Cybersecurity experts are IT specialists responsible for supplying, monitoring, detecting, investigating, analyzing and responding to security events in software and networks. These professionals are accountable for detecting potential threats and constructing firewalls to protect a company’s network infrastructure.
Every business’s success depends on the security of the network and database. As a result, companies seek cybersecurity experts to manage and defend the company’s integrity by monitoring IT infrastructure. Because hackers are becoming more sophisticated in conducting business attacks, cybersecurity experts are critical members of any organization. No company can afford a data breach, which can bankrupt the company or ruin the company’s reputation. Companies must put in place all of the safeguards to secure automation with the help of a cybersecurity specialist. The cybersecurity field is rapidly expanding. Some of the skills and abilities required of cybersecurity specialists are problem-solving skills, technical and analytical skills, communication, basic computer forensic skills, hacking basics, multi-platform security expertise and other relevant skills.

The top cybersecurity experts to follow are given below.
- Eva Galperin
- Adam K. Levin
- Brian Krebs
- Bruce Schneier
- Eugene Kaspersky
- Daniel Miessler
- Steve Morgan
- Larry Dignan
- Anton Chuvakin
- Mikko Hypponen
- David Linthicum
- Kevin Mitnick
Table of Contents
1. Eva Galperin
Eva Galperin is the director of cybersecurity of the Electronic Frontier Foundation (EFF) and a technical advisor to the Freedom of the Press Foundation. Galperin is known for critical work in universal privacy and free speech, security and malware, nation-state spyware research and analysis.

Galperin’s passion for technology began when she was 12 years old. She got interested in computers at a young age because of her father, a computer security professional. Galperin’s father developed a desktop for her on a Unix/Solaris computer. The cybersecurity expert became a frequent contributor to Usenet discussion groups dedicated to science fiction novels and interactive text games. This access to a computer enabled Galperin to become involved in web development.

Galperin later studied political science and international relations at San Francisco State University and worked as a Unix system administrator in Silicon Valley. She previously worked at the US-China Policy Institute, where she assisted in conference planning and research on Chinese energy policy. Galperin began working with the EFF in 2007.
Ensuring privacy and security for the world’s most vulnerable people was the primary focus of Galperin’s work at the EFF. Galperin’s political science and technical expertise also aided in the growth of the foundation. Galperin has coordinated the Tor Relay Challenge for the Electronic Frontier Foundation, written privacy and security training materials (such as Surveillance Self Defense and the Digital First Aid Kit) and published malware research in Syria, Vietnam and Kazakhstan.

Galperin persuaded Kaspersky Lab, an antivirus company, to start openly notifying users of security issues when stalkerware was detected on the company’s Android app in April 2019. According to Galperin, authorities need to compel cybersecurity services to follow this pattern to achieve this higher benchmark because of the increased rivalry. She has also informed authorities in the United States to punish CEOs of companies that design and distribute stalkerware on hacking charges.
The username @evacide is for Galperin’s Twitter account with over 167,000 followers. Galperin is one of the best cybersecurity experts that specialists in the industry may look up to because she is well-versed in cyber threats.
Galperin has mastered the skills needed to secure networks and defend systems, computers and data from attacks, which can be extremely useful to other cybersecurity experts. Her depth of expertise can be a valuable resource for beginners in cybersecurity and companies.
2. Adam K. Levin
Adam Levin is a Stanford University and University of Michigan School of Law graduate. Levin became the youngest director of the New Jersey Division of Consumer Affairs at the age of 27. Levin resigned as Director of Consumer Affairs in 1982. Levin is a well-known consumer advocate and serial entrepreneur with over 40 years of expertise. Levin aims to raise awareness about identity management, privacy, credit and security issues among consumers, corporations and policymakers.
Levin co-founded Credit.com in 1994, an online financial services educator and solution provider that assists people in actively managing personal credit finances. Levin founded CyberScout, an online supplier of personal-touch identity management solutions, identity theft recovery services, breach services and data risk management solutions for enterprises, in 2003. Sontiq, now a Transunion company, acquired CyberScout in March 2021.

