Spyware is software that enables a user to obtain private information about another’s system activities by transmitting information covertly from their hard drive. It is specially designed to enter the system, gather information about its user, and forward it to a third party without the user’s consent. Spyware can also refer to legal software that monitors data for commercial purposes like advertising. Spyware can be used to steal private information such as account passwords and credit card numbers, resulting in identity theft and fraud.
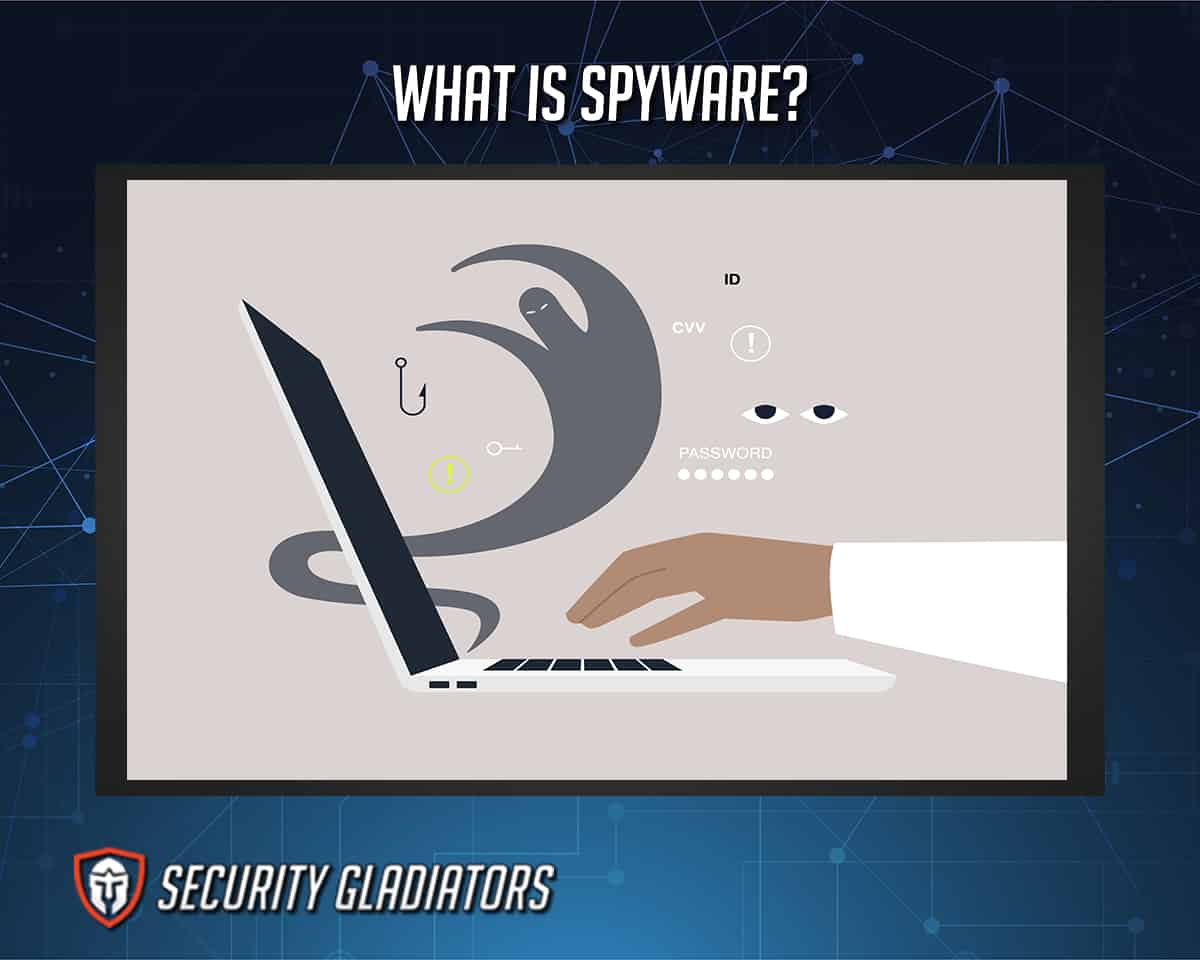
Table of Contents
What Is the History of Spyware?

