Most of the movies related to cyber security are based on true stories. If not entirely, they could have some elements of truth in them. Movie enthusiasts are drawn towards such movies or programs because they are thrilling and educational. Not only will they give them insights into how the hacking world operates, but viewers also see how crippling a cyber-attack can be to individuals and businesses. A complete list of cyber security movies to check out in local movie listings is listed below.

- The Matrix (1999)
- Bourne Ultimatum (2007)
- V for Vendetta (2005)
- Ex Machina (2014)
- The Imitation Game (2014)
- The Italian Job (2003)
- The Girl with the Dragon Tattoo (2011)
- WarGames: The Dead Code (1983)
- Lo and Behold: Reveries of the Connected World (2016)
- Swordfish (2001)
- Reboot (2012)
- Catch Me if You Can (2002)
- Who Am I (1998)
Table of Contents
1. The Matrix (1999)
Definition: Released in 1999, the Matrix is a science fiction action film, meaning the movie uses fictional-based science phenomena that people rarely see in real life. Such phenomena include extraterrestrial lifeforms, interstellar travels, spacecraft, and robots. This movie was the first in the Matrix film series.
Release date: The Matrix was released on 24th March 1999 at the Mann Village Theater in Los Angeles, California.
Producer: This movie was produced by executive producers Lana Wachowski, Lilly Wachowski, Bruce Berman, Andrew Mason, Barrie M. Osborne, and Erwin Stoff. Dan Cracchiolo was the co-producer, while Carol Hughes and Richard Mirisch were associate producers. Joel Silver was also a producer on the Matrix.
Director: This movie was written and directed by the Wachowski siblings, Lana and Lilly. The two are American citizens who write, produce, and direct film and television shows. Both identify as Trans women.
Cast: The Matrix starred Keanu Reeves, Lawrence Fishburne, Hugo Weaving, Carrie-Anne Moss, Joe Pantoliano, Marcus Chong, Anthony Ray Parker, Julian Arahanga, Matt Doran, Gloria Foster, Belinda McClory, Paul Goddard, Robert Taylor, and Ada Nicodemou.

Theme: This movie follows a science fiction action film house style. The movie has since inspired various literary and cinematic works. Like many cyber security movies in Hindi, The Matrix also borrowed concepts from religion, philosophy, and mythology. Christianity, Buddhism, Judaism, and Hinduism were among the religious inspirations for this movie.
Subject: The movie centers on the human population being trapped unknowingly in the Matrix, a simulated reality. Intelligent machines have created this situation to distract humans and use their bodies as energy sources. Thomas Anderson, alias Neo, discovers this secret and starts a rebellion among people against the intelligent machines. He rebels with the help of other Matrix escapees.
Links to cyber-security: The movie is related to cyber security for two reasons.
- The code takes over the humans in similar events to when a hacker uses a person’s credentials to log into a system and steal their information.
- When one of the team members betrays them for a chance to get back into the Matrix, it depicts how a company employee can facilitate hacking. An employee or contractor may give cybercriminals access to the company’s exclusive data, hence posing the risk of hacking.
2. Bourne Ultimatum (2007)
Definition: The Bourne Ultimatum is one of the most popular movies about cyber security. The movie was loosely based on a 1990 novel of the same name, written by Robert Ludium. It was the third sequel to the Jason Bourne film series, starting with The Bourne Identity (2002) and Bourne Supremacy, released in 2004.
Release date: The movie was released on 25th July 2007 in ArchLight Hollywood.
Producer: Bourne Ultimatum was produced by Frank Marshall, Paul L. Sandberg, and Patrick Crowley under an American production and distribution company, Universal Pictures.
Director: The Bourne Ultimatum was directed by Paul Greengrass.
Cast: Matt Damon, Julia Stiles, David Strathairn, Joan Allen, Scott Glenn, Edgar Ramirez, Paddy Considine, Daniel Brühl, and Albert Finney. Other cast members include Colin Stinton, Tom Gallop, Lucy Liemann, Joey Ansah, and Franka Potente.