Levin discusses various security and personal financial subjects, including the benefits and drawbacks of credit, the ongoing struggle between convenience and security online, how professionals and businesses can better secure consumer and employee data and more.
Levin is a frequent speaker at conferences on cybersecurity, personal finance management, credit concerns in the age of IoT and cyber fraud. Levin has a Twitter account, @Adam_K_Levin and a Facebook page, Adam Levin. Levin has over 50k Twitter followers and is always fighting and sharing updates on scammers and identity thieves.
Following Levin on Twitter or any of his other social media handles can help individuals learn more about cybersecurity and current risks in many industries.
3. Brian Krebs
Brian Krebs, a journalist and investigative reporter from the United States, was born in 1972. Krebs graduated from George Mason University with a B.A. in International Relations in 1994. With no prior experience with cybersecurity, Krebs developed a strong interest in the subject due to a series of events. The first event was when a Chinese hacking team hacked Krebs’ entire home network in 2001 with Lion Worm. After that incident, Krebs was determined to learn everything possible about computer and Internet security and read almost everything on the subject.

Krebs worked as a reporter for The Washington Post from 1995 to 2009, covering technology policy, privacy and computer security and writing the Security Fix blog. Krebs is also known for conducting hacker interviews. Krebs now runs the KrebsOnSecurity blog, exposing data breaches at different companies. Krebs has interviewed many hackers over the years.

Following several threats and cyber attacks, Krebs has had a great deal of success reporting his experiences. Krebs was one of the first journalists targeted by swatters on March 14, 2013. However, on December 18, 2013, Krebs reported that Target Corporation had been hacked, resulting in the theft of 40 million credit cards. Krebs’s threat experience has aided his advancement in cybersecurity to the point of publishing a book on security, Spam Nation: The Inside Story of Organized Cybercrime—From Global Epidemic to Your Front Door. Krebs won the 2015 Prose Award for this work.
Kreb has a reputation for being a self-made expert and influencer. Krebs’ Twitter handle is @briankrebs, with more than 340,000 followers. The journalist also has a LinkedIn account.
Every career journey necessitates connecting with industry specialists. Cybersecurity specialists like Krebs are well-versed in cyber threats and should be followed for further data. Above all, the Krebs on Security news site, which focuses on in-depth cybersecurity reporting and investigations, will expose individuals to cyber threat trends and techniques.
4. Bruce Schneier
Bruce Schneier is a cryptographer, computer security expert, privacy specialist and author from the United States. On Jan. 15, 1963, Schneier was born into the family of Martin Schneier, a Brooklyn Supreme Court justice. Schneier earned a bachelor’s degree in physics from the University of Rochester in 1984 and a master’s degree in computer science from American University in Washington, D.C., in 1988. In November 2011, Schneier received an honorary Ph.D. from the University of Westminster in London, England.
As of November 2013, Schneier is a Lecturer in Public Policy at Harvard Kennedy School and a member at the Berkman-Klein Center for Internet & Society. He serves on the boards of the Electronic Frontier Foundation, Access Now, the Tor Project and EPIC and Verified Voting’s advisory boards.

As a computer security expert and a philosopher of the bigger concept of making the world a better place, Schneier thinks a lot about security. Schneier has authored numerous books, articles, essays and academic papers on various security topics, including computer security and cryptography.
Counterpane Internet Security was founded by Schneier, who served as the chief technical officer (now BT Managed Security Solutions). Schneier was the CTO of IBM for a short time until leaving at the end of June 2019. Schneier publishes Crypto-Gram, a free monthly internet newsletter about computer and other security topics and Schneier on Security, a security weblog. The blog is based on Schneier’s opinions and focuses on the most recent threats.
Schneier is an internationally known security technologist and author of numerous papers on the subject, who has been called a “security guru” by The Economist. @schneierblog, Schneier’s Twitter account, has over 139,000 followers.
5. Eugene Kaspersky
Eugene Kaspersky is the CEO of Kaspersky Lab and a Russian cybersecurity expert. On October 4, 1965, Kaspersky was born into a family of engineers (father) and historic archivists (mother). Kaspersky developed an early interest in mathematics and technology as a child. Kaspersky began attending the A.N. Kolmogorov boarding school, supervised by Moscow University, and specializing in arithmetic as a 14-year-old.

