Table of Contents
What is Malware
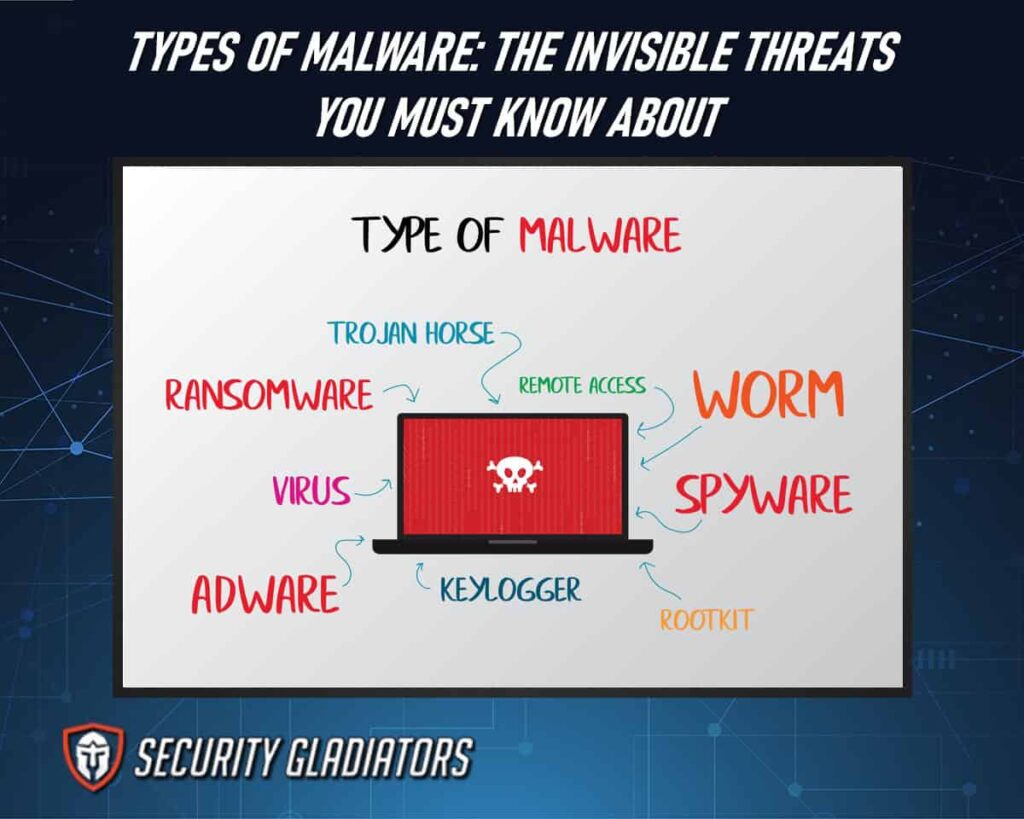
Malware, short for “malicious software,” is a broad term encompassing any software specifically designed to harm, disrupt, or gain unauthorized access to computer systems, networks, or individual devices. This category includes various types of harmful software, such as viruses, worms, Trojans, spyware, ransomware, adware, and more. Malware is typically distributed through deceptive means, like infected email attachments, compromised websites, or disguised as legitimate software. Once inside a system, malware can cause a range of damaging effects, from stealing sensitive data and financial information to corrupting files, disrupting system operations, and enabling remote control by cyber criminals. Understanding ways to remove malware is important for keeping your data protected. Protection against malware involves the use of malware removal software, regular system updates, cautious browsing habits, and careful downloading practices.
Common Types of Malware
Various types of malware pose significant threats to computer systems and networks, compromising their security and potentially causing extensive damage. There are several types of malware that individuals and organizations need to be aware of in order to protect themselves from potential attacks. They are:
1. Ransomware
One prevalent form of malicious software that has become increasingly common in recent years is ransomware. Ransomware is a type of malware designed to encrypt a victim’s files and demand payment for their release. It operates by infiltrating the target system through various means, such as email attachments, malicious websites, or software vulnerabilities. Once ransomware gains access to the system, it begins encrypting user files using strong encryption algorithms. This effectively locks the victim out of their own data until they pay a ransom to obtain the decryption key. The ransom demand is typically made in cryptocurrency, such as Bitcoin, to ensure anonymity for the cybercriminals behind the attack.

