Android devices are popular and widely used for several reasons. Like most mobile devices, Android devices enable individuals to store important personal and business data and can be used to access the internet as well as email, university systems, banking information, personal and business accounts. Also, Android devices are relatively cheap, hold excellent computing power, and are compact.
Android is a collection of software developed for mobile devices that features middleware, core applications, and an operating system. Android devices range from Tablets, and smartphones to e-readers. But while the device is great, like all software, Android is vulnerable to malicious attacks, hacks, and other threats. However, this can be tackled using the best privacy apps. This article lists the best privacy apps for android in 2023. Other key aspects will also be discussed, including identifying the vulnerabilities faced by Android devices, the need for privacy, things to look for, and security tips.

Here you can see the list of best privacy apps for Android.
- Keepass2Android
- Syncthing
- OpenKeychain
- Bitdefender Mobile Security
- Folder Lock
- Google Find My Device
- Glasswire
- K-9 Mail
- Resilio Sync
- Simple Mobile Tools
- Musicolet
- Bouncer
Table of Contents
1. Keepass2Android
Keepass2Android (K2A) is a free and open-source end-to-end password manager app made for Android. The privacy app is ideal for keeping passwords safe and works well with the well-known KeePass 2. x Password Safe for Linux, Windows, and Mac devices.
Keepass2Android is very important because the privacy app can integrate with almost all Android browsers including Safari, Internet Explorer, Chrome etc. K2A has a QuickUnlock feature that enables users to unlock a database once with the input of the user’s full password and subsequently reopen the database by simply typing a few characters. Besides, Keepass2Android allows files to be accessed from the web or cloud. The password manager enables the integration of Soft-Keyboard for the input of users’ credentials; this prevents clipboard-based password sniffers. Furthermore, K2A offers support for file attachment, string fields, tags, and so on. The privacy app also has a search dialog that is similar to the one in Keepass 2. x. Keepass2Android has a file size of 33M.
There are two versions of K2A that can be installed; Keepass2Android (standard version) and Keepass2Android Offline. The latter is ideal if files won’t be accessed from the web or cloud. However, the former is the standard and preferred edition. The installation process involves going to the Google Play Store and searching for the app. Once located, tap the app to install, tap again to accept the installation, and then allow for the installation process to complete.
The next step is the use of the app. Here, a new database will need to be created. To do this, open Keepass2Android and click on “Create New Database”. Next, input a password to secure the database. Scroll down and confirm the password entered. Users can choose to add a key file for additional security; to do this, click on the checkbox, then click on “create database”. Once the database has been created, the user will be required to enter the password to unlock the database. Upon opening the database, users can choose to add entries. This is done by simply clicking on a group, then clicking on the button and the key icon. An entry can be composed of email, credit card, ID card, standard entry, membership, secure note, and wireless LAN. Each entry consists of a set of options that are specific to the type of entry chosen. Once done with the database, click on the lock button located at the top-right corner of the window to securely lock the database.
There are several advantages to Keepass2Android. For starters, the privacy app can store passwords locally on a user’s device or a cloud service such as Google Drive and Dropbox. With K2A, users can copy and paste usernames and passwords directly from the database onto the log-in screen; alternatively, users can turn on the autofill service which enables for automatic population of login details. Also, the password manager features several KeePass ports for Android. These ports are mostly open-source and can open regular KeePass files. Examples include Mac, Linux, Android, and iOS; other examples include Firefox, Chrome, Internet Explorer, Safari, and other popular browsers. Besides, K2A has a better android integration than most commercial products. Moreover, K2A does not depend on the Android clipboard function to operate.