Theme: The Bourne Ultimatum is an action-thriller film.
Subject: The Bourne Ultimatum is a movie whose character pays homage to the novel’s signature character, Jason Bourne. Bourne is a former CIA assassin who is on a quest to find information about his past before becoming part of an assassin program named Operation Treadstone. The Treadstone is a behavior modification program. He also becomes the target of a similar assassin program.
Links to cyber-security: The film is a useful resource where viewers can learn the importance of geosurveillance for national security post-9/11. The movie shows high-surveillance technologies that are used to counter global terrorism.
3. V for Vendetta (2005)
Definition: V for Vendetta is one of the best cyber security movies at the box office. It features a 132-minutes running time, and English is the main language in the film. The budget for this movie ranged between 50-54 million dollars. Cinematographer Adrian Biddle shot the movie in London, Potsdam, and Berlin.
Release date: V for Vendetta was first released on 11th December 2005 during the Butt-Numb-A- Thon film festival.
Producer: Joel Silver, the Wachowskis, and Grant Hill.
Director: James McTeigue.
Cast: Natalie Portman, Hugo Weaving, Stephen Rea, Stephen Fry, John Hurt, Tim Pigott-Smith, Rupert Graves, Roger Allam, Ben Miles, Sinéad Cusack, Natasha Wightman, Imogen Poots, John Standing, Eddie Marsan, Clive Ashborn, and Guy Henry.

Theme: The movie is a dystopian political action film. V for Vendetta portrays an individual’s struggle between freedom and the state. The imagery in this film is inspired by real and fictional totalitarian icons, including Adolf Hitler.
Subject: The film depicts an era where anarchy reigns. Pandemics, global wars, terrorism, and riots leave the world in turbulence. The government imprisons and executes homosexuals, Muslims, atheists, political opponents, Jews, and immigrants. The main character, “V”, starts a rebellion against the government. He urges the people to meet him on the following year’s Guy Fawkes Night outside parliament houses.
Links to cyber-security: The main character is portrayed as an idea rather than an individual. This is because his identity, face, and past are hidden through the symbolic use of a Guy Fawkes mask to conceal his scars. The hidden identity symbolizes how hackers are normally depicted in images related to cyber security. Their faces are often masked to show how they remain anonymous while carrying out cyber-attacks.
4. Ex Machina (2014)
Definition: Ex Machina is one of the best cybersecurity movies on this list, emphasized by the fact the National Board of Review recognized this movie as one of the 10 best independent films of the year in 2014. It received largely positive reviews for its extraordinary editing, visual effects, and screenplay. For a budget of $15 million, the production companies involved in this movie included DNA Films and Film4. It grossed about $36 million at the worldwide box office.
Release date: The movie was first released on 16th December 2014 at the BFI Southbank Cinema in Britain.
Producer: Andrew Macdonald and Allon Reich.
Director: Alex Garland.
Cast: Domhnall Gleeson, Oscar Isaac, Alicia Vikander, Sonoya Mizuno, Gana Bayarsaikhan, Corey Johnson, Claire Selby, Symara Templeman, Tiffany Pissani, and Lina Alminas.

