Two-factor authentication is already widely adopted for some products. For example, Google made 2FA mandatory for over 150 million users to access their accounts, an action that led to an astonishing 50% decline in compromised accounts. The adoption of 2FA is essential for organizations that wish to improve their operational security. From a risk management perspective, one of the major concerns with organizations is the possibility of hacking. While having strong passwords is certainly a good step, there is still a chance for phishing attacks and keyloggers to retrieve these. Two-factor authentication reduces this risk for organizations.

There are a number of different 2FA applications available, so it is important to choose one that is right for you. Some of the factors that determine a good 2FA application include compatibility with various devices, the trustworthiness of the 2FA provider, as well as ease of use in setup and in practice.
The 3 best 2FA apps for 2023 are listed below.
- Google Authenticator
- Authy
- Microsoft Authenticator
Table of Contents
What is Two-Factor Authentication (2FA)?
Two-factor authentication or 2FA is a process that aims to solve the pitfalls of basic password user authentication. Instead of relying on just a password for logging into a website or service, the authentication step will require the user to prove that they are in fact the actual user attached to the account. This step requires the user to provide another piece of information that only they know which is most commonly a one-time code that is generated by a secondary device owned by the user. One-time passcodes ensure that users must use a new password each time they log in, making it almost impossible for anyone to gain access to their account. Most of these one-time passcodes use a computer algorithm that uses the current time as a source of uniqueness. Because the passcodes are generated based on the current time, platforms are able to filter out passcodes that have already expired. Due to the short window of validity, attackers will be less likely to penetrate the user’s account since it requires real-time input.
The Best 7 2FA Apps of 2023
The following sections will enumerate our top picks for the best 2FA apps to download in 2023. We will go over the key features of each application as well as the advances and disadvantages. Each section will also cover the compatibility and price of the given 2FA app.
1. Google Authenticator
Everyone is familiar with Google. The search engine giant has also made a name for itself as a provider for essential office and productivity tools. It simply makes sense that the company also provides its very own 2FA application known as the Google Authenticator. The product was first released in 2010 and continues to be widely available and supported today.
The Google Authenticator generates a six to eight-digit one-time password that must be entered when logging into a website that supports the Authenticator. The app is available for both iOS and Android devices through the App Store or Google Play Store. The app makes it incredibly easy to set up 2FA for websites that support the Google Authenticator. Users can quickly use their mobile devices to scan a QR code to add a new account. The app also has a multi-device sync feature which allows you to use the same token in multiple devices.
A disadvantage of the app is that it does not support a backup option. Losing access to your phone may lock you out of your account in some cases.
2. Authy
Authy is a two-factor authentication that is compatible with mobile devices and desktop computers. Authy is a product by Twilio, a San Francisco-based tech company that specializes in web services for communication channels. The Authy app allows you to access your tokens from any device you want. The application is available on both the App Store and Google Play store. Authy also offers a Chrome application for accessing tokens.
Mobile users can also take advantage of TouchID, PIN protection, and password login to add further security. Authy also makes it easy to create a backup of your account. This backup feature will be helpful in case the user loses their phone. However, this option is not selected by default. Users will have to opt-in to this feature to ensure a backup exists.
The application also provides device management options that allow you to control which devices can receive codes. The app also works offline. This makes it possible to log in to websites without having your phone connected to the internet. The Authy app is also completely free to use, making it a great option for personal use. One possible disadvantage of Authy is that the code base itself is proprietary and closed-source. This makes it difficult for a third party to audit the code to see if there are any security issues within the service.
3. Microsoft Authenticator
Microsoft Authenticator is a two-factor authentication app for Android, iOS, and Windows Phones. The app generates time-based one-time passcodes (TOTP) and push notifications for Microsoft accounts and apps. It’s used as an additional layer of security on top of your password.
The app works by first scanning a QR code from the website or service that requires 2FA. This will create a new account that will be where you will find new one-time passwords whenever you need to log in to the website or service. The Microsoft Authenticator has the advantage of being a great way to quickly log in to a Microsoft account securely from your phone. Besides Microsoft services, the app can also be used for other services. Microsoft Authenticator, like the previously mentioned Authy and Google Authenticator, is completely free. You are able to create and link as many accounts as you want without any additional fee.
