
Businesses and individuals need to know what endpoint protection is and the type of solutions considered endpoint protection. While any endpoint protection program can offer resilience against new types of cyber threats, there are certain features that make certain endpoint protection solutions better than others. Some of those features include remote wipes, patch management, and data encryption, along with real-time threat detection and prevention. For the best possible endpoint protection solution, customers need to know how to choose the right endpoint protection solutions. Factors such as cost, available vendors, the needs of the organization, technical capabilities and others should be considered. Even after implementing a robust endpoint protection program, certain practices need to be followed in order to get maximum security.
Table of Contents
What Is Endpoint Protection?
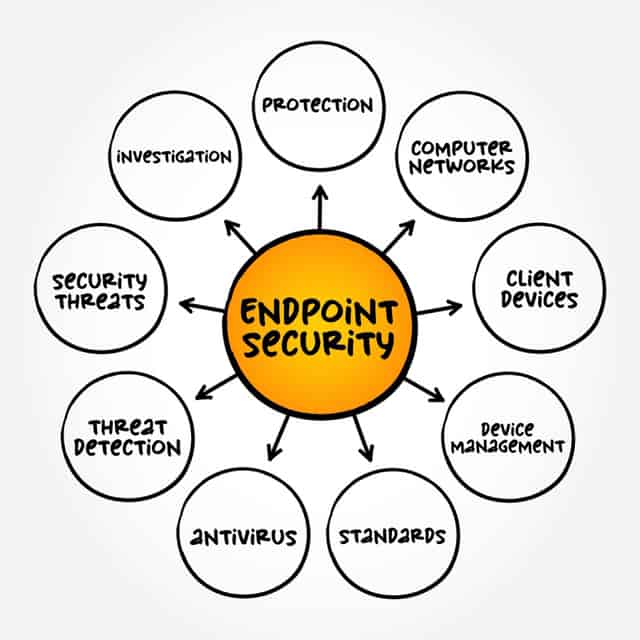
Endpoint protection encompasses all the services, tools and products that help form a cybersecurity solution for network endpoints. The most common endpoint protection tools and services include firewall products, web filters, email filters and antivirus products. Endpoint protection essentially protects all types of computing devices from cyber threats. Endpoints, if not managed well, can present cybercriminals with network entry points. Hackers with enough skills and resources can exploit such weak points. Endpoint protection makes sure cybercriminals do not have a way to infiltrate a network. Modern endpoint protection solutions protect items in the cloud as well. Endpoint protection is a lot more than an individual computing device with cybersecurity products. All types of actors such as organized gangs, hacktivists and countries play a part in attacking organizations big and small. Sometimes, the main cyber threat can arise from within an organization. Proper endpoint protection guards against insider threats as well.
What Is an Endpoint?
Endpoint refers to any computing device that exists on a network and forms an endpoint (physically). The most common types of endpoints are given below.
- Virtual environments
- Servers
- Tablets
- Smartphone devices
- Desktops
- Laptops
- Internet of Things (IoT) computing devices
- Printers
- Switches
- Medical devices
- Scanners
- Wearables
- All POS systems
What Are the Types of Endpoint Protection Solutions?
Modern endpoint protection solutions are a lot more diverse than the early days when protection meant securing one’s digital perimeter. Cybersecurity professionals can now configure security tools for endpoints that form a part of the organization’s IT environment instead of something that is simply applied after the fact. Any decent endpoint protection strategy must make use of many different solutions, with each one acting as a barrier for hackers. The types of endpoint protection solutions are given below.
Antivirus Software
Antivirus software is the tried and tested endpoint protection solution that still forms the bedrock of any cybersecurity plan. Antivirus products are not only popular but also very effective. Only antivirus solutions offer some of the most critical capabilities needed for complete endpoint protection. Such capabilities include anti-malware, anti-spyware and sometimes even anti-ransomware.
Any enterprise looking for reliable protection against signature-based viruses should invest in a decent antivirus solution. Though most cyberattacks today are not stopped by signature-based protection solutions, organizations can still benefit because of that one-off virus already present in the database. Modern antivirus solutions also offer advanced malware scanning tools that protect endpoints via a vast database that contains dossiers on various cyber threats. Directly installing antivirus software at endpoints offers more protection. Of course, for sufficient protection against advanced cyber threats, antivirus solutions are not enough.