At 16, Kaspersky enrolled in a five-year program at the KGB Higher School’s Technical Faculty, which trained intelligence operatives for the Russian military and the KGB. He earned a bachelor’s degree in mathematical engineering and computer technology in 1987. Shortly after graduating from college, Kaspersky joined the Soviet military intelligence organization as a software engineer.

When the Cascade Virus infected Kaspersky’s computer in 1989, Kaspersky became interested in IT security and needed to develop a tool to remove the virus. His cryptography training aided in the analysis of the encrypted virus, understanding the behavior and finally building a removal program.
In 1990, as a technology enthusiast, Kaspersky began assembling a team of like-minded researchers to produce the AVP Toolkit Pro antivirus application. The software was certified as the most effective antivirus software globally by the University of Hamburg after four years. Kaspersky and his colleagues started an antiviral company based on this successful track record.

As the head of research, Kaspersky co-founded Kaspersky Lab in 1997 and helped discover instances of government-sponsored cyber warfare. Kaspersky became the CEO of Kaspersky Lab in 2007 after contributing to the company’s growth through security research and business skills.
Kaspersky also holds an Honorary Doctorate of Science from Plymouth University in the United Kingdom. Kaspersky often provides cybersecurity lectures at universities throughout the world and keynotes at major business conferences and events.
Kaspersky is now one of the most successful IT security providers globally, with operations in over 200 countries and territories. Over 400 million people are also protected by the company’s cybersecurity products worldwide.
Kaspersky has over 185,000 followers on Twitter as @e_kaspersky and has been in the cybersecurity business for almost 30 years. Also known on LinkedIn as Eugene Kaspersky.
Kaspersky is a trained and dedicated cybersecurity expert who can educate others on becoming experts as well. By following Kaspersky, people will access cybersecurity issues, tips, hacks and preventative actions against various cyber threats.
6. Daniel Miessler
Daniel Miessler has over 20 years of experience as a cybersecurity expert, speaker, podcaster and book writer. Meissler’s background includes technological evaluation and implementation, executive-level advisory services consulting and the creation and management of industry-leading security programs.

Meissler said in an interview that his interest in computers arose after he left the Army for university. After some months, Meissler was already constructing websites for a professor and assisting the lab administrator in defending the network against threats.

Meissler leads and presents security talks about cybersecurity careers and personal experience working with many companies worldwide. Meissler conducts presentations and takes part in panels all around the world. Meissler’s criticism has also appeared in many major publications worldwide, including the Wall Street Journal, Forbes, BBC, Computer World, Threat Post, Financial Times and many others.
Unsupervised learning is a podcast and newsletter created by Meissler, who believes in a self-taught form of learning. The Unsupervised learning newsletter has over 42,000 subscribers, while the podcast receives 12,200 monthly downloads on average.
Meissler is a mentor to some people on various cybersecurity and intelligence topics. Meissler uses his social media accounts and blog to act as a security leader and writer, analyzing the convergence of security, technology and society and projecting society’s future with technology.
@DanielMeissler, Meissler’s Twitter account, has over 119,000 followers. Meissler’s social media handles include Daniel Meissler on Facebook, LinkedIn and GitHub.
Meissler is one of the cybersecurity experts serving as an embodiment of knowledge for anyone seeking mentorship, advice and forecasts regarding the future of technology. People following Meissler will get insight on any cybersecurity topic, as well as advice on how to establish a cybersecurity career.
7. Steve Morgan
Steve Morgan is a well-known cybersecurity expert, researcher, journalist and publisher who is also the founder of Cybersecurity Ventures and Editor-in-Chief of Cybercrime Magazine. Morgan co-authored a brilliant book: “Women Know Cyber: 100 Fascinating Females Fighting Cybercrime”. Morgan has been recognized with awards, namely LinkedIn’s 5 Security Influencers to Follow, Onalytica’s Who’s Who in Cybersecurity and the RSA Conference’s Top 100 Cybersecurity Influencers.