One disadvantage of Microsoft Authenticator is that it does not have a backup option. This means that if you lose access to your phone, you may not be able to log in to your account. Another disadvantage is that there is no desktop option to access your one-time password.
4. andOTP
andOTP is an open-source two-factor authentication app for Android that offers time-based one-time passcodes (TOTP). AndOTP is free and open-source software released under the GPLv3 license. Some key features include multiple backup options, encrypted storage, and a sleek minimalist design.
The app also requires minimal permissions. Camera access is needed for scanning QR codes and storage access is optional if the user decides to import and export data. While the app is still available in the Google Play Store, the main developer stated in June of 2022 that the code would no longer be maintained. However, this may change sometime in the future.
The main disadvantage of AndOTP is that it is only compatible with Android devices. According to the GitHub page, the app is compatible with Android 5.1+ devices. Since the app is open-source, andOTP will remain free to use for all users.
5. Duo
Duo Security is a tech company that provides two-factor authentication for businesses and organizations. Duo provides a 2FA solution with their Duo Mobile application. The application uses a single-tap user-friendly interface to allow users to verify their identity using push notifications. Duo Mobile is also capable of generating time-based one-time passcodes to complete the two-factor authentication process. After set up, the user will be able to verify their identity to a particular platform or service using Duo Mobile.
Duo Mobile includes support for several authentication controls such as push notifications, passcodes, and even biometrics. The application also works for both iOS and Android devices. Duo Mobile is free for up to 10 users, which makes it an excellent choice for smaller teams. Larger teams can subscribe to the Duo MFA plan which costs $3 per user per month. This plan also comes with access control policies and Secure Single Sign-On support. One possible disadvantage of choosing Duo is that users who opt to use push notifications may find the feature sub-optimal with an unstable internet connection.
6. Aegis
Aegis is a free and open-source 2FA app for Android users. The Aegis application supports several ways to add new entries. For example, users can scan a QR code or provide an image of one. Users also have the option to import data from other authenticator apps such as Google Authenticator. Since Aegis is an open-source project, its code is available for anyone to review and audit. This makes it a secure option for your needs.
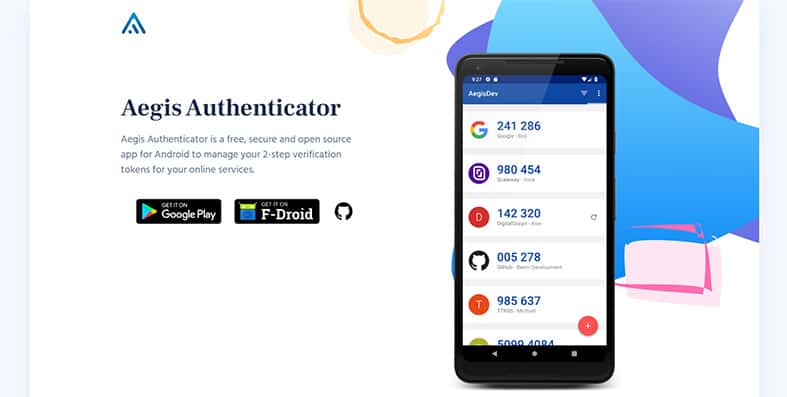
A key feature available in Aegis is the ability to set up automatic backups of the program’s vault. The user can select the location where the backups will be stored. Another useful feature is the ability to organize all the apps and services in your vault. Users have the option to set custom items and create custom groups for easier navigation. Users will also have the opportunity to export their tokens and send them to another device.
One disadvantage of Aegis is that it does not offer customer support due to being an open-source project. Aegis is also only available for Android systems. However, since the app is open-source, andOTP will remain free to use for all users.
7. 1Password Authenticator
1Password is a password management company that offers a variety of products to help users manage their passwords and other sensitive information. The 1Password program can save a QR code that a platform provides for setting up two-factor authentication. 1Password users can label the QR code as a one-time password.