Ransomware attacks can have severe consequences for individuals and organizations alike. Victims may face significant financial losses if they choose to pay the ransom or invest resources in recovering their encrypted data independently. Furthermore, these attacks can disrupt critical services or operations for businesses and institutions, resulting in reputational damage and potential legal ramifications. To protect against ransomware attacks, users are advised to maintain regular backups of important files offline or on separate systems not connected to the internet. Additionally, keeping all software up-to-date with security patches and exercising caution when opening email attachments or clicking on suspicious links can help prevent infection.
2. Fileless Malware
Fileless malware, a stealthy and insidious form of cyber threat, infiltrates computer systems without leaving traces on the hard drive or relying on traditional executable files. These are sophisticated malware attacks difficult to detect and eradicate, as it operates entirely in memory and takes advantage of legitimate processes and tools already present in the targeted system. Unlike other types of malware that rely on files or software installations for their execution, fileless malware leverages scripting languages such as PowerShell or JavaScript to exploit vulnerabilities within existing applications. By doing so, it can easily bypass traditional antivirus solutions that primarily focus on scanning files.
To understand the impact of fileless malware, consider the following scenarios:
- A user clicks on a malicious link in an email or visits a compromised website. Without any visible indications, the fileless malware silently executes in the background.
- The malware then injects its code into a trusted process like Microsoft Word or Adobe Reader, effectively camouflaging itself among legitimate activities.
- It utilizes built-in functionalities of these trusted programs to carry out its malicious activities, such as downloading additional payloads from remote servers.
- Since no files are written to disk during this process, traditional security measures that scan for known signatures or monitor file activity may fail to detect this sophisticated attack.
3. Spyware
Spyware covertly monitors and gathers information from a targeted device or network without the user’s knowledge or consent. It is designed to infiltrate systems undetected and collect sensitive data such as passwords, credit card information, browsing habits, and personal files. Spyware operates by exploiting security vulnerabilities in a device’s operating system or popular applications. Once installed, it runs silently in the background, evading detection by traditional antivirus programs. One of the primary objectives of spyware is to steal sensitive data for various malicious purposes. This could include identity theft, financial fraud, corporate espionage, or even blackmail. By monitoring keystrokes or capturing screenshots, spyware can obtain valuable information that can be utilized for illicit activities. Additionally, some forms of spyware are capable of activating webcams and microphones without the user’s knowledge, allowing attackers to eavesdrop on conversations and invade privacy.
This is important:
To protect against spyware infections, it is crucial to maintain up-to-date security software that includes anti-spyware capabilities. Regularly updating operating systems and applications can help mitigate security vulnerabilities that spyware often exploits. Users should also exercise caution when downloading files or clicking on links from untrusted sources as these actions may lead to the unintentional installation of spyware.4. Adware
Adware displays advertisements on a user’s device or within their web browser in order to generate revenue for the developer. It is often bundled with free software and installed without the user’s knowledge or consent. Adware can be annoying and disruptive, as it interrupts the user’s browsing experience by displaying pop-up ads, redirecting web pages, or inserting ads into search results.
One of the main concerns with adware is its potential to compromise user privacy and security. Some adware programs collect personal information such as browsing habits, search queries, and even financial data to deliver targeted advertisements. This invasion of privacy raises ethical questions about consent and data protection. Additionally, some adware may also install other potentially unwanted programs or malicious downloads without the user’s knowledge, further exposing them to cyber threats. Users should be cautious when downloading free software from untrusted sources to avoid inadvertently installing adware and other potentially harmful programs.
5. Trojan
Trojans disguise themselves as legitimate programs to deceive users and gain unauthorized access to their systems. They are named after the Greek mythological story of the Trojan Horse, where Greeks used a wooden horse to enter the city of Troy undetected. Similarly, trojan horses appear harmless and useful but actually contain hidden malware that can harm user data and compromise system security. Trojans often spread through various means such as email attachments, software downloads from untrusted sources, or even exploiting vulnerabilities in legitimate software. Once installed on a system, they can perform various malicious activities without the user’s knowledge or consent. For example, trojans may create backdoors in the system that allow remote attackers to gain control over the infected computer. They can also steal sensitive information like passwords or financial details by logging keystrokes or capturing screenshots. In some cases, trojans may even download additional malware onto the compromised system, such as computer worms or ransomware.