On the downside,Keepass2Android is only available on the Google Play Store and is only updated through the same channel. This is worrisome as Google could inject malware or other viruses into an update. Also, the installation process is rather long and tedious and not best suited for impatient users.
There are no fine prints with K2A. The password manager is completely free. However, users can choose to make donations via the website to support the open-source effort, but this is done voluntarily.
Keepass2Android is a very secure password manager. By default, the password manager uses 256 ciphers along with SHA-256 hash authentication. The app encrypts notes, names, passwords, and so on. K2A offers process memory protection so that even when a device’s OS dumps the K2A to disk, the user’s password won’t be leaked.
2. Syncthing
Syncthing is a continuous, open-source P2P (peer-to-peer) file synchronization application that enables files to be synchronized across two or more devices in real-time. The application is available for macOS, Android, Solaris, Darwin, Windows, and BSD. Files can either be synchronized on a local network or over the internet.
Rather than work off a client-server structure, Syncthing functions off a peer-to-peer architecture. Devices (computers) that are connected to a Syncthing network will each have copies of files that are in a user’s shared folders and then carry out changes and push new content via peer-to-peer connections. This means that the deletion, creation, or modification of files on one device will automatically be replicated in other synchronized devices.
Syncthing is an important privacy tool because the application enables the backup of data and files without having to trust a third-party agent. This is because the data is backed up to a server or a computer device that gives the user direct control, thus eliminating storage by a third party. Also, the encryption used in the privacy tool is end-to-end, this means once a data is encrypted on a device, only the user can decrypt the file or data. Besides, Syncthing provides document management, data security and enables data capture and file storage. Also, this privacy tool supports drag and drop, backup, encryption, backup management as well as data storage management. Freelancers, startups, SMEs, agencies, and enterprises will find this privacy tool useful. Besides, users who do not wish to download the app from Google Play Store can do so through F-Droid. Syncthing supports File Versioning, with this a user can choose to archive older versions of data and files when these files are deleted or saved. The files can then be accessed at a later date. File versioning is configured per folder; hence users can select the number of previous files to be archived. Syncthing is quite a small file, with a size of only 17.9MB.
Syncthing is easy to download requiring no signup before use. All that needs to be done is to download the relevant program file to a device that’s to be used to synchronize. If for instance, a user wishes to synchronize 10 PCs and an Android phone, the user will need to download the windows files. Upon downloading the files, the files will need to be unzipped. No further installation is required (a default folder for synchronization will need to be created though). Running the privacy tool will lead to the opening of a web interface. Also, a default sync folder will be created when Syncthing is first launched. The first step is to add a new device. Upon downloading the app to an Android device, the device ID will then be shared to the Windows PC via email. This device ID is an exclusive and cryptographically protected identifier created as a part of the key generation the first time Syncthing commences. These IDs are not necessarily a secret as the IDs are part of the public key. To connect the Windows PC with the Android phone, scan a QR code using the phone. Next, generate a folder on a device. If a folder already exists, then share the folder with the other devices. A notification will be sent to the other devices (the notification will appear like a standard Android notification on the phone). Users can then select where to keep the paired sync on the other device (the PCs in this case). Click the save button located at the top-right corner of the screen. Once done, the devices have been synchronized and are ready to use.
There are pros and cons to Syncthing. On the bright side, the privacy tool provides a secure means of syncing multiple operating systems and computers. With Syncthing, users can create personal peer-to-peer synching without the need for third-party servers. Also, Syncthing is an open and transparent source project.

On the other hand, Syncthing can be quite challenging to install and run. This is because the installation process of the privacy tool is different from other software. Also, the documentation of Syncthing is often out of date. The privacy tool does not contain many of the secondary features known with other cloud storage services. Besides, the options provided are often confusing and difficult to grasp.
Syncthing is a free and open-source privacy tool, requiring no fee for the services provided.
Syncthing is private and secure. Data are saved directly to a location of choice and third-party servers are not needed. Since Syncthing encryption is end-to-end, relay servers won’t be able to read user’s data. Also, the privacy tool uses the TLS protocol, this is equivalent to the HTTPS protocol used by browsers. The use of the TLS protocol offers encryption with updated algorithms and also provides authentication to ensure that communication between clients is secure and no adversary can intercept.
3. OpenKeyChain
OpenKeyChain is an open-source mobile app built for the Android operating system. This privacy tool offers strong, user-based encryption that works with the OpenPGP standard. With this, users can decrypt, encrypt, sign and verify signatures for files, emails, and texts.
OpenKeyChain, like most modern encryption, functions on digital keys. The privacy tool manages and stores users’ keys and that of others in the communication chain; these keys are stored on Android phones. The privacy tool also enables users to locate and store the public keys of other users. Besides, if a user receives a file and the public keys received are saved, the user can verify the authenticity of the file sent and decrypt it if needed.
OpenKeyChain is important for many reasons. For starters, the privacy tool is open source, hence, OpenKeyChain is designed to be trusted. Users can review and verify every part of the tool. Cure53, an independent security audit carried out an intensive security audit of OpenKeyChain and declared that “[…] none of the spotted issues were considered to be of a critical severity in terms of security implications. The latter is a significant and impressive result for an app of this complexity and relevance.” Thus, OpenKeyChain is safe, secure, and private. Also, the Android privacy app synchronizes with K-9 Mail to offer end-to-end capabilities. Asides from this, other apps such as PGPClipper, OverSec, Password Store, Conversation, andOTP, oandbackup, PhotoPGP, PGPAuth, and FairEmail also work with OpenKeyChain to provide encryption.
OpenKeyChain is quite easy to install. First, locate and open the Google Play Store on an Android device and search for OpenKeyChain. Next, locate and click on the entry and click on the install button. If there are permissions listings that need to be accepted, then click on Accept. After this, allow the installation to be complete. Upon completion, the OpenKeyChain should appear on the home screen of the device or in the App Drawer, or both. Click on the launcher to begin use. The next step involves the creation of the key. To do this, head on to the OpenKeyChain real window and click on the “CREATE MY KEY” button. Follow the creation wizard. To create a key, the name of the user will need to be inputted along with an email address and a strong password. Finally, click on “CREATE KEY”. The key has now been created and is ready for use.