The word “spyware” was used for the first time in October 1995. It popped up on a distributed internet discussion system in which users post email-like messages in an article aimed at Microsoft’s business model. Spyware is often referred to as snoop equipment such as tiny, hidden cameras. It re-appeared in a press release for a personal firewall product in early 2000, marking the beginning of the modern usage of the word.
In 1999, Steve Gibson of Gibson Research detected ads software on his system and suspected it was actually stealing his private information. The so-called adware had been secretly installed and was challenging to remove, so he decided to counter-attack and develop the first-ever anti-spyware solution.
Note:
As with other forms of malicious apps, spyware has enjoyed a rapid evolution since its humble beginnings. Primarily, this may be attributed to the proliferation of sites, portals, file-sharing resources and torrents. These tools allow users to exchange files and avoid using official software distributors and app stores to download free software as well as stolen versions of commercial packages.
Spyware authors have been known to pay the shareware developers to bundle their tracking software with legal packages. They may also re-engineer freeware apps to include their own spyware code. Spyware works perfectly when the target is unaware of its presence or activities. Therefore, today’s spyware practitioners take considerable pains to ensure that victims have no idea that the software package they are installing comes bundled with spyware.
Once established on a host system, spyware may observe a user’s activities and offer its controllers a steady stream of information. This could include private data, contact lists, financial information, account and user credentials, intellectual property or operational data essential to businesses. In some cases, the tracking software may also change a system to make its work simpler or as a form of sabotage.
What Does Spyware Do?

All spyware peeks into your information and all your system activity, whether authorized or not. Although, many trusted computer services and applications use spyware-like tracking tools. Malicious spyware is a type of malware installed explicitly without your informed consent. Spyware will infiltrate via an install package, malicious site or file attachment on your devices. Spyware will also monitor, capture and send stolen data to the spyware author.
In short, spyware communicates your private, confidential information to an attacker. The personal information gathered might be reported about your online browsing activities, but spyware code can also be customized to record specific activities.
How Does Spyware Infect Devices?

Malicious spyware needs to cover itself carefully to install and operate unnoticed. Therefore, the method of infection is usually obscured within seemingly regular sites or downloads. This malware may be inside or alongside genuine software and sites via vulnerability exploits. Bundled software packages are a common delivery technique for spyware. In this case, the spyware attaches itself to some other program that is intentionally installed and downloaded.
Some bundled spyware installs subtly without warning. Victims unknowingly infect their devices when they are forced to agree to the whole software bundle to install the required program. Spyware can also get into your system through all the avenues that other malware takes, such as when the user visits compromised sites or opens a malicious attachment in an email.
What Are the Steps of Spyware Infection?
Spyware is a form of a virus that is installed explicitly without your consent. Spyware will take the following actions on your devices:
1. Infiltrate
Spyware infiltrates a user’s device via an app install package, malicious site or file attachment. For example, a user can get spyware by opening an infected email attachment or clicking on a link to a malicious website. Cyber attackers install spyware by exploiting a software vulnerability or through unauthorized access.
2. Monitor and Capture Data

Spyware can monitor and capture data via keystrokes, tracking codes and screen captures. Spyware allows websites to remember individuals, their website login details, their shopping carts and more. Sometimes, spyware is used as a legal surveillance tool by employers. However, in the hands of cybercriminals, it is purely malicious.
3. Send Stolen Data
Spyware can send captured data to its author to be used directly or sold to other third parties. For example, if you have visited any malicious website, spyware on your device can monitor and capture your login and banking details and sell all the captured data to third parties.
What Are the Types of Spyware?
Spyware has uses beyond secretly monitoring and storing its target’s online activities and capturing critical information. Some strains can force unwanted pop-up ads into a user’s online browsing experience or covertly overtax the processor in their devices. Others are used to create traffic for sites. Some of the most common types of spyware are mentioned below:
Trojan