To deceive users further, trojans often disguise themselves as popular and trusted software applications. This way, unsuspecting users are more likely to install them willingly without suspecting any malicious intent. They may also exploit social engineering techniques by presenting enticing offers or urgent requests for action to manipulate users into falling for their traps. Therefore, it is crucial for users to be cautious while downloading software from unknown sources and regularly update their security measures to protect against these types of malware disguised as legitimate programs.
6. Worms
Worms, a self-replicating form of malicious software, propagate through computer networks and exploit vulnerabilities to infect multiple systems without requiring user interaction or the need for a host program. Unlike viruses or Trojans, worms have the ability to spread on their own by taking advantage of security flaws in an operating system or network protocol. Once they gain access to a system, worms can create copies of themselves and send them to other vulnerable computers within the same network. This method allows worms to quickly and efficiently infect numerous systems, causing widespread damage. Worms are often disguised as harmless files or attachments that users unknowingly download or open. They can exploit various vulnerabilities such as outdated software, weak passwords, or unpatched security loopholes. Once inside a system, worms can perform a range of malicious activities including stealing sensitive information, deleting files, modifying data, or even hijacking control over the infected machine.
Note:
Removing malware spread by worms can be challenging due to their ability to hide within different parts of a computer’s file system and network infrastructure. To effectively remove these threats, it is crucial to use up-to-date antivirus software and regularly update operating systems and applications with the latest patches and security fixes. Additionally, employing strong passwords and practicing safe internet browsing habits can significantly reduce the risk of worm infections.7. Virus
A virus is a malicious program that attaches itself to legitimate files or programs and can execute its code when those files or programs are accessed or activated. Computer viruses are one of the most well-known types of malware due to their ability to cause significant damage and disruption. Unlike worms, which spread independently, viruses require human intervention for propagation. Once a virus infects a system, it can replicate itself by attaching to other files or programs on the same machine or even across an entire network. This characteristic allows viruses to quickly spread from one computer to another, making them particularly effective in carrying out large-scale attacks. The primary goal of computer viruses is often not just replication but rather causing harm with malicious intent. They can be programmed to delete files, corrupt data, steal sensitive information such as passwords or credit card details, or launch further attacks on other systems. Some viruses may remain dormant until triggered by specific conditions such as a particular date or user action. The complexity and versatility of computer viruses make them highly dangerous threats that require constant vigilance and robust security measures to prevent infection and minimize potential damage from malware attacks.
8. Rootkits
Rootkits, a form of covert malware, are designed to conceal their presence on a computer system by manipulating its operating system and evading detection by security software. Unlike other types of malware, rootkits aim to establish persistence within the targeted system, allowing unauthorized access and control without the knowledge of the user. By modifying core components of the operating system such as kernel functions or device drivers, rootkits can alter system behavior to suit their malicious intent. There are various types of rootkits that exploit different vulnerabilities in a computer system. User-mode rootkits operate at the application layer and can modify or replace key executable files or libraries to hide their activities from security software. Kernel-mode rootkits reside deeper within the operating system itself and can tamper with critical kernel structures to hijack control over all processes running on the machine.
Bootkit rootkits target even earlier stages of the startup process by infecting firmware or bootloader components. The primary goal of these manipulations is to maintain stealthiness and avoid detection by security software. Rootkits achieve this by employing advanced techniques like direct memory manipulation, hooking into API calls, or using encryption and obfuscation methods to disguise their presence. Furthermore, they often employ tactics like anti-forensic measures and cloaking mechanisms to evade analysis attempts. By concealing themselves effectively within a compromised system’s infrastructure, rootkits enable attackers to perform various malicious activities undetected. This could include unauthorized access and control over sensitive data or systems for espionage purposes or launching further attacks against other targets using compromised machines as part of a botnet network.