Firewall
Firewalls represent another type of endpoint security solution. By inspecting all network traffic that enters and exits a device, firewalls can keep malicious traffic at bay. Modern firewall solutions also help in implementing security applications for specific applications, rather than the entire system. Sometimes, firewalls are used in addition to some network access control mechanisms. Network access control solutions can help with issues that arise with identity management and properly authorized access. Network access control also protects devices connected to network nodes. Some firewalls can also manage what users and devices can access and what infrastructure is available via the network. The functionality firewalls offer can be topped off with more data limitations for better endpoint security.
Endpoint Detection and Response (EDR)
EDR or endpoint detection and response is a modern cybersecurity tool for achieving more resilient endpoint security solutions. EDR offers capabilities such as detection and mitigation. In simpler terms, EDR security solutions monitor endpoint applications and files to look for malicious ones. The biggest advantage of using EDR in any endpoint security solution is visibility. EDR offers deep control on what’s happening behind the scenes with regard to an endpoint. EDR solutions offer good protection against modern cyber threats, such as ransomware and fileless malware. If there is one tool cybersecurity teams in different organizations can benefit from the most, that tool is EDR. Not just for identifying potential threats, but also for remedying any associated problems.
Mobile Device Management (MDM)
Corporate networks now have to deal with connections from a huge number of remote devices. UEM or unified endpoint management solutions address such communications. UEM is based on MDM or mobile device management functionalities. With MDM properly configured, remote devices can be managed and monitored with ease. Advanced MDM solutions can also protect laptops and desktops that have support for remote access. MDM offers security management policies all connected devices can follow. MDM can also help update policies, functions, apps and equipment. Some implementations also come with additional features, such as performance monitoring of apps and equipment. Not only that, but MDMs can also track device activity, ownership, status and current location. Depending on the vendor, MDM may also offer encryption tools for files and email messages.
What Are the Key Features of Endpoint Protection Solutions?
Without the right functionality, no amount of investment in endpoint protection solutions is going to offer sufficient safety. The best way to make sure an endpoint protection solution delivers is to write a list of requirements. There are many guides available online that go deep on how to create a checklist for endpoint security requirements that fits the needs of an individual or a company. Using the checklist along with a template that can be customized is the best way to make sure endpoint protection solutions end up performing up to the mark.
Real-time Threat Detection and Prevention
The first feature of any endpoint protection solution should be real-time threat detection and prevention. Through real-time detection, endpoint security solutions can guard devices against all types of cyberattacks. Modern cyberattacks are very different from before as most hacker groups are now able to launch multiple cyberattacks simultaneously. Each attack targets a different security vulnerability present within the network or on one of the devices that are part of the network. Endpoint security solutions should be able to first detect and then respond to multiple threats of various types at the same time. Some of the common threats endpoint security solutions should be able to handle with ease include malicious web downloads, email frauds, phishing attacks and software vulnerability exploits.
Note:
Sometimes, the feature is associated closely with threat intelligence where endpoint security solutions have to gather threat intelligence using multiple sources of data. Endpoint security solutions can then protect against malicious actors. Any good endpoint security solution must be able to analyze collected data and filter the unnecessary details to finally show the user real-time updates. This is also how threat detection programs can mitigate many cyber risks.Data Encryption

Full disk encryption is another useful feature where the endpoint security solution can encrypt the protected device, including the memory. To access the data, user credentials must be provided. Endpoint encryption is usually a separate component of the overall solution that offers enhanced security to all sensitive and valuable data. Unauthorized users cannot read the contents of the data because of the encryption. Endpoint encryption encompasses all methods to protect that, including encryption algorithms that can protect endpoints not just at the network level but also at the hardware and software level. Most modern endpoint encryption applications can perform tasks such as key management, authorization of devices and, at the core, encryption. Data encryption apps can back up and restore encryption keys for better security. The two most commonly used strategies include full disk encryption and file-only encryption.