There are many benefits of OpenKeyChain. One of these is that OpenKeyChain has a good design with good performance. The app is available for download not just on Google Play Store but on F-Droid as well. Also, OpenKeyChain is compatible with lots of devices and offers excellent and useful support. Besides, the app’s simplified design allows for easy and efficient management. Furthermore, the privacy tool is safe and secure and this is verified by the independent audit carried out by a reputable security firm.
However, despite being one of the best privacy apps for Android, the app lacks advanced security features.OpenKeyChain is, however, a free, open-source privacy app for Android. Hence, users are not charged a fee for any service rendered. However, users can make voluntary donations. These donations can be made using PayPal, Flattr, and Bitcoin.
OpenKeyChain secures messages with end-to-end encryption. The encryption can be used to send secure emails and messages from an Android device. The app uses the OpenPGP encryption standard on Android phones. This encryption protocol ensures that messages can only be read by people the messages are intended for. These messages can also be signed digitally so that people getting the messages can verify the sender’s identity.
4. Bitdefender Mobile Security
Bitdefender is known to produce antiviruses for computers, but beyond that, Bitdefender produces antiviruses for mobile devices as well. Bitdefender Mobile Security keeps all Android devices safe from existing and new online threats
Bitdefender Mobile Security is a privacy tool suitable for IOS and Android operating systems. The function of the app is to offer a smart anti-theft experience and a supreme cloud-based malware detection system. The mobile security app for Android reacts immediately to any perceived online threats without compromising the performance of the system.
Several features make Bitdefender Mobile Security a very important privacy tool for Android devices. The VPN is fast and safe and enables users to surf the internet anonymously. Besides, the tool enables users to locate, lock and wipe Android devices in case of theft. There is also an account privacy feature which verifies if the users’ email account has been breached. Also, the privacy app has a minimal effect on battery life.
Bitdefender Mobile Security for Android is easy to download and install. To download the app, head to the Google Play Store and search and locate Bitdefender Mobile Security. Having located the app, click on “install” to download the privacy app on an Android device. Once the download is complete, open the app and check the box beside the “I agree with the Subscription agreement”. After reading the terms and conditions, click the continue button to proceed. Next, sign in to the app by inputting a username and password. Once in, click on “get started” located on the configuration screen. To complete the installation process and protect web browsers, the Web Protection feature in the app will need to be turned on. To do this, click the “activate” button. The accessibility screen should appear: here, click on the Bitdefender Mobile Security app. Next, turn on the “use Bitdefender Mobile Security” feature and select “allow” to confirm the action. The Accessibility feature is needed as the service ensures that the privacy app can scan and block malicious websites found in browsers. Head back to the installation screen; users will have the option of scanning Android devices for malware. Users can either choose to perform the action immediately or click on “skip” to perform the task at a later date. If the former was chosen, then the app should be given time to scan the various files on the device. Once the scanning commences, wait until the process comes to an end. The privacy app is now installed and ready to protect the Android device.

There are lots of pros and a few cons to Bitdefender Mobile Security. Firstly, it offers excellent antivirus protection for mobile devices and this is confirmed by independent labs. The privacy tool provides superfast scanning and has a robust anti-theft feature. Also, users get SIM alerts in case there’s a threat. Moreover, Bitdefender Mobile Security has an outstanding UI design and supports remote antivirus scans. The tool is also quite affordable. The app has many useful features while having minimal system impact.
There aren’t many negative sides to Bitdefender Mobile Security. However, the privacy tool does not feature call blocking or a remote camera. Also, users will need to connect to the internet for malware scans. The unlimited VPN option is also very expensive.
While the Bitdefender Mobile Security is free to download on Google Play Store, users will need to pay to use the app. The Bitdefender Mobile Security is priced at $14.99 per account and is billed annually.
Bitdefender Mobile Security for Android offers a lot of security features to ensure the protection of Android devices. These features include Web Protection, Anti-theft, Scam Alert, On-Demand & On-Install scan, as well as WearON. Besides, the privacy tool offers malware detection and protection and supports account privacy.
5. Folder Lock
Folder Lock is a fully-featured web security software designed to serve agencies, enterprises, and individuals. The app offers end-to-end security solutions including secure web access/ restoration, secure data storage, compression, and multiple system support, and encryption. Folder Lock is one of the top 10 privacy apps for Android and is known to be the most downloaded security application with more than 26 million users.
Folder Lock performs a variety of functions. The revolutionary security application enables users to protect folders, drives, and files through password locking. The security tool is designed to encrypt vital files on the fly and ensure they are backed up in real-time. The app also protects portable drives, cleans history, and shreds files and drives. With Folder Lock, users can hide, lock, or password-protect files, drives, and folders. The software gives users the option of backing up encrypted files to a secure online account, thus ensuring data and files are synchronized at all times.
Folder Lock is important to users for many reasons. Users can get the app installed and running in no time. Upon installation, Folder Lock can lock folders and files easily. But beyond protecting sensitive data, Folder Lock is also capable of securing files to a protected USB key or the cloud. Besides, the app can shred files and manage Password Wallets. Also, the privacy-protection tool can erase usage history and paper-trails of temporal data. The application approaches file security from two distinct angles; the first approach is that files are locked in place, while the second approach involves files being dragged to a managed locker where the files are then encrypted. The first approach is generally preferred as users can apply for password protection, wherein the file temporarily disappears when the lock is active and reappears when desired. On the other hand, folders and files can reside in an encrypted drive and will have to be unlocked to be accessed. Alongside the Locker encryption is the Secure Backup, a feature that copies the encrypted drive to the cloud. Users can then retrieve files from the Secure Backup online storage if a hardware failure or theft is encountered.
The download, installation, and use of Folder Lock is simple and easy. To download the app, go to Windows Explorer or any other browser and search for the app. Once located, click on the app and select download to initiate the download. Upon completion, open the app to begin use. To lock a folder or file, simply drop the file or folder on the Folder Lock. The file or folder will appear on the Folder Lock and disappear from the previous location (Windows Explorer) in a flash. A menu within the program can also be used to lock folders, drives, and files. However, the Windows drive cannot be locked. The Lock Folders page located on the main window contains a list of all locked items, each having a green padlock icon. Users can choose to unlock the items by clicking on the files; these files will vanish from the Folder Lock and reappear in the Windows Explorer. To access the files while still being locked, simply click on “protection off”, this leaves the files inside the Folder Lock, with a red padlock icon replacing the green. The file will leave the Folder Lock and reappear in the Windows Explorer for use. The app can be configured so that when the tool shuts down and then restarts, the protection is automatically turned on.
Folder Lock is beneficial in many ways. The app offers secure online backup, while encrypted lockers protect folders and files. Also, Folder Lock can lock folders and files, thus making these files and folders invincible. Besides, the software supports file shredding and allows for free space shredding. Files can be self-decrypted with Folder Lock. Folder Lock also offers lots of other useful bonuses including USB locker distribution.