An advantage of the 1Password app is that it can automatically fill in the one-time password for a given service. Another advantage of using 1Password is that it combines both password management and two-factor authentication in a single service. 1Password will even let you know if any services you are part of offer 2FA support.
The 1Password Authenticator app is compatible with both iOS and Android devices. It is also available as a web app. The app costs $2.99 per month or $29.99 per year. 1Password costs $2.99 per month for a single user. This plan comes with unlimited passwords and support for two-factor authentication as well. Users can also choose to avail the 1Password Families plan, which allows up to 5 family members to use the same service.
How to Use a 2FA App?
Users who want to use a 2FA app may be wondering how easy or how difficult it is to set up yourself. Because of the importance of 2FA applications in opsec for organizations, teams should find a 2FA solution that is easy to set up and use daily.
After following the instructions below, even non-technical users should be able to set up 2FA for a compatible account. In this guide, we will use Google Authenticator as an example.
- First, the user should download the 2FA application on their secondary device. Most 2FA applications are available in both the iOS App Store and Google Play Store.
- Next, open the platform or service you want to add 2-factor authentication to. Do note that not all platforms offer this feature. The user will likely find the option to enable 2-factor authentication through the service’s Settings menu.
- The service will typically display a QR code or 32-digit code during the set-up process.
- The user must use the downloaded 2FA application to scan the QR code.
- The service or platform will ask you to confirm with an authentication code that will be displayed on the 2FA app. Enter these details to finalize the setup procedure.
Note:
After setting up the new account, the user’s 2FA application should now have an entry that generates a new code for the desired service.What are the Benefits of Using a 2FA App?
Users might be wondering what the actual benefits are for using 2FA applications. First, the use of 2FA applications dramatically increases the user’s security. Because 2FA involves proving that the right person is logging in, there is a lower chance for hackers to gain access to sensitive data and private accounts. This is especially important when working in a corporate setting.
Second, users who opt to use two-factor authentication is less prone to fraud. Malicious actors will have a difficult time pretending to be a user within your team when logging into an account requires two-factor authentication. Enabling two-factor authentication for a particular platform will reduce the likelihood of both phishing attacks and brute force attacks.

Phishing attacks refer to a type of cybersecurity risk where a malicious actor pretends to be a reputable source. Most phishing attacks aim to retrieve the target’s user ID and password. However, with 2FA enabled, the malicious actor will be unable to use these login details on its own.
Brute force attacks, on the other hand, refer to a type of hacking method where the malicious actor submits many passwords in order to find the right password for a certain username or email. With two-factor authentication enabled, brute-force attacks become ineffective since a password alone will not be enough to log into the account.
The third reason why it is recommended to use a 2FA application is that it is often safer than SMS-based two-factor authentication. The use of SMS for authenticating logins is prone to vulnerabilities such as malware that is programmed to intercept text messages. Another benefit of using 2FA applications is to prevent breaches within a company. Enforcing a 2FA login when logging into an organization-owned system will prevent employees from accessing unauthorized data.
What is the Difference Between 2FA Apps and 2FA Hardware?
When it comes to two-factor authentication technology, there are two main types: 2FA applications and 2FA hardware. While 2FA applications use an app or program to generate the codes needed to log in, 2FA hardware relies on a dedicated physical device to store and generate codes.

One of the most popular examples of 2FA hardware is 2FA security keys. These devices come in the form of a flash drive that you can plug into your desktop or laptop. Security keys are more secure than 2FA applications since it requires criminals to physically steal your key. However, the added security comes with some disadvantages. For example, these keys cost money to buy and can also be misplaced. Additionally, setting up a security key may require more steps than the typical 2FA app process.
Which is the Strongest 2FA Method?
The strongest 2FA method is two-factor authentication through a hardware-based solution. This is because hardware devices eliminate the chances for hackers to obtain your codes through malicious software or through social engineering. Because logging into your account will require you to have the unique device on hand, it ensures that only the user can log in. However, as stated in the previous section, software-based 2FA solutions are still more convenient and accessible.