Theme: Ex Machina follows a science action theme, and it includes real characters and android robots.
Subject: The movie follows the narrative of a programmer invited to the home of the CEO of the company he works for. The CEO asks him to test the intelligence of the robots through a Turing Test. Tables turn when the robot convinces the programmer to help her escape from the home. In the end, the robot outwits the programmer and leaves him behind, arriving in an unknown city and blending into the crowd.
Links to cyber-security: This movie portrays how artificial intelligence can threaten the human population if not handled carefully. It shows the vulnerability of robots to cyber-attacks because a person can manipulate their systems to achieve whatever they want. In turn, the machines can also use their intelligence to overturn the human population because they are devoid of emotions.
5. The Imitation Game (2014)
Definition: The imitation Game is one of the most popular cyber security movies on Netflix. Written by Graham Moore, the movie was shot with a budget of $14 million and grossed about $233 million worldwide. The insane profits from this film made it the highest-earning independent movie of 2014.
Release date: The movie was first released on 29th August 2014 at the Telluride Film Festival in Colorado.
Producer: Nora Grossman, Ido Ostrowsky, and Teddy Schwarzman.
Director: Morten Tyldum.
Cast: Benedict Cumberbatch, Keira Knightly, Mathew Goode, Rory Kinnear, Allen Leech, Mathew Beard, Charles Dance, Mark Strong, James Northcote, Tom Goodman-Hill, Steven Waddington, Ilan Goodman, Jack Tarlton, Alex Lawther, Jack Bannon, Tuppence Middleton, James G. Nunn, and Victoria Wicks.

Theme: The theme of this movie is based on an American historical drama.
Subject: The Imitation Game is a movie that follows the events in the life of Allan Turing, a mathematician. A young Allan develops an interest in cryptography courtesy of his friend in boarding school, whom he develops romantic feelings for soon after. He later joins a cryptography team and consequently develops his machine to decode messages from the Enigma machine sent between Nazis for the British government. The government later convicts him of gross indecency due to his sexuality and forces him to undergo a chemical castration procedure. His physical and mental health deteriorates, leading him to commit suicide.
Links to cyber-security: Allan Turing, whose life is loosely portrayed in this film, was a mathematician who created a mechanical computing device. The device was massively superior to human capabilities, its function being computing a large number of mathematical calculations. The Turing machine set the pace for the development of computers, smartphones, and the Internet. All these are the main vessels in cyber-security threats and attacks.
6. The Italian Job (2003)
Definition: The Italian Job is an American remake of a 1969 British film of the same name. However, the plot and characters of this film differed from the original film. Most of the movie was shot by cinematographer Wally Pfister in Venice and Los Angeles. From a budget of $60 million, The Italian Job raked in $176.1 million worldwide.

Release date: 11th May 2003 at the Tribeca Film Festival in New York City.
Producer: Donald De Line.
Director: F, Gary Gray.
Cast: Mark Wahlberg, Charlize Theron, Edward Norton, Donald Sutherland, Jason Statham, Seth Green, Mos Def, Franky G, Boris Lee Krutonog, and Aleksander Krupa.

Theme: The Italian Job follows an action thriller film theme.
Subject: The Italian Job is also among famous cybersecurity-related movies. With a running time of 110 minutes, the plot follows a varied crew of thieves. The thieves hatch a plan to steal gold from a former associate who betrayed them. Through a series of events and with the help of technology, the team successfully obtains the gold and divides it amongst themselves. The epilog shows that the gang has used their share of the gold to achieve their desired purposes.
Links to cyber-security: This movie opens up a world of possibilities where hackers can access and control security systems. This aspect is shown when the robbers perform a successful gold heist and get away by hacking into the city’s traffic light system. This cyber-attack results in a heavy traffic jam, easing their escape through the snarl-up.
7. The Girl with the Dragon Tattoo (2011)
Definition: The Girl with the Dragon Tattoo is another movie about cyber security. With a running time of 158 minutes, the movie was produced under a budget of $90 million. It was distributed by Sony Pictures Entertainment Motion Picture Group and raked in $239.3 at the box office.
Release date: 12th December 2011 at the Odeon Luxe, Leicester Square in London.
Producer: Scott Rudin, Ole Søndberg, Søren Stӕrmose, and Ceán Chaffin.
Director: David Fincher.
Cast: Daniel Craig, Rooney Mara, Christopher Plummer, Stellan Skarsgård, Steven Berkoff, Robin Wright, Yorick van Wageningen, Roely Richardson, Goran Višnijić, Donald Sumpter, Ulf Friberg, Geraldine James, Embeth Davidtz, Josefin Asplund, Per Myrberb, Tony Way, Fredrick Dolk, Alan Dale, Leo Bill, Élodie Yung, and Joel Kinnaman.