On the downside, locked files aren’t encrypted, they are only locked. Also, users are required to pay a separate subscription fee for secure backup. Moreover, the product serial number takes the place of the master password and this is done by default. Folder Lock lacks 2FA security too.
Folder Lock isn’t a free security tool. The software can be purchased for $39.95; this entitles a user to indefinite unlimited use. However, users can try out the free trial which can be used up to 25 times.
Folder Lock is secure, even if the software isn’t the most secure security software around. For starters, while files aren’t encrypted, they are hidden using Kernel-level filtering. The app also features a stealth mode, this ensures that snoopers searching through the system won’t be able to find any hidden or locked file/folder. Also, files and folders can be protected using passwords.
6. Google Find My Device
Google Find My Device (My Device) is an extension of the Google Play Protect and a part of the broader Play Services. This is a set of utilities created to protect users’ mobile devices from malicious content and protect a user’s device from thieves or hackers. Google leverages machine learning skills to scan and verify apps installed on mobile devices, and although the feature has been in existence for a long time, Google is simplifying and making the process more visible to users.

The function of Find My Device is to enable users to ring or wipe a device from the internet. Users can locate lost Android devices and lock the device until the phone is retrieved. With My Device, users can see tablets, watches, and phones on a map. Even if a real-time location isn’t available, users will be able to see the last known location.
The importance of Google Find My Device stems from the features and uses of the software. One of the uses of this security tool is the discovery of device location. Upon opening the website or app, users will be able to check the location of the device; the location is automatically displayed on the map. Although the location is approximate and can only be seen if the GPS of the device is turned on, the software can help locate stolen phones.
Also, Find My Device can be used to ring a missing phone around the home. With a simple click on the My Device tool, a phone can ring for as long as five minutes even if the phone is set on vibrate or silent.
Note:
The device can also be used to keep data safe by locking the device. To do this, a user can simply click on the “secure device” option in the software and then input a phone number and recovery message, both information will be displayed on the lost device’s screen. Adding a phone number will help anyone who finds the device to give the owner a call by simply tapping the number on the screen. And even if the phone is stolen, locking the phone will ensure the thief is unable to use the phone.Finally, Find My Device can also be used to erase all data on the device. For times when a phone is stolen and there is no chance of getting the device back, a remote factory reset can be performed. This action will erase all the data from the phone. With this, users can be assured that no one will be able to use the personal data on the device in the event that a phone is stolen. Although the function only works if the device is connected to the internet, the data will be deleted as soon as the device is connected to the internet.
Find My Device can either be downloaded through the Google Play Store or the website. To install the app from the Play Store, search for Find My Device and click on the three dots seen on the first result. Next, select install. Once installed, sign in to the app from a Google account. Open the app and choose the Google account to go with. Tap the continue button; input Google account password and click on the “sign-in” button. Next, allow the app access location. The app is now installed and ready to use.
There are many advantages to Find My Device. The app helps to track a device if stolen or lost. Find My Device also enables users to remotely access a device. Also, with Google Find My Device, users can lock a phone, thus making the device useless to thieves. The app can help erase or delete data from a stolen phone thereby protecting the user from identity theft, fraud, or other criminal offense that may be carried out by a thief.
But despite the app’s sterling performance, there are a few limitations to the software. The app isn’t battery efficient—My Device is a battery draining app. Also, most of the tool’s functionality can only work if the device is online or turned on; this includes tracking, data erasure, and so on. Besides, tracking of location is often not on a real-time basis, but mostly approximate location.
Google Find My Device is a free download from the Google Play Store or any browser.
My Device is focused on phone tracking rather than data encryption. With the app, users can lock devices using a password, PIN, or pattern. Stolen or lost phones can also be found by sending a phone number or message to the lock screen. Also, the app can erase or permanently delete data from a device (but not from the SD card). Also, the app’s tracking system enables users to track the location of a device.
7. Glasswire
Glasswire is an Austin (Texas) based Microsoft partner. The software is a new firewall and web monitor with a built-in firewall. Glasswire has more than 27 million downloads and offers features including bandwidth usage tracking and internet security.
Glasswire presents past and present network activities in an easy-to-decipher graph. The function of Glasswire is to monitor remote servers, manage firewalls and help users understand network activities. With Glasswire users can block applications from accessing the web. The software can also see if a PC is communicating with other PCs using a network tracking graph. The function of Glasswire is to block spyware on computers and mobile phones, including Android.
Glasswire is important for the many features the application offers. These features include a network time machine, visual network monitoring, bandwidth usage monitoring, Wi-Fi evil twin detection, internet privacy protection, RDP connection detection, and network or Wi-Fi network user detection. The software features multiple remote server monitoring which tracks network activities of various apps. Also, Glasswire ensures gaming and Voice over IP (VoIP) is stable, whether through remote access or a computer. The software is also important because there is a lockdown mode that can be activated to block all network activity. There’s also a mini graph on the system to make the monitoring process easy and simple.
Glasswire is also easy to use. Users can monitor the internet without needing to open the whole application. There are several profiles for work and home too. The application sends a notification for changes to the internet whether past or present; these changes are either sent to a mobile device or desktop computer. The privacy app has speedy connections making denial or approval of connections very fast.
Glasswire can be downloaded from various sources including Google Chrome, Microsoft Edge, Mozilla Firefox, etc. To download, type the app’s URL into the browser and click on download. Once downloading is complete, double-click on the application to start the installation process. After this, tap on “Next” and follow the instructions to install the software.

