity professionals rather than hackers. The entirety of the documentary records the work of cybersecurity professionals and how the discipline is learned and put into practice.
The Defenders is perhaps the only feature-length documentary that deals with cybersecurity from the perspective of cybersecurity professionals rather than hackers. Hence, the documentary is closely related to cybersecurity, with a particular focus on cyberattacks and how countermeasures work to protect important infrastructure from the ever-evolving threat of hackers.
15. Zero Days (2016)
Zero Days is a PG-13 cybersecurity documentary that focuses on Stuxnet and how the malware destroyed key components of nuclear facilities in Iran.
The Zero Days documentary was released in the U.S. on July 8, 2016. Marc Shmuger and Alex Gibney are credited as the producers of Zero Days, with Gibney also receiving credit as the writer. In addition to Shmuger and Gibney, Daine Weyermann, Jeff Skoll, Tess Ranahan, Richard Perello, Stacey Offman, Allyson Luchak, Ophelia Harutyunyan, Sol Dooman, Alex Gibney, Blair Foster, Grace Fradella, Sarah Dowland, Heather Courtney, Javier Alberto Botero and Jennie Amias worked on Zero Days as producers.
Cast members of Zero Days include Andy Grieve, Julian Seltzer, Camilo Quiroz Vazquez, Tadashi Mitsui, Joanne Tucker, Sean McGurk, Chris Inglis, Gary D Brown, Yuval Steinitz, Amos Yadlin, Yossi Melman, Michael Hayden, Richard Clarke, Emad Kiyaei, Olli Heinonen, Rolf Mowatt Larssen, Gary Samore, David Sanger, Liam O Murchu, Ralph Langner, Vitaly Kamluk, Eugene Kaspersky, Eric Chien and Sergey Ulasen.
Zero Days’ main subject is Stuxnet and how intelligence agencies in Israel and the U.S. worked together to develop Stuxnet and deploy the computer malware to destroy nuclear enrichment centrifuges in Iran.
This documentary has major connections with ideas and concepts found in cybersecurity, such as the development of malware from supposed law enforcement agencies, deployment of malware, nation-level cyber warfare and data collection.
The subject matter of Zero Days may not directly relate to professional work found in the cybersecurity industry. However, any cybersecurity professional can benefit from the content offered in the documentary for a broader look at how cybersecurity principles can be leveraged to generate real-world consequences.
What are the Themes of Cybersecurity Documentaries?
Most cybersecurity documentaries tackle the same themes related to cybersecurity, cybercrime, cyberwarfare, mass surveillance, the surveillance state, data privacy and privacy invasion.
“Cybercrime” is a term used to refer to any criminal activity that affects a network, mobile device or computer. Generally, any device that is part of a network (either local or via the internet) is vulnerable to cybercrimes. Both organizations and individuals can and do take part in cybercrime. Contrary to popular belief, cybercrimes are not always committed for money but also for political power and cultural superiority.
The term “cybersecurity” refers to all the practices that security professionals and organizations implement in order to stop cybercrimes. More specifically, cybersecurity refers to all the mechanisms and tools that organizations and individuals use to protect sensitive information and critical computer systems from cyberattacks. All of the cybersecurity measures are meant to stop cyber threats from damaging applications and/or network systems.
Cyber warfare is another common theme in various cybersecurity documentaries. The term “cyber warfare” refers to all the actions that an organization or a nation-state takes to attack and damage a given target’s computing devices and networks. The target can be anything from nations to individual organizations. Most cyber warfare comes down to two parties developing computer viruses and launching DDoS attacks against each other’s critical infrastructure.
Another common theme in most cybersecurity documentaries is “mass surveillance,” a term referring to the practice of keeping tabs on citizens and civilians. Numerous activities can form part of a larger mass surveillance strategy, such as email interception, CCTV camera monitoring, hacking, infecting devices with spyware, wiretapping and recording targets’ GPS locations.

The next very relevant term is “surveillance state,” which generally means the government is deploying technological solutions and infrastructure to collect data on citizens under the garb of national security. In the modern world, a surveillance state takes advantage of technologies such as the internet and mobile devices to expand spying programs on citizens. Surveillance states also have heavily-funded intelligence agencies with legally-sanctioned extraordinary power to collect data not just via government channels and the agency’s own but also from private organizations.
Data privacy is another common theme that is discussed in various cybersecurity documentaries time and time again. The term “data privacy” means the protection of sensitive data from all actors that don’t have a legitimate reason to access that data. Data privacy grants end-users the right to control how personal/sensitive data is shared.
The final theme that appears regularly in various cybersecurity documentaries is the invasion of privacy. The term “privacy invasion” refers to the behavior of various online services and apps that track users over the internet even when the user has closed the app or the service. Such services/apps record anything the user clicks on, the pages the user visits and other websites that the user visits at other times. Since these services/apps do not ask the user for permission before tracking, privacy advocates consider such behavior an invasion of privacy.
Can You Get Motivated after Watching a Cybersecurity Documentary?
Yes, people interested in cybersecurity can get motivated after watching a cybersecurity documentary. Cybersecurity documentaries are an attractive and practical way to get introduced to cybersecurity and can provide inspiration to someone looking for opportunities in the cybersecurity sector.On that point, jobs in the cybersecurity sector can look a bit dull. Cybersecurity documentaries can mix the factual information of the subject at hand with good direction and make the whole experience look more interesting.
Considering the increasing amount of cyber security job opportunities worldwide, cybersecurity documentaries can enable someone interested in this field to have a cursory look at all the diverse positions available. The primary purpose of any cyber security job would be to protect a given organization or an individual computer system from cyberattacks. Cyber security jobs also require the applicant to have the necessary skills to keep networks safe and information secured.
There is even more variety in the type of roles one can play in a given cybersecurity organization. For example, some security experts only deal with detecting vulnerabilities in a given computer system, while others develop software that helps protect vulnerable systems. Then, some professionals mostly handle the hardware side of security; others specialize in the specific procedures necessary to implement to keep attackers at bay.
Less technical roles in cybersecurity involve the cybersecurity professional developing strategies to mitigate risks from various cyber threats and develop company-wide policies to maintain data security and anonymity.