A Trojan is a type of spyware that is often disguised as harmless software. Trojans can be used by hackers trying to gain access to user’s systems. Users are typically trapped by some form of social engineering into loading and executing Trojans on their devices. Once activated, Trojans can enable hackers to spy on a victim, steal their private information and gain backdoor access to their device.
The word “Trojan” originates from the ancient Greek story about the Trojan horse, which was presented as a gift to the Trojans who were later killed by the Greeks hiding inside. A Trojan hides within seemingly harmless programs or tries to trick users into downloading it. The name was coined in a 1974 USAF report which speculated on imaginary ways computers could be compromised. A Trojan spreads by pretending to be helpful software or content while covertly containing malicious instructions. It is more practical to think of a Trojan as an umbrella term for malware delivery that cyber thieves use for various threats.
A Trojan must be executed by its victims to do its work. Trojan can infect devices in a variety of ways, such as:
- A user falls victim to an attack by opening an infected email attachment or clicking on a link to a malicious site.
- A user visits a malicious site and experiences a drive-by download pretending to be useful software.
- A user downloads software whose publisher is unknown from unreliable access.
- Hackers install a Trojan by exploiting a software vulnerability or through unauthorized access.

Trojans are not problems only for laptops and desktop computers. They can impact your mobile devices, including tablets and cell phones. Usually, a Trojan comes attached to what looks like a legitimate program. In fact, it is a fake version of the application that is loaded up with malware. Hackers will usually place them on unofficial and pirated app markets for unsuspecting users to download. These applications can also steal private information from devices and generate revenue by sending premium SMS texts.
As is the case with protection against most common cybersecurity threats, effective cybersecurity should be the first line of protection. A combination of a complete antivirus shield and excellent cybersecurity hygiene is the best protection from Trojans. Below are some techniques to use to stay safe:
- Be aware of phishing threats.
- Be cautious about downloads.
- Update devices as soon as the updates are available.
- Do not visit unsafe sites.
Adware
Adware is often known as advertisement-supported software that generates revenue for developers by automatically generating ads on users’ devices, usually within a website browser. Adware is typically created for computers but can also be found on other devices. Some forms of adware are highly manipulative and create an open door for malicious programs.
Adware use began in 1995 when some market experts considered all adware to be spyware, which enables someone to collect confidential information from a user’s computer without the user’s knowledge. Adware usually comes in software downloaded from the internet and it secretly installs itself onto the system without the user’s knowledge.
- Adware developers and the distributing vendors make money from third parties via either pay per click, pay per view or pay per install.
Adware can also track internet activities to display ads that are more relevant to the user. Once the developer has the user’s location and internet browsing history, they can earn additional income by selling that information to third parties.

Different types of adware have different functionalities and behavior, ranging from bombarding users with ads to downloading plugins or applications without asking. Some adware functions like a man-in-the-middle attack, redirecting all of the device’s internet traffic through their system even over an HTTPS connection. This is especially disturbing when considering that this action could expose users’ online activities to the adware developer. In addition, the adware can eat up a device’s processing power. Downloading and running ads makes devices work extra hard, slowing them down. Users who get adware on their device can expect extra data charges from all the advertisements.
Adware removal will help fix adware issues like obnoxious pop-ups and hidden spyware. As with all kinds of spyware, prevention is easier than removal. To prevent the spread of adware, you can take several steps given below:
- An ad blocker will stop ads as you surf the internet, eliminating drive-by downloads from infected sites.
- Any ads providing you a free iPhone or something else that seems too good to be true is most likely a scam.
- Make sure to avoid illegal sites, especially if you are doing any online shopping.
- Depending on the browser you use, you should be able to stop third parties from installing things like toolbars without your consent.
Tracking Cookie Files
Tracking cookie files are essential to the modern internet but are also a vulnerability to online privacy. As a critical part of internet browsing, cookies help website developers provide more private, convenient site visits. Cookies let sites remember you, your site logins, shopping carts and more. Protecting your privacy can be overwhelming. Luckily, even a basic understanding of cookies can help to keep unwanted eyes off your browsing activity.