Patch Management
Patch management refers to all the tools that repair security vulnerabilities within the system quickly. The vast majority of cyberattacks are successful because of outdated software and operating systems. Hackers usually target such devices because fewer resources are required. A company may have invested in cybersecurity to develop patches quickly, but if there is a delay in applying the patches to each device on the network, hackers get the upper hand. Patch management becomes even more important when an organization has enabled remote work for certain employees. With more people working from home, employee-owned devices must have adequate protection, which includes updated system software. The best patch management services can automate the process of collection of patches quickly and deliver the patches to all devices on the network.
Remote Wipe
Remote wipes remain one of the key features of any endpoint security solution. The ability to perform a remote wipe on part of network administrators or the owner of a device that needs protection comes in handy in many situations. Once properly configured, remote wipes only require a single command to delete or modify data on a device. The main usage of the remote wipe feature is when a device is lost or stolen. The owner of the device can simply use a remote wipe to erase all data on the lost device. Similarly, a change in ownership of a device (such as an employee leaving an organization and handing over company-owned devices) may also require a remote wipe feature to keep company data safe in a more convenient way.
How To Choose the Right Endpoint Protection Solution
Choosing the right endpoint protection solution is almost as important as deciding to use a security solution. The right endpoint protection solution would offer the standard set of tools and services such as malware protection, exploit protection, email threat protection, download protection, behavior analysis, application control, data loss prevention and endpoint detection and response. But there are more effective ways to choose the best endpoint protection solution. After all, endpoint protection forms just one of the many layers of security modern organizations need for a sufficient cybersecurity plan.
Identify Your Business Needs
Before even considering the product to sign up for, the initial step should be to understand the needs of the organization in question. Without properly identifying and evaluating current business needs, even the best endpoint security solution may end up performing at suboptimal levels. Hence, any endpoint protection solution must have the capacity required from a business. The same goes for scalability. The right endpoint solution will be able to serve a large user base from the start for big organizations. As far as scalability is concerned, businesses must first consider how fast the company is likely to grow in the near future. In that context, start-ups, small and medium businesses, along with enterprises, will have different criteria on what makes an endpoint protection solution viable.
Evaluate Vendors and Solutions
Evaluating vendors and solutions before deciding on a single endpoint security provider is also an important step in ensuring the right solution is chosen. There should be options available for trial runs. After measuring the performance of the endpoint security solution, a decision should be made about the possible purchase. The effectiveness of any endpoint protection solution is not based on a feature or spec list. Endpoint security vendors who can customize the final offering according to the needs of an organization are the most effective. Evaluating possible vendors and solutions has to be a continuous, careful and somewhat lengthy process. The best way to evaluate multiple vendors and associated solutions is to go with a gradual rollout instead of a big change in one go. Check if the vendor and the solution offered are compatible with the network and the software already installed. Problems showing up at this stage are a good sign to go with another vendor.
Consider Cost

To secure sensitive data from a company, some resources will have to be spent considering how indispensable endpoint security has become. But an organization still has to plan a budget. Choosing an endpoint protection solution is not just about purchasing the solution with the most features. Not giving proper attention to the budget leads to either not purchasing the right solution or purchasing a solution that can’t be implemented within the budget. This leads to security compromises. Depending on the exact requirements and size of the company, a standard endpoint security solution can cost as low as $17 per endpoint. But the low cost usually comes with the condition of using thousands of endpoints. For smaller businesses with 25 or fewer endpoints, the price usually goes up to $49.99 per year.
Evaluate Technical Capabilities
Without testing and evaluating the technical capabilities of an endpoint security product, security vulnerabilities can remain in place even after significant investment. To pick the best possible endpoint security solution, third-party testing results and a long history of reliable performance can show efficacy. A low number of false positives, lack of missed detections, minimal quality issues and downtime are some capabilities all good endpoint security solutions have. Endpoint security solutions that require a lot of technical capabilities on part of the employees are a problem that needs to be taken into consideration. If an endpoint security solution blocks breaches in the first place or prevents such problems, that should be considered sufficient as far as the evaluation phase goes.