Additionally, some sophisticated rootkit variants are known for creating hidden backdoors that allow remote hackers easy access while remaining undetectable by traditional security measures. Detecting and combating rootkits requires specialized tools capable of detecting anomalies in both file systems and memory space while also analyzing network traffic for signs of malicious activity. Advanced intrusion detection systems and behavior-based anomaly detection algorithms can help identify rootkit activities by analyzing patterns of malicious traffic or abnormal system behavior. Regular system updates, strong access controls, and implementing secure coding practices can also help mitigate the risk of rootkit infections.
9. Keyloggers
Keyloggers are designed with the primary objective of capturing and recording keystrokes made by users on a compromised device. This covert activity allows cybercriminals to gain unauthorized access to sensitive information such as login credentials, credit card details, or any other confidential data entered via a keyboard. Keyloggers can be deployed through various methods, including phishing attacks, drive-by downloads, or even disguised as legitimate software or attachments. Once installed on a victim’s system, these malware programs operate silently in the background without the user’s knowledge. By monitoring and logging every keystroke made on the infected device, keyloggers enable hackers to gather valuable information that can be exploited for financial gain or further cyberattacks.
To emphasize the significance of this threat and shed light on its implications, it is essential to consider four key points:
- Data theft
- Covert operations
- Delivery methods
- Widespread impact
10. Bots/Botnets
Bots and botnets have become a pervasive threat in the digital landscape, wreaking havoc on individuals and organizations alike. A bot is a software application that performs automated tasks over the internet, often without the user’s knowledge or consent. These bots are typically used by cybercriminals to carry out malicious activities such as distributed denial-of-service (DDoS) attacks, spamming, identity theft, and data breaches. Botnets, on the other hand, are networks of infected computers controlled remotely by a central server known as a command-and-control (C&C) server.
Bots and botnets pose significant challenges to cybersecurity due to their ability to rapidly propagate and evade detection. They can infect devices through various means such as email attachments, compromised websites, or social engineering techniques. Once a device is infected with a botnet client or ‘bot,’ it becomes part of the larger network under the control of cybercriminals. This allows them to use these infected devices collectively to launch coordinated attacks or exploit vulnerabilities in target systems. To mitigate the risks associated with bots and botnets, individuals and organizations should implement robust security measures. This includes regularly updating antivirus software to detect and remove malware infections caused by bots or other types of malware like mobile malware or ransomware attacks.
Additionally, users should exercise caution when opening email attachments from unknown sources or clicking on suspicious links. Employing strong passwords and keeping operating systems up-to-date can also prevent unauthorized access via trojan horse attacks. As cybercriminals continue to develop hybrid malware that combines multiple attack techniques, it is crucial for cybersecurity professionals to stay vigilant and adapt their defense strategies accordingly.
11. Mobile Malware
Mobile malware refers to any type of malicious software specifically designed to target mobile devices. This includes various forms such as viruses, spyware, Trojans, adware, and ransomware that can compromise the security and privacy of users’ data. One common method used by attackers to distribute mobile malware is through malicious links or attachments in emails or text messages. Users may unknowingly click on these links or download infected files, leading to the installation of malware on their devices. Another technique employed by cybercriminals is phishing emails disguised as legitimate communications from trusted sources like banks or social media platforms. These emails often contain deceptive links that redirect users to fake websites where their personal information is compromised.
The rise in mobile malware highlights the importance of maintaining strong system security measures on mobile devices. Regularly updating operating systems and applications can help protect against known vulnerabilities that attackers exploit. Installing reputable antivirus software can also detect and remove potential threats from mobile devices. Additionally, users should exercise caution when downloading apps from third-party app stores or unfamiliar sources, as these are often hotspots for distributing malware-infected applications.
How Does Malware Work
Malware operates through various mechanisms depending on its type and purpose. When a user inadvertently downloads or executes the malicious software, it gains entry into the target system. Viruses attach themselves to legitimate programs and replicate by infecting other files, spreading throughout the system when those files are accessed. Worms are self-replicating and can spread across networks without needing a host file. Trojans disguise themselves as legitimate software to deceive users, allowing unauthorized access to the system. Ransomware encrypts the victim’s files, demanding a ransom for decryption. Spyware covertly monitors and collects sensitive information. Once inside a system, malware exploits vulnerabilities, modifies files, steals data, disrupts system operations, or enables remote control by cyber criminals. It can be challenging to detect and remove, making preventive measures and robust cybersecurity practices crucial for protection.