Theme: This movie follows a neo-noir psychological thriller theme.
Subject: The Girl with the Dragon Tattoo tells the story of an investigation into the disappearance of a girl from a wealthy family 40 years prior. One disgraced journalist, Michael Blomkvist, enlists the help of a brilliant computer hacker named Lisbeth Salander to solve the mystery. The duo uncovers that the missing girl has been alive all this while, and she had assumed the identity of her late cousin. Her father had abused her, and she later killed him while defending herself. Her brother also abused her, forcing her to run away. The girl’s grandfather offers Blomkvist evidence against businessman Hans-Erik Wennerstrom who filed a libel suit against him and disgraced his career. In exchange, the journalist should investigate the presumed murder of the girl who disappeared when she was 16.
Links to cyber-security: Lisbeth Salander is portrayed in this movie as a talented hacker who can access information from her laptop. She can retrieve the contents of whatever computer she wants and, in some cases, have full control of it. By hacking, she satisfies her curiosity when she accesses emails, bank statements, work documents, and browsing histories on computers. This movie shows how much information a hacker can access on any computer and steal valuable information.
8. WarGames: The Dead Code (1983)
Definition: WarGames: The dead Code is also on this list of revolutionary movies on cyber security. The film features a running time of 114 minutes in English. With a budget of $12 million, the production companies involved in this movie were Sherwood Productions and United Artists. The film grossed an impressive $124.6 million worldwide.
Release date: 7th May 1983 at the Cannes Film Festival.
Producers: Leonard Goldberg, Richard Hashimoto, Harold Schneider, and Bruce McNall.
Director: John Badham and Martin Brest.
Cast: Mathew Broderick, Dabney Coleman, John Wood, Ally Sheedy, Barry Corbin, Juanin Clay, Dennis Lipscomb, Joe Dorsey, Michael Ensign, William Bogert, Susan Davis, Irving Metzman, John Spencer, Michael Madsen, Alan Blumenfeld, Maury Chaykin, Eddie Deezen, art LaFleur, Stark Pierce, Stephen Lee, Jesse Goins, James Ackerman, and James Tolkan.

Theme: This movie is a cold war science fiction techno-thriller film.
Subject: The movie depicts a young hacker named David Lightman (played by Mathew Broderick) who unknowingly accesses a United States military supercomputer. The computer is programmed to fuel, predict, and effect nuclear confrontation against the Soviet Union. He unknowingly plays a game that stimulates the machine to depict that the Soviet Union has attacked American cities. Following a string of events that threaten to start world war III, David is arrested and later escapes to find the creator of the computer. Together, they stop the computer from playing the game and triggering war, suggesting a friendly chess game instead.
Links to cyber-security: This science fiction film was one of the influences in creating a U.S Computer Fraud and Abuse Act, among other security policies. The Act involved anti-hacking law with felony consequences to deter invasions into NORAD (North American Aerospace Defense Command).
9. Lo and Behold: Reveries of the Connected World (2016)
Definition: With a running time of 98 minutes, Lo and Behold: Reveries of the Connected World shows real people and institutions through interviews that depict how the internet and artificial intelligence has impacted them. The film generated mainly positive reviews from movie critics.
Release date: 23rd January at the Sundance Film Festival.
Producers: Werner Herzog and Rupert Maconick.
Director: Werner Herzog.
Cast: This film features interviews with leaders in the technology space. They include Elon Musk, Joydeep Biswas, Shawn Carpenter, Hilarie Cash, Sam Curry, Danny Hills, Robert Kahn, Marcel Just, Leonard Kleinrock, and Lawrence M. Krauss. Other interviewees include the family of Nicole Catsouras, Felix Jay Lockman, Tom M. Mitchell, Theodore Holm Nelson, Sebastian Thrun, and Kevin Mitnick.