Glasswire is easy to use; the application enables users to see the direction of traffic on a device. Glasswire has an excellent interface with full functionality and easy-to-use tabs. The security tool is safe and secure, offers great convenience and speed. Also, Glasswire blocks intrusive apps and offers malware and phishing host alerts. Furthermore, the application exposes apps that use a lot of bandwidth while also offering full mobile backup support. There are, however, lots of ad pop-ups that interrupt use and Glasswire does not provide any antivirus properties.
Glasswire offers both free and paid services. The free trial is free but there is a Basic, Pro, and Elite plan to choose from after the free trial expires. The Basic plan costs $39 while the Pro and Elite plan cost $69 and $99 respectively.
Glasswire is a well-secured privacy tool. The application detects malware, spyware, bandwidth hogs, and misbehaving apps. Once detected, the software blocks off these malware and apps. Also, the software alerts users of changes to apps or computers that could indicate malware.
8. K-9 Mail
K-9 Mail is an open-source android software that enables users to easily break down large volumes of emails. The program is positioned as a replacement for default mail apps common with most phones. K-9 supports IMAP mailbox and POP3 mailbox along with IMPA IDLE.
K-9 mail functions as a form of replacement for default mail on Android phones. The application supports several mailboxes that can be configured independently, thus making the app suitable for users with many emails.
K-9 Mail has lots of features that make the software important. These features include new and improved OpenPGP support, flexible searching (recipient’s name can be searched using a nickname), more support for multiple windows, Storage Access Framework for export of settings, message listing, and emoji support. K-9 Mail is an open-source program that functions well with almost all email providers.
To download K-9 Mail, go to the Google Play Store and search for the app. Click on download and allow the app to complete the download. Once downloaded, open the app and tap “next” to move to the next screen. On the “set up a new account” that appears, fill in the email address and password. Click on IMAP on the “account type” feature. Set the server settings for received emails. Click on “next” to proceed. Set the server setting for sent emails. Again, tap “next” to proceed. Select synchronization and notifications settings and click on “next” thereafter. Input the account name, and personal name. Click on “done”. The K-9 mail app is now installed and ready for use.

K-9 Mail’s advantage lies in the app’s ability to handle several email accounts at once and easily. Other advantages include being an open-source email platform and an easy set up of accounts and the use of the app. Also, the app is designed to support PGP encryptions and is free.
On the downside, K-9 Mail is restricted to mails only. The app is designed primarily as an email management platform rather than a privacy app.
As previously stated, K-9 Mail is open-source and completely free of charge.
K-9 Mail provides an intuitive email service that is secure and safe. The app supports secure login to users’ email servers and in the main email. The app deploys two authentication methods, namely client-side TL certificates and CRAM-MD5 encryption. The email platform also supports MIME/PGP encryption through an open API that can be applied by users when encrypting or decrypting emails.
9. Resilio Sync
Resilio Sync (BitTorrent sync) is a closed-source tool for peer-to-peer file synchronization. This tool is available on Android, as well as Linux, Mac, and a few other operating systems. Resilio has a universal system for file delivery, which provides enterprises with a path to optimize IT and reduce the cost of enterprise-wide services such as file distribution, collection, and synchronization.
Although Resilio was not created to replace cloud-based file synchronization, this tool has functioned in this regard and is now famed for providing these services. This is because Resilio has been able to take care of the problems that existing services face, concerning storage limits, cost, performance, and privacy. In addition to file synchronization, Resilio also provides end-to-end data protection and security.
Resilio provides users with a host of features that have made the tool of great importance. Firstly, users are provided with a great tool for P2P file synchronization. Users can synchronize files over multiple systems, providing access to the files from anywhere while also avoiding the cost of cloud-based services. Resilio also allows for files to be sent to friends without having to create a permanent sync connection. This feature can only be enjoyed by Pro users though, while any user can receive files with the tool.
Resilio also gives users the ability to restrict access permissions on files according to desires. Users can change ownership of files, revoke ownership, or change read and write permissions at any time. Resilio also allows users to back up files automatically on multiple devices and create a disaster recovery site. This prevents the loss of valuable and important files in the case of a crashed or stolen device.
Resilio is best downloaded from the official website of Resilio Sync, resilio.com, or directly from the Google Play Store. The installation of this tool occurs automatically immediately after download. Resilio can also be downloaded from several browsers, by just typing in “Resilio Sync download”. The download can then be performed from a host of results that are displayed on the search.