What Are the Dangers of Malware
Malware poses significant dangers to individuals, organizations, and even society as a whole. Some of the key risks and dangers associated with malware include:
Data Theft
Malware can steal sensitive information such as personal data, financial details, login credentials, and intellectual property. Stolen data can be used for identity theft, fraud, or sold on the dark web for profit.

Financial Loss
Ransomware, a type of malware, can encrypt files and demand a ransom for decryption. Paying the ransom does not guarantee data recovery, leading to financial losses for victims.
System Disruption
Malware can disrupt computer systems and networks, causing downtime for businesses, organizations, and individuals. This disruption can lead to a loss of productivity, revenue, and operational capability.
Unauthorized Access
Some malware, like backdoors and remote access Trojans, can grant cybercriminals unauthorized access to a compromised system, enabling them to monitor activities, steal data, or use the system for illegal activities.
Spread of Propagation
Certain malware, such as worms and viruses, can rapidly spread across networks, affecting multiple systems and devices, amplifying the damage.
Damage to Reputation
A malware attack can damage an individual’s or organization’s reputation if sensitive data or embarrassing information is exposed, leading to a loss of trust among customers or partners.
How to prevent Malware
Here are some essential steps you can take to reduce the risk of malware infections:
Use Antivirus Software
Install reputable antivirus or anti-malware software on all devices, including computers, smartphones, and tablets. Keep the software updated to ensure it can detect and block the latest threats.

Keep Software Updated
Regularly update operating systems, web browsers, and other software applications. Software updates often include security patches that address known vulnerabilities, making it harder for malware to exploit them.
Be Cautious with Email
Avoid opening email attachments or clicking on links from unknown or suspicious sources. Malware often spreads through phishing emails designed to trick recipients into downloading infected files or visiting malicious websites.
Use Strong Passwords
Create strong, unique passwords for all your online accounts and change them regularly. Enable multi-factor authentication (MFA) whenever possible to add an extra layer of security.
Be Wary of Downloads
Only download software and files from trusted sources and official websites. Be cautious with freeware and cracked software, as they may contain hidden malware.
Enable Firewall Protection
Activate the built-in firewall on your devices and network router. Firewalls act as a barrier between your devices and the internet, blocking unauthorized access and potential malware.
Frequently Asked Questions
What Are the Common Signs and Symptoms of a Malware Infection?
Common signs and symptoms of malware infection include slow computer performance, frequent system crashes or freezes, unexpected pop-ups, changes in browser settings, and the presence of unfamiliar programs. These indicators suggest the need for immediate malware detection and removal.
How Can Malware Be Spread and Transmitted To Other Devices or Networks?
Malware can be spread through various means including email attachments, infected websites, file downloads, and removable media. It can also propagate across networks via vulnerabilities in software or by exploiting weak passwords.
Can Malware Affect the Performance and Speed of a Computer or Mobile Device?
Malware can significantly impact the performance and speed of computers or mobile devices. It can consume system resources, slow down processes, cause crashes, and degrade overall functionality, resulting in a decrease in efficiency and user experience.
Are There Any Specific Industries or Sectors That Are More Susceptible to Malware Attacks?
Certain industries or sectors are more susceptible to malware attacks, such as the financial sector, the healthcare industry, and government agencies. These industries possess valuable data and are often targeted due to their attractiveness to cyber criminals.
Conclusion
Understanding the various types of malware is essential in order to protect computer systems and networks from potential threats. The dangers posed by malware are significant and can result in financial loss, identity theft, or even damage to critical infrastructure. Malicious actors exploit vulnerabilities in software or trick users into downloading malicious files or visiting compromised websites. Once installed on a system, malware spread malicious code in different forms to steal sensitive data, disrupt operations, or cause irreversible damage. Combating malware requires a multi-faceted approach that combines technological solutions with user awareness and education. As new forms of malware continue to emerge and evolve at an alarming rate, staying informed about the latest threats is paramount.