Along with Business Insider, Reuters, The New York Times and The Wall Street Journal, Morgan was ranked among the top 10 cybersecurity journalists to follow in 2021.
@CybersecuritySF is Morgan’s Twitter account with over 17,000 followers. Steve Morgan’s LinkedIn account is also available for viewing.
Morgan is a cybersecurity specialist who keeps the public up to date on the latest cybersecurity data, facts and trends. Anyone seeking cybersecurity news can follow him for further information and insights on cybersecurity news and trends.
8. Larry Dignan
Larry Dignan is a Columbia School of Journalism and University of Delaware graduate. Dignan has worked as a reporter and editor for over 15 years. Dignan worked as an executive editor at eWeek before becoming the Executive Editor of News and Blogs at ZDNet in 2006. He supervised the ZDNet blog network during this time, including some of the industry’s most authoritative and well-respected voices.


Dignan was made Editorial Director of TechRepublic Inc. and Editor-in-Chief of ZDNet Inc. in 2008. Dignan led the editorial team in ZDNet coverage and events that benefited business professionals. Dignan continues to blog every day for “Between the Lines,” a thorough overview of events in the business technology area.
Dignan is well-known in the technology and financial sectors. Recently, he has been the Editor in Chief of Celonis since December 2021.
Dignan is a successful individual who has taught, mentored and managed technology publications. Dignan’s Twitter username, @ldignan, has over 31,000 followers. Individuals looking for advice and updates on technology, data analytics and business should follow Dignan for deep insight on related topics.
9. Anton Chuvakin
Anton Chuvakin holds a physics degree from Moscow State University and a PhD from Stony Brook State University. Chuvakin co-authored the book “Security Warrior,” published in 2004. Afterward, these “Security Warrior” editions were published in German, Polish and Japanese. PCI Compliance and Logging and Log Management: The Authoritative Guide to Understanding the Concepts Surrounding Logging and Log Management are two other works by Chuvakin. As a subject matter expert, Chuvakin has written several papers on log management, SIEM, correlation, security data analysis, PCI DSS and security management.

Chuvakin is the Research Director of Gartner’s Security and Risk Management Strategies (SRMS) team for Technical Professionals (GTP) and works with the security solution strategy at Google Cloud. Chuvakin was earlier a partner with Security Warrior Consulting. Chuvakin once worked as Director of PCI Compliance Solutions at Qualys, a U.S. vulnerability management firm, Chief Logging Evangelist at LogLogic, a U.S. log management and intelligence company and Security Strategist netForensics, a U.S. security information management company.
Chuvakin’s social media accounts include @anton_chuvakin on Twitter, which has over 35,000 followers, and Anton Chuvakin on LinkedIn.
10. Mikko Hypponen
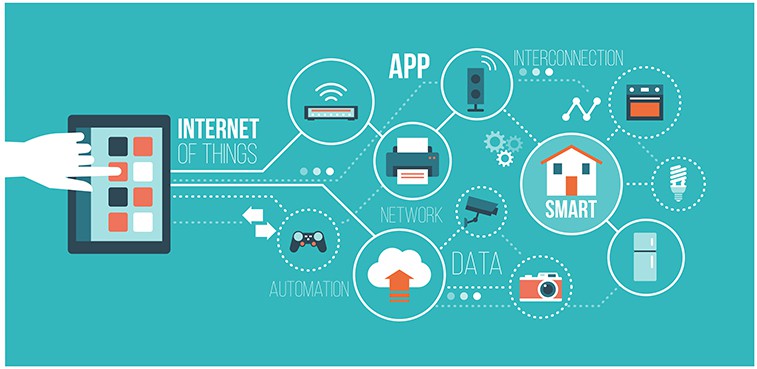
Mikko Hermanni Hyppönen is a columnist and cybersecurity researcher. On Oct. 13, 1969, Hyppönen was born. Hyppönen is the creator of the Hyppönen Law, which asserts that every appliance labeled as “smart” is vulnerable.