Resilio, with many features and importance, also has a few pros and cons. On the bright side, the app is a fast and secure means of file sharing and synchronization. The tool also allows for unlimited storage and file sizes. Users are allowed to sync just the files that are needed, and are allowed to set the bandwidth usage for the syncing of files. This allows syncing across devices only when it’s suitable for the users.
One major disadvantage of Resilio Sync is the lag time between when a file is dropped and when the file gets synchronized across devices.
Resilio sync has a free subscription plan. However, the features are restricted in this plan. The tool has 3 paid Pro versions: The “Sync Home”, “Sync family”, and “Sync business”, pegged at $59.99, $99.99, and $30 per month, respectively. These paid plans give the user more features to enjoy in their subscriptions.
As previously mentioned, Resilio offers end-to-end data protection, giving users a safe and secure means of transferring files across devices with optimal privacy. The data that is shared or synced is usually encrypted, making it impossible for a third party to have access to this data.
10. Simple Mobile Tools
Simple Mobile tools are a group of completely free, ad-free, and open-source apps. Mobile phone users are usually faced with the problem of large apps, weighing tens to hundreds of MBs cluttering and slowing down the performance of mobile devices. This tool provides a very good option for the download of lightweight alternatives for these android apps, that can be used on less-capable devices, to help alleviate this issue.
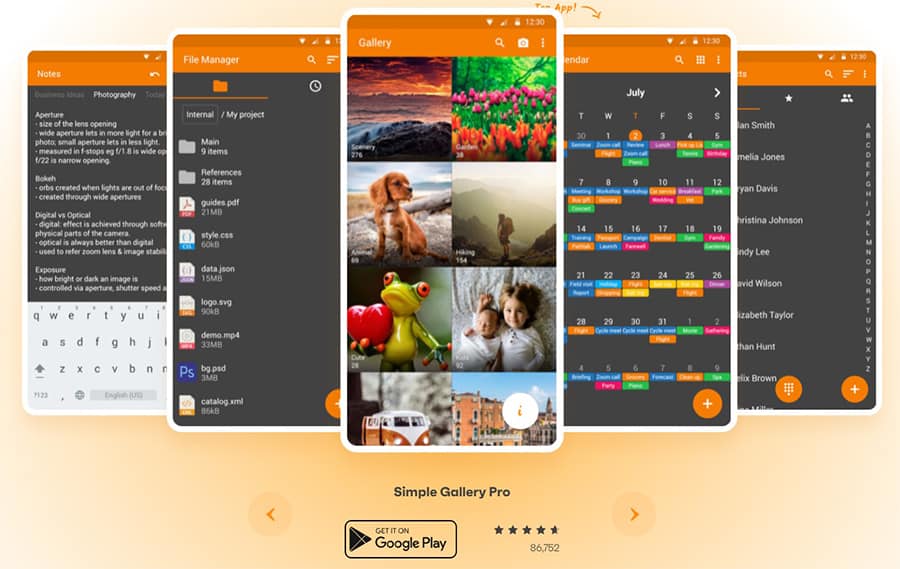
The major function of this tool is that Android users are provided with a collection of lightweight apps that can be used on phones that are not able to handle heavy apps without causing problems on the phones. The tool contains a host of lightweight alternatives to some everyday apps that are used by mobile phone users.
Seeing as not all android phones produced today can easily handle “big apps”, Simple Mobile Tools helps to solve one major problem a host of mobile phone users face. That is by providing a solution to large mobile apps cluttering the mobile phones of users, and slowing down user experience, by providing simple, open-source, ad-free, and lightweight apps for the less capable phones. This is the major selling point of Simple mobile tools.
These apps can be downloaded from the Google Play Store by just typing in “simple mobile tools” in the search bar of the app. The simple mobile apps are displayed, and the user can then choose the particular apps they wish to download.
Providing mobile phone users with lightweight apps for mobile devices that are “not very capable”, forms the major advantage of simple mobile tools. Other advantages include the fact that the apps included in the tool are free and downloadable at no cost. The apps are also ad-free, thereby eradicating the frustration that arises from ad pop-ups when using the apps. The tool is also free from unnecessary permissions and allows for customizable widgets. Simple Mobile Tools is also very easy to use.
One disadvantage of simple mobile tools is that the apps, being light-weighted, do not have the extra features that can be found in the heavyweight versions. As such, users of these simple apps are not able to enjoy these features.
There are Pro versions of Simple Mobile Tools that come at the very affordable price of $2.
Simple Mobile Tools is ad-free, and as such, can protect the user against adware, spyware, and other forms of malware that are usually associated with ad pop-ups during browsing. User information is therefore safe from the acts and intentions of malicious developers.
11. Musicolet
Musicolet is an offline lightweight music app that can be used on Android mobile devices. This means that the app does not possess streaming features, and can only play songs from the local storage of the phone. The app comes in the very small size of 5.1MB and is packed with many pleasant features.
Being an offline music player, the app can be used to play songs from the local storage of an Android device. This forms the major function of this lightweight app. One other major function of this app is that lyrics of songs can be added and displayed, even without an internet connection.
Because of the very many features that the app possesses, despite its small size, Musicolet ranks high in importance. Some of these features include the ability to play multiple queues of songs, a very powerful equalizer, and customizable notifications. The app also allows songs to be shared and renamed directly from the app, a feature that cannot be found in most music players. These features and many more have given the app a high level of importance relative to other music players.
The Musicolet app is very easy to download. The app can be found on the Google Play Store or other app stores. To download the app, head on the relevant App Store for your device and search for Musicolet. Once found, click on the app and select download to begin the process. Next open the app to launch by following the detailed guide on the screen. The app can then be enjoyed by the mobile phone user.