That’s not even the end of different cybersecurity roles. More and more businesses are moving to the digital world for a variety of reasons. For a person interested in cybersecurity, that only means more job opportunities in even more diverse industries. The most lucrative cyber security jobs are in insurance and hospitality.
The wide range of job titles in the field showcases the sheer diversity of cyber security job opportunities. An interested person in cybersecurity can become a security engineer, security architect, chief information security officer or information security analyst.
Is It Easy to Understand a Cybersecurity Documentary?
Yes, users will find watching and understanding cybersecurity documentaries easy. That’s because cybersecurity documentaries are not too technical in nature. The main purpose of any cybersecurity documentary is to make people aware of the activities of different malicious actors on the internet and how such activities can affect lives in the real world. Hence, producers and directors ensure that the material presented is not so dense that people get discouraged to continue watching cybersecurity documentaries.
With that said, there is only so much that writers, directors and producers can do to make cybersecurity documentaries understandable for the mass audience.

Some general concepts about how companies collect and use consumers’ data may be helpful. People interested in cybersecurity documentaries may also take short non-technical courses available on sites like Coursera and Simplilearn to know more about the world of hacking and cyber warfare. Readers can also run a quick search engine query on the basics of cybersecurity and what an average online user needs to know. Going through a few guides should be enough to get the best out of any cybersecurity documentary.
What is the Required Knowledge to Understand a Cybersecurity Documentary?
There is no special required knowledge to understand a cybersecurity documentary. However, knowing a few basic cybersecurity concepts can always help absorb the presented content better. Some of these terms include attack surface, antivirus, Tor, SQL injection, SOC, ransomware attacks, phishing, NIST, malware, IPS, honeypot, firewall, EDR, cryptoworm and data breaches.
To learn about the terms mentioned so far, readers can refer to courses on FutureLearn, Simplilearn, Coursera and of course, YouTube. Open up a browser, go to YouTube and then input one of the terms mentioned above as the search query. YouTube is likely to return hundreds if not thousands of explainer videos for free. After watching two or three explainer videos, an individual can gather enough knowledge to understand the term’s application in any cybersecurity documentary.

There aren’t many conditions and requirements involved with learning cybersecurity terms to make watching cybersecurity documentaries easier. Readers just need to make sure the platform regularly reviews the information available and adds newer, more relevant terms periodically.
Again, YouTube is the perfect platform to get the latest information on any cybersecurity-related term or concept for free. But since YouTube is not the most trustworthy place to learn about technical subjects, readers may get more out of paid platforms like Coursera and FutureLearn.
Can You Learn Cyber Security Terms from Documentaries?
Yes, readers interested in the subject can learn cyber security terms from documentaries. Of course, different documentaries would focus on different cybersecurity concepts and terms, and hence there is no single cybersecurity documentary that can properly cover all the relevant cybersecurity terms.
An example of an important cyber security term that pops up in many cybersecurity documentaries is “brute-force attack.” Hackers and other cybercriminals use brute-force attacks to guess a username and password combination by trying out all possible outcomes on a trial and error basis. Brute-force attacks are some of the simplest and oldest cyberattacks in existence.

One of the documentaries mentioned above, Zero Days, covers the term “Stuxnet” in depth. Watching this cybersecurity documentary can help readers learn more about Stuxnet. In short, though, Stuxnet is a computer worm that intelligence agencies in the U.S. and Israel wrote and deployed. Stuxnet specifically compromises PCIS devices and makes the infected system unstable enough to malfunction completely.
That leads to another important cybersecurity term: “zero-day attack.” The term zero-day attack means a cyberattack that uses a very recent security vulnerability found in a computer or network system. Zero-day attacks are usually more effective than many other types of cyberattacks because developers, manufacturers and vendors haven’t had enough time to learn the security vulnerability the attack is exploiting. Thus, a security patch is delayed.
For those looking to advance a cybersecurity career by watching cybersecurity documentaries, some cyber security terms to learn more about include risk assessment, collaboration (in the context of cybersecurity), penetration testing, digital forensics, Splunk, Kerberos, Linux Server Administration and post-hack work.