Theme: The movie is an American documentary film.
Subject: This movie contains interviews of people to portray the impact of the Internet and artificial intelligence on humans. Werner Herzog narrates over the footage of the University of California, terming it as “the birthplace of the internet.” He then shows the first piece of internet gear ever to be connected. The rest of the film explores the benefits and the downside of the Internet, including an interview with the family of Nicole Catsouras. They describe how internet trolls continually harassed the family online after the death of Nicole, deepening their grief.
The film also explores an institution that doesn’t allow electronic devices within a 3-mile radius and interviews people affected by electromagnetism sensitivity. Elon Musk is also part of this film, describing his quest to send humans to Mars. Finally, the movie touches upon the possibility of artificial intelligence taking over human interactions in the future.
Links to cyber-security: One standout interview involves Kevin Mitnick, an ex-convict, and a master hacker. He describes how easy it is to perform a cyber-attack by exploiting humans. Mitnick describes in great detail how one can steal confidential information by manipulating the human element in cyber-security systems.
10. Swordfish (2001)
Definition: This film perfectly fits the algorithm of hacker cyber security movies. It features a running time of 99 minutes in English. Distributed by Warner Bros. Pictures, the movie raked in $147.1 million worldwide. The budget for making this film was $102 million, with the cinematography done by Paul Cameron. The music featured in this film was done by Christopher Young and Paul Oakenfold, while Stephen E. Rivkin completed the editing.
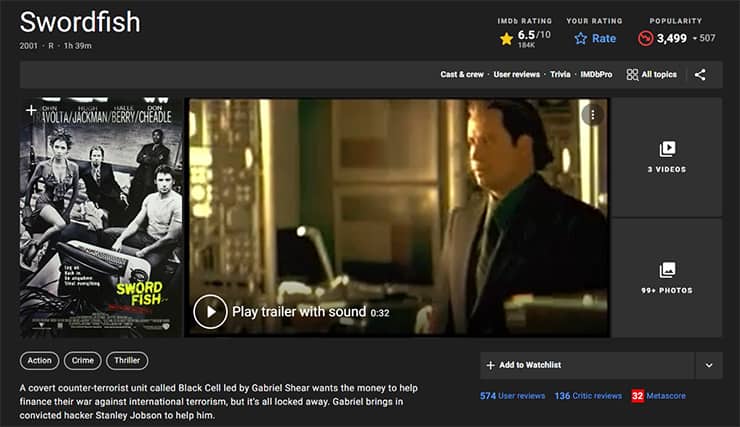
Release date: 8th June 2001.
Producers: Joel Silver and Jonathan D. Krane.
Director: Dominic Sena.
Cast: Hugh Jackman, John Travolta, Halle Berry, Don Cheadle, Sam Shepard, Vinnie Jones, Drea de Matteo, Rudolf Martin, Zach Greiner, Camryn Grimes, Angelo Pagan, Kirk B. R. Woller, Carmen Argenziano, Tim DeKay, and Laura Lane.

Theme: The theme of this movie is centered on an action thriller genre.
Subject: The film focuses on Stanley Jobson (played by Hugh Jackman). Stanley is a cyber-hacker and an ex-convict with formidable hacking skills. He became notorious for his daring infection of the FBI’s Carnivore program with a computer virus. His skills led him to be targeted for recruitment into a bank robbery conspiracy. Stanley is tricked into siphoning funds from the government’s slush funds.
He is also blackmailed into performing a bank heist to rescue his daughter, who was captured by the same people he was working for. In the end, Stanley realizes he has been tricked into re-siphoning the money from the backdoor of his computer worm into a bank. An FBI agent helps him secure the custody of his daughter and depart from the city.
Links to cyber-security: This film features a hacker forced to crack various cyber security systems and commit cybercrimes. He performs the attacks even when he is forbidden from touching any computer. Authorities put the ban in place because he had previously been convicted for a seriously damaging cyber-attack on the FBI.
11. Reboot (2012)
Definition: This short film brings home the reality that hackers are a big threat to the Internet and electronic media security. Reboot exposes the Internet’s sensitive side that could cause damage if the systems experience security leaks to malicious hackers.
Release date: 23rd July 2012 at Canada’s Fantasia International Film Festival.
Producers: Reboot had Arnold Serame as the executive producer, as well as Sidney Sherman as a producer. Also, there were two associate producers in the film, namely John Glaze and Heiko Heilemann-Bartsch.
Director: Joe Kawasaki.
Cast: Emily Somers, Travis Aaron Wade, Martin Copping, Sonalii Castillo, Janna Bossier, Troy Vincent, Charlie Weirauch, Traci Elizabeth, and Justin M. Via.