This interesting music app possesses a lot of advantages, for example, the app can function on Android versions from 2.4 upwards. The app has an elegant and very beautiful interface and the possibility to improve the music experience with the equalizer feature. The music privacy tool for Android has a small size, requires no internet connection, and as such, is ad-free. Music files are also conveniently grouped into folders and can be sent and renamed directly from the app.
One disadvantage of Musicolet is that music cannot be streamed online. Only songs found in the local storage of the Android device can be played. Also, the app is only compatible with Android devices. This means that the music player cannot be used with other operating systems other than the android OS.
The app is completely free of charge and does not require any additional costs during or after download.
Being an offline music player and consequently an ad-free one, this music app offers users maximum protection against various forms of malware that are associated with ads and the internet. Thereby, offering users maximum privacy in the usage of the app.
12. Bouncer
Bouncer is an app that allows android users to control the permissions granted to other apps on their device. . Users can approve permission for a short while using the Bouncer app and the app will automatically cancel those permissions later on.
The main function of Bouncer Temporal App Permissions is to grant temporary permission to apps. This security app has an accessibility service that is usually granted by Android users, with the option of removing this service. When an app is closed on the user’s phone, Bouncer accesses the phone’s settings and turns off the permissions that have formerly been granted to a specific app. This feature gives users complete control over the permissions granted to apps.
Bouncer’s temporal app permission is important in many ways. The app allows users to approve permissions for only a short period, after which the permission is automatically revoked by the app. This service provided by the app guards against privacy invasion by third-party apps.
Again, this app is very easy to download. Bouncer can be downloaded on any app store such as the Google Play Store. The app can also be downloaded directly from the official site of Bouncer. However, users should beware of fraudulent sites that can allow one or more forms of malware to be downloaded into the user’s phone. Once downloaded, the app is automatically installed on the phone. Once downloaded, follow the setup guide to begin use.

Some advantages of the bouncer app include: increased security and the lack of permissions needed to use the app. This is because the app does not require any form of internet connection. As such, the user is free from all forms of malware that can be downloaded from the internet. Bouncer also improves the battery life of the phone, as app permissions that reduce battery longevity are turned off immediately after the app is exited.
Some disadvantages of the app are the confusing logs and a slightly complicated interface. Also, the app has no help guide.
Bouncer is not free of charge. The app is sold on the Google Play Store for $1.88.
Bouncer Temporal App Permission provides Android users with maximum security for android devices. First, because the app does not require internet service, there are no chances of malware invasion. Also, the temporal app permission tool terminates permissions granted to other apps, once the app is exited. This prevents third-party apps from invading the privacy of the user.
What are the Vulnerabilities of Android in terms of Privacy?
Android devices are often targeted by hackers. This happens because the operating system of Android powers too many mobile devices. And because of how well known the operating system of Android is, cybercriminals and hackers are more attracted to the device. This makes Android devices more vulnerable to viruses, malware, and other attacks.
Android devices face many common attacks including phishing attacks, spyware, data leakage, unsecured wi-fi, broken cryptography, malware, stalkware, adware, and lots more.
However, these attacks can be prevented or eliminated. To do so, users will have to avoid downloading from third-party sites, pay attention to permissions, stay up to date with the latest operating systems, avoid using free wireless networks and protect the device with a VPN or other security tools.
Why is Privacy Important for Android?
Mobile devices including Android devices can store a large amount of sensitive information. Thus, it is important to take measures to protect the data from threats such as malware, spyware, stalkware, adware, and so on. Having privacy measures will also protect the device from theft and loss.What are the Common Threats for Android Mobiles?
The common threats for Android mobiles include:
- Data Leakage through Malicious Apps: This occurs when hackers redesign unprotected mobile apps into a malicious app designed to steal data, get backend information, digital wallets, and other details from the app.
- Social engineering: Social engineering attacks occur when text messages (smishing attacks) and emails (phishing attacks) are sent to people in a bid to inject malware into users’ devices or have people hand over personal information such as passwords.
- Unprotected Public Wi-Fi: Generally, public wireless connections are less secure than private networks. With a public network, there’s no way to detect who set up the network, who monitors the network or whether or not the connection is encrypted. And with many people using the network, public wireless connection poses a great threat to Android mobile devices.
- Spyware: Spyware is used to snoop and gather user data; this is often introduced through malicious ads (malvertisement).
- Outdated operating systems: Like other security initiatives, android requires constant work to discover and fix all vulnerabilities. When the OS isn’t updated, hackers can gain entry into a user’s data and system.
- Poor password habits: Poor password habits such as the use of a name, date of birth, age, and other easy passwords can pose a threat to android mobiles. Hackers can easily crack these passwords and carry out malicious intentions.