Cookies are text files with some information like a username and password to identify devices as they use an internet network. A tracking cookie is a sample of a text file dropped onto an internet browser while viewing a site. This text file collects information from a user, such as their activity on a site, browsing activity, geographic location, purchase trends and more. This way, websites can be personalized to the specific user. The sites can suggest content that might be especially relevant to the specific user and can monitor activity on the website, offering deep analytics on its use. This can enable site owners to optimize and enhance their websites.
Luckily, if you do not like the idea of cookies tracking your internet activity, you can disable them. You can configure your browser so that it will automatically disable third-parties tracking cookies. The directions to do this depend on the internet browser you are using. For example, if you are using Google Chrome, click the three dots on the upper right side of the internet browser. Next, click Settings. On the left side of the screen, you should see an option for Privacy and Security. Click it and then click the Cookies and Other Site Data option. Then choose to block third party cookies.
Modem Hijacker
Modem hijackers are one of the oldest types of spyware. A modem hijacker ties into your phone line to make unauthorized calls and access member sites through your connection. Generally, modem hijackers make calls to premium rate phone numbers and access malicious websites. Victims of modem hijackers do not know about the access and calls until the unauthorized charges show up on their phone bill.
If you use a telephone modem for your internet connection, a hacker may be able to install an online dialer on your system to establish a new internet connection that uses pricy 900-type long-distance phone numbers. These calls can come as quite a surprise when you get your next telephone bill. This dialer spyware often piggybacks on spam and porn emails; simply opening the email can inadvertently start the dialer installation. The victims would generally become aware of the issue when they saw their $1,000+ phone bill the following month.
Commercial Spyware

Commercial spyware is commonly marketed under the guise of parental control software which is legal to use. Commercial spyware is a somewhat new concept that has plagued various personal computers and business networks. Although, like most forms of technology, it can be misused. Spouses could monitor their partners, businesses could monitor their employees, hackers could install spyware onto an executive’s device and extract critical business information, etc.
Commercial spyware applications, also referred to as spy apps, are surveillance applications used to monitor, track and extract information from third-party mobile devices. Detecting commercial spyware on your device may be difficult. Some signs could include your battery draining quickly, your device turning off and on or spikes in your data usage.
This is important:
Before attempting to find or remove the commercial spyware, it is essential to consider safety and the possibility of collecting evidence. Many intruders use commercial spyware as a way to monitor and control their victims. Some may even increase their behavior if they feel that their victim is cutting off their access.Be careful if someone needs to update or fix something on your device and trust your instincts if you do not trust their intention. If someone did have access, consider if their access coincided with improved monitoring or stalking.
How Does Spyware Work?

Spyware is distributed in many ways. One of the most traditional ways is getting users to click on a link that leads to a malicious site. Those links can be in text messages, emails, pop-up windows in an internet browser, etc. Poisoned links have been known to appear in Google search results. Sometimes, a victim does not even need to click on a malicious link to get to an infected site. This is most generally done through an infected ad delivered to reliable sites through legal ad networks.
Spyware secretly infiltrates devices and starts to obtain critical information, such as login details, account credentials and internet activities. Internet spyware is secretive, so victims do not know of its existence until it takes over their device.
How Do You Get Spyware?
There are many ways for your device to be infiltrated. The most common ways are listed below:

Many applications pretend to be something else on the internet from unofficial sources. Once you download them, they can result in spyware applications getting into your device.
Not all pop-ups are risky, but some can be. Clicking and following the instructions on pop-ups may invite unwanted risks onto your device.
How to Recognize Spyware on a Device
Even if you cannot find the spyware, you may be able to detect signs of it. For example, if a computer starts to run more slowly, that could signify that it has been compromised. The common clues to recognize spyware on your device are:

- Slow response and increased sluggishness.
- Unexpected ad messages or pop-ups.
- New search engines, toolbars or internet home pages that you do not remember installing.
- Batteries are becoming depleted more rapidly than usual.
- Difficult logging into secure websites. For example, if your first login attempt fails and your second attempt succeeds, that may mean the first attempt was on a spoofed internet browser and the password was communicated to a third party.
- Strange increase in your data usage. This can be a sign that the spyware is searching your essential data and uploading that data to a third party.
- Anti-virus and other safety applications are not working.
Which Devices Are Vulnerable to Spyware?
The more innovative your home gets, the greater the spyware threat. Therefore, ensure that you take precautions with the hackable devices. Most of us are aware of spyware and many have been confronted with these viruses at one time or another. However, spyware can compromise more than just computers. Any electronic gadget that connects to the internet may be in danger, especially smartphones and tablets now that they are the most popular internet-connected devices. Some other at-risk devices are:

- Smart TVs
Hackers can access your smart TV from a remote location and use it to spy on you. Often the hackers just cause annoyances like turning the TV on and off, changing the channel or changing the volume setting. But sometimes this interference leads to more severe consequences such as spying on your household via a TV camera or accessing other devices connected to the same network.
- Baby monitors
Smart baby monitors can capture audio and video streams, monitor a baby’s movement and heart rates and trigger an alarm if there is an emergency. These capabilities are beneficial for new parents, but they can also expose you to security threats. For example, hackers can speak to family members by using the device or stream live audio and video from your home.
- Garage door openers
Smart garage door openers enable you to control the door functions remotely. Unfortunately, these devices also allow hackers to remotely control your garage door and find out when you leave for work.
- Home Wi-Fi routers
Unwanted access to your Wi-Fi router can lead to harsh consequences. Depending on what type of smart devices are connected to it, the damage can range from accessing your Google account and tracking your activities to stealing your identity.
Examples of Problems Caused by Spyware
Spyware can be extremely dangerous if you have been infected. Threats can range from mild problems to long-term financial damage. Some of the most frequent problems caused by spyware are listed below:
- Data Theft and Identity Fraud: First and possibly most importantly, spyware can steal personal data that can be used for identity theft. If a malicious app has access to every piece of data on your device, it can collect more than enough information to copy your identity. Data used for this purpose includes email accounts, shopping history, internet browsing history, saved passwords for online banking and social networks. If you have visited any banking websites, spyware can copy your bank account details or credit card accounts and sell them to third parties.
- Computer Damages: Spyware can be poorly designed, leading to low system performance. The lack of performance optimization can take up a massive amount of your computer’s memory, internet bandwidth and processing power. As a result, infected computers may run slowly and lag in between apps or while online. Worse cases include frequent computer system crashes or overheating issues which can cause permanent damage. Some spyware can even disable your cybersecurity programs.
- Disruptions to Your Browsing Experience: Spyware can control search engine results and deliver unnecessary search results in your internet browser, leading to harmful sites. Spyware can also cause your homepage to change and can alter some of your device settings. Pop-up ads are an equally irritating problem that accompanies some types of spyware.
How to Remove Spyware?

If your device appears unusually slow and crashes a lot or your internet browser becomes overpopulated with pop-up windows, your efforts to avoid spyware might have failed. That means you will need to remove the infection. Removing any type of virus manually is difficult, but it can be even more so with spyware. Spyware developers often name their files to copy the names of actual system files to mask their identity.
There are many network security programs available on the market that can detect and remove spyware. They include Malwarebytes, Avast Antivirus, Adware, Trend Micro, SpywareBlaster and Spybot Search & Destroy.
Pro Tip:
Spyware on mobile phones can cause symptoms similar to computers, such as regular system crashes and performance breaks, but there are other symptoms too. For example, your mobile phone may start turning itself off and not reacting immediately when you try to turn it back on. Other symptoms include faster battery reduction than usual and strange text messages in your inbox. If you feel you have spyware on your mobile phone, you can back up all your data and reset it to its factory settings. As with computers, many security programs can be used to scan a mobile phone for spyware and remove it, even though that solution may not be effective in every case.What Are the Tools to Remove Spyware?
Anti-spyware tools detect and remove malicious spyware to protect your device. These tools can be used to protect your private information and allow you to browse the internet safely. The best spyware removers are:
- TotalAV

TotalAV is a free spyware removal software that provides complete security for all your household devices in one simple desktop and mobile phone application. It also offers real-time anti-malware, anti-ransomware, anti-spyware and anti-adware protection.
- Real-time protection
- Provides a highly secured password vault
- Removes viruses, spyware and Trojans
- Windows, iOS and Android supported
- Avira
Avira is an all-in-one security tool for Android, iOS, macOS and Windows that keeps your devices free of spyware. It is powered by a smart scan to scan your devices for unsecured networks, vulnerabilities, threats and performance optimizations.
- Password manager
- Internet browser tracking blocker and ad blocker
- Junk file cleaner
- Award-winning antivirus scanner
- Avast Free Antivirus