Theme: The movie follows a short science action theme.
Subject: A young woman, also a hacker, wakes up from a traumatic aftermath that she barely remembers. She has an iPhone glued to her hand, and there is a countdown ticking on the phone to zero. She must understand who she is and why she has become an extension of the phone before the time lapses. As the countdown continues, the young woman races against time to connect the pieces before the mysterious countdown hits the zero mark.
Links to cyber-security: This movie shows how deadly a cyber-attack can be, including making people anxious because of the fear of the unknown aftermath of such an attack.
12. Catch Me if You Can (2002)
Definition: Catch Me if You Can depicts a 141-minute clip with all the markings of a corporate cyber-security horror movie. It has horror-movie characteristics because the main character assumes different identities in different situations. Catch Me if You Can was inspired by the true story of Frank Abagnale, who sold the film rights to his autobiography in 1980. Producers Norman Lear and Bud Yorkin then sold the rights to other companies. DreamWorks Pictures eventually owned the rights after a series of reselling events between various production companies. The filming was set to begin in March 2001 with a budget of $52 million.
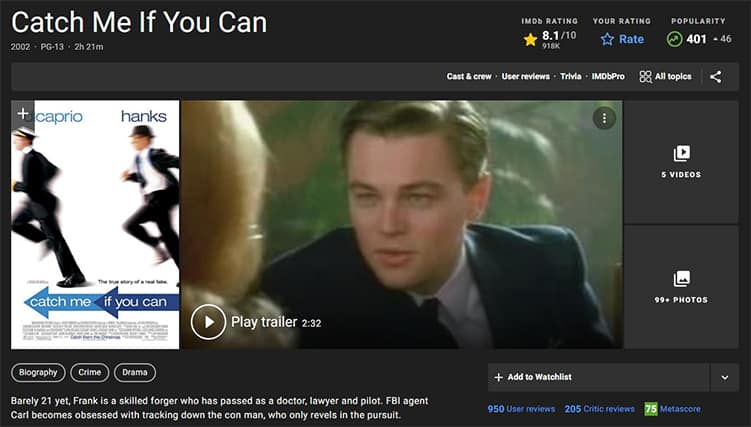
Release date: 28th December 2002 in Westwood, California.
Producers: Steven Spielberg and Walter F. Parkes.
Director: Steven Spielberg.
Cast: Leonardo DiCaprio, Tom Hanks, Christopher Walken, Martin Sheen, Nathalie Baye, Amy Adams, James Brolin, Nancy Lenehan, Candice Azzara, Malachi Throne, Alfred Dennis, Amy Acker, Guy Thauvette, Alfred Davis, Maggie Mellin, Thomas Kopache, James Morrison, Robert Symonds, Dave Hager, and Jasmine Jessica Anthony. Other cast members include Brian Howe, Frank John Hughes, Chris Ellis, John Finn. There were appearances from Jennifer Garner, Ellen Pompeo, Elizabeth Banks, Frank Abagnale, and Kaitlin Doubleday.
Theme: This film follows a biographical crime theme.
Subject: The film pays homage to Frank Abagnale, who is said to have conned people and amassed millions of dollars. The 19-year-old allegedly posed as a Georgia doctor, a Pan American World Airways pilot, and a Louisiana parish prosecutor. He is arrested and spends 12 years in a maximum-security prison. Later, the FBI allows him to serve the remainder of his sentence by working for the institution’s bank fraud unit. He eventually builds his legacy as one of the world’s top bank fraud and forgery experts.
Links to cyber-security: Catch Me if You Can shows how easy it is for hackers to identify vulnerable computer systems, attack, and exploit them. It also shows how hackers can keep changing identities to avoid being detected.
13. Who Am I (1998)
Definition: This 103-minute film is one of the cyber security-based movies shot before the 21st century. The film was scripted and shot in English, making it the second English film that Jackie Chan starred in. The movie was shot in South Africa, Namibia, and the Netherlands and raked in approximately $38.9 million at the Hong Kong Box office.
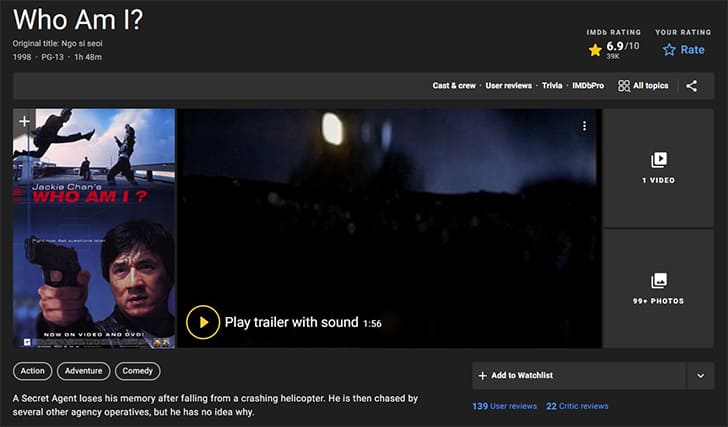
Release date: 17th January 1998.
Producers: Leonard Ho and Barbie Chung.
Directors: Jackie Chan and Benny Chan.
Cast: Jackie Chan, Michelle Ferre, Mirai Yamamoto, Ed Nelson, Ron Smerczak, David Vlok, Mike Ian Lambert, Ron Smoorenburg, Kwan Yung, Yanick Mbali, Washington Sixolo, Tom Pompert, Glory Simon, Chip Bray, and Frank Opperman.
The movie’s stunt team included Andy Cheng, Rocky Lai, Nicky Li, Chan Man Ching, Sam Wong, Kwan Yung, Bradley James Allan, and Paul Anderovski.