Since 1991, Hyppönen has served as Chief Research Officer of F-Secure in Finland. Hyppönen worked with law enforcement in the United States, Europe and Asia on cybercrime cases in the 1990s and advised governments on the subject. Hyppönen’s team knocked down the Sobig.F botnet at these times. Hyppönen collaborated with Vanity Fair on a feature called The Code Warrior in 2004, which looked at his involvement in fighting the Blaster and Sobig Computer worms.

As a professional speaker, Hyppönen has spoken at conferences like Black Hat, DEF CON, DLD and RSA. Hyppönen has also spoken at TED, TEDx, DLD, SXSW, Slush and Google Zeitgeist, among other general-interest events. Since 2007, Hyppönen, together with Yevgeny Kaspersky, Hamadoun Touré, Fred Piper and John Thompson, has been a member of the advisory board of IMPACT (International Multilateral Partnership Against Cyber Threats).
Hyppönen’s social media accounts include @mikko on Twitter and Mikko Hypponen on LinkedIn.
Hyppönen can be followed and listened to by techies and anybody who wishes to stay updated on cybersecurity trends. Hyppönen frequently shares thoughts and speaks on tech topics relevant to both businesses and individuals.
11. David Linthicum
David Linthicum is an application integration and e-Business expert who graduated from George Mason University. In addition to being a cloud computing thought leader, executive, consultant, author and speaker, Linthicum is the Chief Cloud Strategy Officer of Deloitte Consulting LLP. Linthicum has been the CTO of five firms and the CEO of three more. Linthicum is the author of 13 books and over 5,000 articles about computing and has appeared on countless radio and television shows for expositions.

Linthicum’s Twitter handle is @DavidLinthicum and his LinkedIn username is David Linthicum. He also maintains a blog, InfoWorld, where he posts various expositions about his field of expertise.
Through Linthicum’s courses, individuals and organizations growing in the tech space can benefit from Linthicum’s expertise and perspective.
12. Kevin Mitnick
Kevin Mitnick was born on August 6, 1963 and is a convicted hacker, a cybersecurity expert and book writer. Mitnick is a hacker and cybersecurity professional who started as early as 12 years old. Mitnick first acquired an entry to the computer network when he was 16.

Mitnick was accused and convicted in 1988 for breaking into DEC’s computer network and stealing the company’s software. He suffered a 12-month prison term and three years of supervised release. Mitnick broke into Pacific Bell’s voicemail computers at the end of his supervised release. Mitnick’s ability to hack into any computer and get illegal access resulted in a string of arrests and convictions.

Mitnick now manages Mitnick Security Consulting, LLC, a security firm. He’s also the Chief Hacking Officer and a co-founder of KnowBe4, a security awareness training company and a member of the Zimperium advisory board, a company that creates a mobile intrusion prevention solution. Mitnick has worked as a professional security consultant, public speaker and author since 2000. He provides security advice and Social Engineering classes to businesses and government organizations.
Mitnick is now known as “the world’s most famous hacker” and has been featured in numerous news and magazine publications worldwide.

Mitnick and his team have a proven track record of successfully breaching any system’s security using a combination of technical vulnerabilities and social engineering. He also helps build the world’s most popular security awareness training programs to prevent social engineering and boost security effectiveness in his capacity as Chief Hacking Officer of KnowBe4.
Mitnick has a Twitter account, @kevinmitnick, and a LinkedIn account, Kevin Mitnick.
Mitnick possesses the necessary skills to train, lead and educate others on cybersecurity issues. People should follow Mitnick to gain a solid understanding of cybersecurity and the capacity to recognize potential dangers.
What does a Cybersecurity Expert Do?

Cybersecurity professionals are in charge of an organization’s software security. Experts must be proactive in spotting hardware and software problems. Cybersecurity also incorporates firewalls into the network infrastructure in the event of danger. The importance of cybersecurity experts’ jobs cannot be overstated in any firm. IT security rules and documentation must be maintained by security specialists. Professionals must identify security flaws and devise a plan of action.
Cybersecurity experts can work as information security analysts, chief information security officers, security architects, malware analysts and security engineers.
How can Cybersecurity Experts Help You Secure Your Company?