Avast Free Antivirus is a tool that can protect your device against viruses and other threats. This tool can check everything from passwords to internet security.
- You can efficiently perform a regular scan to detect threats and vulnerabilities
- It can easily detect malicious software before you install it
- Avast Free Antivirus is best for anti-spyware
- Bitdefender Total Security

Bitdefender is another excellent antivirus tool that offers an on-demand and on-install scan facility. It helps you to keep your devices safe from many threats. The program takes care of your online privacy and personal data.
- Enables you to remotely trace Android devices in the case of loss or theft
- Verifies whether your email account has been breached or not
- Offers 24/7 security updates
- Reacts immediately to threats without compromising the performance of your device
- 360 Total Security
360 Total Security is a perfect tool that cleans your system of any dangerous files or viruses. This spyware detector tool offers real-time protection against external threats. 360 Total Security uses cloud technology to detect different variants of ransomware in real-time.
- Offers protection from spyware and malware
- Protects your online privacy
- Optimizes your network performance
- Keeps your system protected from malware, phishing attacks and other malware attacks
How to Protect Your Phone from Spyware

- Stay away from unauthorized app stores. Third-party app stores can carry various malicious spyware applications. Avoid downloading from these stores to reduce your risk of infection.
- Only download authorized apps from trusted app publishers. Some spyware hides as companion services to other popular applications like Gmail and Facebook. Always read the author’s name and verify if they are trusted or an unknown third party.
- Be careful about giving permissions to applications. Some applications have no apparent need for camera or location access. Decide whether the application needs this permission to provide you an ideal user experience.
- Do not follow links in text messages. A popular technique for mobile attackers is to include links in texts to their targets. You will be safer by avoiding any links and manually entering URLs into the address bar.
Is Spyware Different from Viruses?
Yes, spyware is a specific type of unauthorized software that secretly collects your personal information. A virus is a specific type of application that can be privately distributed, often by email. Both viruses and spyware can cause damage to your device or cause you to lose important information.
| Spyware | Virus |
|---|---|
| Spyware is a form of malware specifically designed to collect your private data. | A virus is a harmful executable file attached to another piece of executable code which can be dangerous. |
| The primary objective of spyware is to monitor the activity of the system. | The primary objective of a virus is to modify data. |
| Spyware can be detected and removed by anti-spyware software. | Antivirus software is used for protection against viruses. |
| It is less dangerous than a virus. | It is more dangerous than spyware. |
What Are the Most Popular Spyware Threats?
The 10 most popular spyware threats are mentioned below:

- CoolWebSearch
CoolWebSearch may hijack web searches, home pages and internet browser settings. CoolWebSearch installs using malicious HTML apps or security flaws such as exploits in the HTML help format.
- Gator
Gator is another spyware threat that may display banner advertisements based on a user’s web surfing habits.
- 180search Assistant
180search Assistant is adware that delivers targeted pop-up ads to a user’s device. Whenever a keyword is entered into an internet browser or a target site is visited, 180search Assistant opens a separate internet browser window displaying an advertiser’s website page that is related to the keyword.
- Transponder
Transponder is an internet browser helper object that monitors requested website pages and data entered into online forms, then delivers targeted ads.
- Internet Optimizer
Internet Optimizer hijacks error pages and redirects them to its own controlling server.
- BlazeFind
BlazeFind may hijack website searches, home pages and other internet browser settings. It may also redirect website searches through its own search engine.
- Advanced Keylogger
Advanced Keylogger is a spyware threat that can monitor keystrokes and capture screenshots.
- TIBS Dialer
TIBS Dialer is a dialer that hijacks a user’s modem and dials toll numbers that access restricted websites.
- Hot as Hell
Hot as Hell is a spyware program that dials toll numbers to access paid pornographic websites. It may disconnect a user’s system from a local internet provider and reconnect it using an international phone number.
- ISTbar
ISTbar is a spyware tool used to search restricted sites that may display pornographic pop-ups.