Theme: Who Am I is an action-comedy movie.
Subject: This movie follows the script of a Secret Agent who loses his recollection after falling from a crashing airplane. He finds himself in a South African jungle after failing his mission of kidnapping three scientists who were experimenting with a potent mineral. He goes on a mission to find his identity. In the process, he coincidentally discovers the location of the organization that kidnapped the scientists.
Links to cyber-security: The movie depicts a CIA undercover agent hiding under the guise of a journalist who cracks a secret code. The code is written on a matchbook, and it leads her and “Who am I” (Jackie Chan) to Rotterdam in the Netherlands, where they prevent the mineral from being sold to a powerful arms dealer. Cyber security involves various computer codes that hackers can crack to access information.
Who Should Watch Cyber Security Movies?
Cyber security movies are ideal viewing for people who are interested in cyber issues, especially how computers and artificial intelligence systems work. Such movies open their eyes to critical cyber issues, including the various avenues hackers can manipulate to access information systems. Therefore, they are better placed to understand how to avoid such situations. If interested, some individuals can also leverage this knowledge and seek further studies to become ethical hackers.
What Are the Benefits of Watching Cyber Security Movies?
Watching cyber security movies helps people understand how powerful the Internet is in building or destroying a system quickly. Cyber security is often oversimplified in mainstream movies though: it is much more complicated in reality. However, the movies spark curiosity in individuals and even spark an epiphany for computer system fanatics interested in venturing into the cyber security space.
What Are the General Themes of Cyber Security Movies?