Can Someone Track My Android Phone without My Permission?
Yes, mobile devices including IOS and Android phones can be tracked without the user’s permission. This is usually done through spyware. The best phone trackers pose a serious threat to Android devices as the malware collects, uses, and spreads a user’s sensitive and personal information without the user’s permission, knowledge, or consent.
What are the Things to Consider While Using an Android Phone?
Some of the security tips to consider when using an Android phone include:
- Upgrade Android to 3.0 and above
- Do not download apps from unknown sources
- Install an anti-malware app
- Never connect to an unknown and unsecured public wi-fi
- Store all sensitive information behind an extra layer of encryption
- Download a remote lock/wipe app
- Use Chrome browser
- Beware of SMS threats
- Have a lock on the phone’s home screen
This is important:
A few care tips can make all the difference when it comes to securing an Android phone. One of the best lines of defense is to lock the screen using a PIN or passcode but not swipe or pattern. Also, create unique login details for all online accounts and ensure the two-factor authentication is turned on for these accounts.Also, turn on the automatic software update, this ensures the device is always up to date and eliminates any bugs. Check for stalkware and watch out for the signs, usually hot phones and batteries that drain quickly. Ensure to use a VPN, this creates an encrypted connection between the android device and a remote server. VPNs prevent Internet Service Providers (ISPs) from having full knowledge or storing a user’s browsing history. Furthermore, change default apps and ensure all data, sensitive information, and apps are encrypted.
Does Using a VPN on Android Help You Make Your Device more Private?
Yes, using a VPN on Android helps to make the device more private. This is because a VPN encrypts the data leaving an internet-linked device, thereby making the network connection seem like a private one even when connected to a public network.

VPNs have many benefits. For starters, a VPN helps to bypass geo-restrictions and provides safety and security through anonymity. The best VPNs for privacy prevent internet browsers and hackers from accessing connections and help to secure information sent and received. Also, some VPNs offer 256-bit military-grade encryption to secure data and prevent hacks.
Besides, VPNs secure public wireless connections, prevent ISP tracking, and provide security for online shopping and banking. Most VPNs feature advanced security features such as kill switch, DNS servers, OpenVPN, and other protocols, IPv6 leak protection, no log policies and more to ensure safety and security of user’s phone and data.
How do I Know if My Android Phone has a Virus that destroys Privacy?
There are signs to show if an Android device has a virus that can destroy privacy.
- Recognizing method: An Android phone is likely to have a virus if the phone is very slow, apps take a longer time to load and the battery drains faster than normal. Also, an Android phone with lots of pop-up ads and unexpected data usage is likely to be infected with a virus. Other signs include having apps that weren’t downloaded on the phone, and regular phone crashes.
- Scanning method: To scan an Android device for security threats, a virus scan program can be used. A smart manager application can also be used. To scan for threats, head on to settings on the phone. Next, locate security and select verify apps.
- Removing method: There are several ways to remove a virus from an Android device. One of the ways to do that is to download an antivirus, and enable the antivirus to scan and remove the virus. Cleaning up the device’s browser can help remove the virus too. Also, cleaning up file download, doing a full factory reset, and cleaning up apps on the device can help eliminate viruses. Above all, downloading from trusted sources and taking several other preventive measures will ensure the virus does not get reintroduced into the device.
Note:
True to the virus definition, a virus can cause several errors and damage to mobile devices. Viruses slow down the performance of the mobile device, causes unexplained data loss, and reoccurring system crashes. Viruses also cause erratic device behavior.What is the Difference between Android and iPhone in terms of Privacy?

IOS is a more secure mobile device than Android. This is because IOS keenly inspects all the apps on the Apple Store. While this means reduced availability of apps, this helps to reduce the number of malware-infected apps on the app store. Android, on the other hand has an open Play Store marketplace with tons of apps to choose from. However, because there are so many apps, there is a greater chance that hackers can distribute malware through the apps.
Furthermore, Android enables users to change their settings to download apps from other app stores. Although this provides a wider range of apps to choose from, the setting exposes users to a greater risk of malware.
Consistently updating the operating systems of both android and IOS is a guaranteed way of securing Google and Apple devices. Since Apple has firm control over the apps available, the creation and distribution of updates are easily achievable. Because of this, Apple offers IOS device updates for a longer time. This isn’t possible with Android devices. The sheer number of Android devices serviced by Google makes regular updates almost impossible. And since the updates have to be distributed across several devices and platforms, updates are less frequent than with Google. An Android vs iOS security comparison reveals strengths and weaknesses on both sides. In practical use there is little difference between the operating systems and other factors are likely more important when choosing between purchasing an Apple or Android device.