The more the use of technology by businesses, the more the potential for scams and security problems. That alone is sufficient to employ cybersecurity professionals who can assist businesses in defending against cyber threats. A cyberattack is expensive and can harm a company’s reputation.
One of the advantages of hiring a cybersecurity expert is having access to tips for keeping business’ data secure. Cybersecurity experts know how to set up firewalls, back up data and encrypt important data for businesses. The goal of consulting cybersecurity specialists is to protect the company’s data.
Note:
Another benefit of having a cybersecurity professional is that computer security specialists can use IT approaches on infrastructures. The computer security specialist is also in charge of assuring the safety of sensitive data. Because of professional responsibility in monitoring the flow of information, verifying bandwidth usage and preventing unauthorized users or even hackers from accessing critical material, these experts can also be classified as information security analysts.
Unlike the employee’s manager, cybersecurity professionals can assist employees with login information and access requests. Computer security specialists are the best choice for password resets and other access needs.
Similarly, computer security experts will protect the security of customer data and assist with any technical issues that customers may encounter.
Cybersecurity understands and will give all digital protection required by a company to protect the workers from risks such as adware and ransomware. Most significantly, productivity will increase because viruses can slow computers down considerably.
Why Should You Follow Cybersecurity Experts?

Professionals with the ability to secure networks and protect systems, computers, and data from attacks, damage and unauthorized access are in high demand. Businesses must follow the advice of a cybersecurity professional to learn and practice all of the strategies for avoiding cyber threats. Users can learn from professionals by following experts on social media pages, blogs or websites, reading published books or listening to podcasts.
Which Social Media Accounts do Cybersecurity Experts Have?
Cybersecurity experts primarily use Twitter, LinkedIn and Facebook accounts. To follow any cybersecurity expert, users must first sign up on those platforms.
Do Cybersecurity Experts Have Blogs and Websites to Follow?
Yes, cybersecurity specialists have blogs and websites to read and learn more about cybersecurity updates. David Linthicum, for example, has a blog at InfoWorld where he writes regular pieces. Mikko Hypponen also has his own website, mikko. Adam Levine has a website dedicated to cyber fraud, identity theft and privacy. Brian Krebs is the author of the KrebsOnSecurity blog, which documents data breaches at various corporations. One of the best cybersecurity blogs and websites to read about security-related topics is Bruce Schneier’s blog.
How to Become a Cyber Security Expert

Cybersecurity necessitates a solid educational foundation, technological skills and specific learning duration. The most important quality of a cyber security expert is proficiency and interest in computers. Some other important skills are in-depth knowledge of computer operating systems, hardware and software, problem-solving skills, ability to work well under pressure, solid telecommunications knowledge, strong mathematical knowledge, determination, ability to work and learn independently and excellent attention to detail.
This is important:
Skills are the driving force behind becoming a cybersecurity specialist. A strong educational background in cybersecurity or an IT-related course is required. People with a cybersecurity associate’s degree, bachelor’s degree or master’s degree can work as cybersecurity specialists. Many cybersecurity specialists obtained jobs after earning a degree in a related field such as computer science, engineering, or mathematics.Certification is the next step after earning academic knowledge. Certification is also required for cybersecurity careers to be competitive in the field. Examples of cybersecurity certificates are Security+, a CompTIA certification, Network + (for networking infrastructure and operations), the Certified Information Systems Security Professional (CISSP), the Certified Ethical Hacker (CEH) and many others. It’s crucial to keep track of the certifications that employers are looking for while job hunting.
Having good experience in the profession is another approach to advance in a cybersecurity career. Experience can also be in a structured internship or other formal hands-on learning.

After learning everything there is to know about becoming a certified cybersecurity expert, it’s critical to network with the professionals and groups who support the growth and development of emerging cybersecurity experts.
Cybersecurity, like other careers, necessitates commitment. The estimated time to become a Cybersecurity specialist varies depending on one’s education, experience and certifications. With prior experience, some people can get into an entry-level cyber security role in two to four years. A certification is a rapid approach to becoming an expert for someone who has already worked in IT and has sufficient experience.