Best Practices for Endpoint Protection
The vast majority of data breaches happen because something is lacking in the endpoint protection department. Organizations can reduce the impact of a data breach to a significant degree by applying some key best practices for endpoint security. With the help of the best practices for endpoint protection, the risks to any organization should be reduced, as well as the costs associated with data breaches in terms of reputational and financial damage.
Keep Software Up-to-Date

Keeping all software and operating systems up-to-date is perhaps the single most important aspect of having an effective endpoint protection strategy. Generating a plan for pushing out updates to endpoints in a timely manner first requires visibility. Each device connected to a network needs to be identified. After that, a decision can be made on whether the endpoint requires updates. Similar steps need to be taken for operating systems, security software and any installed apps. Determining if an endpoint will require more software for better protection is also paramount. Keeping software and operating systems updated automatically takes care of many types of malware and sometimes even helps in removing an already present malware item at an endpoint. Having patches and updates available regularly does not compensate for not making efforts to apply the said updates to endpoints.
Regularly Back-up Data
Even the best endpoint protection solution with all the advanced scan options and machine learning techniques to detect and thwart threats can malfunction. That is especially the case once an endpoint is no longer a part of the protected network. Examples include employees or individuals moving outside the vicinity of a company office. Devices can also be stolen or simply become lost. Missing devices can cause significant data loss to companies. Backing up data regularly ensures the company can recover quickly from such events. The best endpoint protection solutions should offer some backup options. Such backup data options should store information in data centers operated by the service for safekeeping. Securing data by storing in a remote place is only the first step as end users should have robust access to the data at the same time. Companies and individuals are bound to create vulnerabilities because of a lack of effort or oversight. In all of these cases, having a backup ensures there is no loss of data.
Educate Employees on Cybersecurity
Making sure users accessing endpoints and the resources available on the network don’t give rise to security issues starts with education. Even the safest environments and IT functionalities are not sufficient if users on the network read emails from strangers and download attachments. Employees not educated on cybersecurity regularly engage in behavior that opens up security holes and gives hackers opportunities to attack the company’s network infrastructure. Educating employees on cybersecurity can be as simple as going through a compliance training and basic security knowledge course. A company must invest in the regular and continuing education of employees on critical security issues. The IT staff can send out notifications and cybersecurity tips to users who may require more training. Simple instructions on how to delete or quarantine malicious files can prove sufficient.
Regularly Monitor and Review Endpoint Protection Solutions
The cybersecurity landscape is always changing. An endpoint protection solution that works today may not offer the same level of protection in the future. Any company that signs up for endpoint security protection should have programs in place to monitor and review the said solution from time to time for optimal protection. Cyber threats such as fileless attacks, phishing, ransomware and credential theft evolve at a pretty rapid pace. If an endpoint protection solution vendor is not trying to keep up with regular updates and feature addition, then that can lead to security vulnerabilities over the long term. Check with the endpoint protection solution vendor on the processes in place to ensure the product remains effective over a long period. Regularly going through review sites and cybersecurity forums can also help ensure the chosen endpoint protection solution is up to the mark at a time.
Why Is Endpoint Protection Important?
Any enterprise’s cybersecurity solutions depend critically on endpoint protection. With more activities shifting online, all businesses now generate some sort of data. Data is quickly becoming the most valuable asset a company can own. Losing sensitive or proprietary data can not only put a company out of business but may also come with legal ramifications. Other reasons why endpoint protection has become important include a higher number of endpoint devices leading to more vulnerabilities, more fluid security perimeters, higher returns for data breaches and an increase in remote work.
Does Endpoint Protection Protect Against All Cyber Threats?
Depending on the expertise employed and investment made, endpoint protection can protect against all cyber threats. But once data leaves the endpoint, hackers can launch cyberattacks as usual and steal sensitive data. Modern endpoint protection solutions protect against malware, ransomware and viruses.
Is Endpoint Protection Only for Businesses or Can Individuals Use It Too?
Endpoint protection is aimed toward business use. Individual online users usually make use of other tools for security computing devices. Endpoint security solutions are more suitable for an organization that requires the protection of a huge number of endpoints remotely. Businesses and companies that rely on employees having personal devices (and using devices outside the office as well) must provide the infrastructure for employees to connect to company networks and access assets quickly, either just outside the office or at home.