Most of these movies follow a cyber-security theme and are executed in an action-thriller genre. The movies revolve around the main or supporting characters hacking into a computer system to obtain confidential information. Hackers in the film use their knowledge to commit a crime, solve a mystery or prevent a potential disaster from occurring.
Cyber Security movies also depict cyber-security crimes like phishing scams. This crime involves a hacker masquerading as a well-known brand or authoritative body and dupes unsuspecting individuals into revealing sensitive information like passwords and credit card details. Such scammers often hide under the guise of customer service agents to solve a particular problem, hence the need for the information.

Another cyber-security-related crime that the movies bring to light is DDoS attacks. Cybercriminals use these attacks to render an online service unavailable. They do this by overwhelming a website with heavy external traffic from various sources, causing the site to crash. The criminals also deposit malware on target computers by using Botnets, which are considerable networks of infected devices. Once they have successfully disabled a network, they exploit that opportunity to hack into the system.
Identity theft is also another cyber-crime often highlighted in movies. This crime involves a computer criminal hacking a system and accessing a computer user’s personal information. The hacker then uses this information to access confidential records, steal funds, or participate in insurance/tax fraud under the victim’s identity. The hackers can also claim government benefits or use the victim’s accounts to plan and execute criminal activities, leaving them in trouble with law authorities.
Where Can You Watch Cybersecurity Movies?
The best cyber security movie platforms that exist today include Disney Plus, Hulu, Apple TV+, Amazon Prime Video, and Netflix. Netflix is the best on this list because many devices support it, including smart TVs, game consoles, and streaming sticks. It also has amazing video quality where one can comfortably watch videos in 4K and HDR. Netflix also has a large catalog of movies, both old and new. Viewers can access a 2016 cyber security movie or older ones related to the same theme.
Can You Watch All Cybersecurity Movies on Netflix?

No, Netflix is a streaming platform that acquires streaming licenses by partnering with the content providers of the movies. Unfortunately, Netflix lacks the copyrights to stream all movies. The platform also constantly shuffles movies by adding new ones and taking out others. Netflix can pull down a movie if it has poor ratings or has expired copyright licenses.
Also, the platform streams content based on the country its subscribers are based in. Therefore, a Netflix subscriber in country A may be exposed to different content on the streaming platform than one in country B. Each of the 190 countries where Netflix is present has different catalogs of original and licensed films and TV shows, hence the content difference.
While users cannot change their country on the Netflix account, it is possible to bypass this by using a Virtual Private Network (VPN). With a VPN, users can set their location to anywhere on the VPNs location list. This is commonly used to access UK or US Netflix programs. This article explains how to change region on Netflix.
Who Are the Best Actors Played in Cyber Security Movies?
Some of the best actors on cyber security posters include Leonardo DiCaprio, Hugh Jackman, Halle Berry, Mark Ruffalo, Tom Hardy, and Joseph Gordon-Levitt. Other notable actors in cyber security films include:

- Elliot page
- Bruce Willis
- Marion Cotillard
- Emma Watson
- Shia LaBeouf
- Kevin Spacey
- Miley Cyrus
- Charlize Theron
- Matt Damon
Do Cyber Security Experts Act in Cyber Security Movies?

The documentary, Lo and Behold: Reveries of the Connected World (2016) shows real people breaking down the intricacies of the internet world. Cybersecurity experts that have acted in this documentary include Kevin Mitnick. Mitnick is revered as the world’s most famous hacker. Mitnick describes how easy it is to manipulate the human element and hack a system. Mitnick had been a cyber-criminal who committed various federal offenses related to computer hacking. He was arrested on 15th February 1995 and was incarcerated for five years. Since his release in 2000, he has been an author, a public speaker, and a paid security professional.
Another leader in the Cyber-security space that has made an appearance in a movie is Frank Abagnale Jr. Frank made an appearance on a Netflix cyber security movie named Catch Me if You Can. He claims to have committed various crimes when he was young by impersonating different professionals, earning millions of dollars while at it. He is now a renowned fraud prevention and cybersecurity expert.

